What Is Attack Surface Management Guide For Organizations Techtarget

Qualys Guide For Attack Surface Management Qualys Inc Attack surface management (asm) calls on enterprises to continuously scan and identify possible exposures, recommend remediation steps and monitor an organization's it environment for emerging threats. A comprehensive attack surface management program helps an organization protect its network assets. learn what to look for before implementing asm.
Qualys Guide For Attack Surface Management Qualys Inc Discover what attack surface management is, how it enhances your security posture, and how to protect your digital assets with microsoft security. What is attack surface management? attack surface management (asm) is the continuous discovery, analysis, prioritization, remediation and monitoring of the cybersecurity vulnerabilities and potential attack vectors that make up an organization’s attack surface. Upcoming research shows organizations are working to reduce their attack surfaces. check out ways to manage them, which include zero trust and other options. What is attack surface management? attack surface management is the continuous discovery, monitoring, evaluation, prioritization and remediation of attack vectors within an organization's it infrastructure.
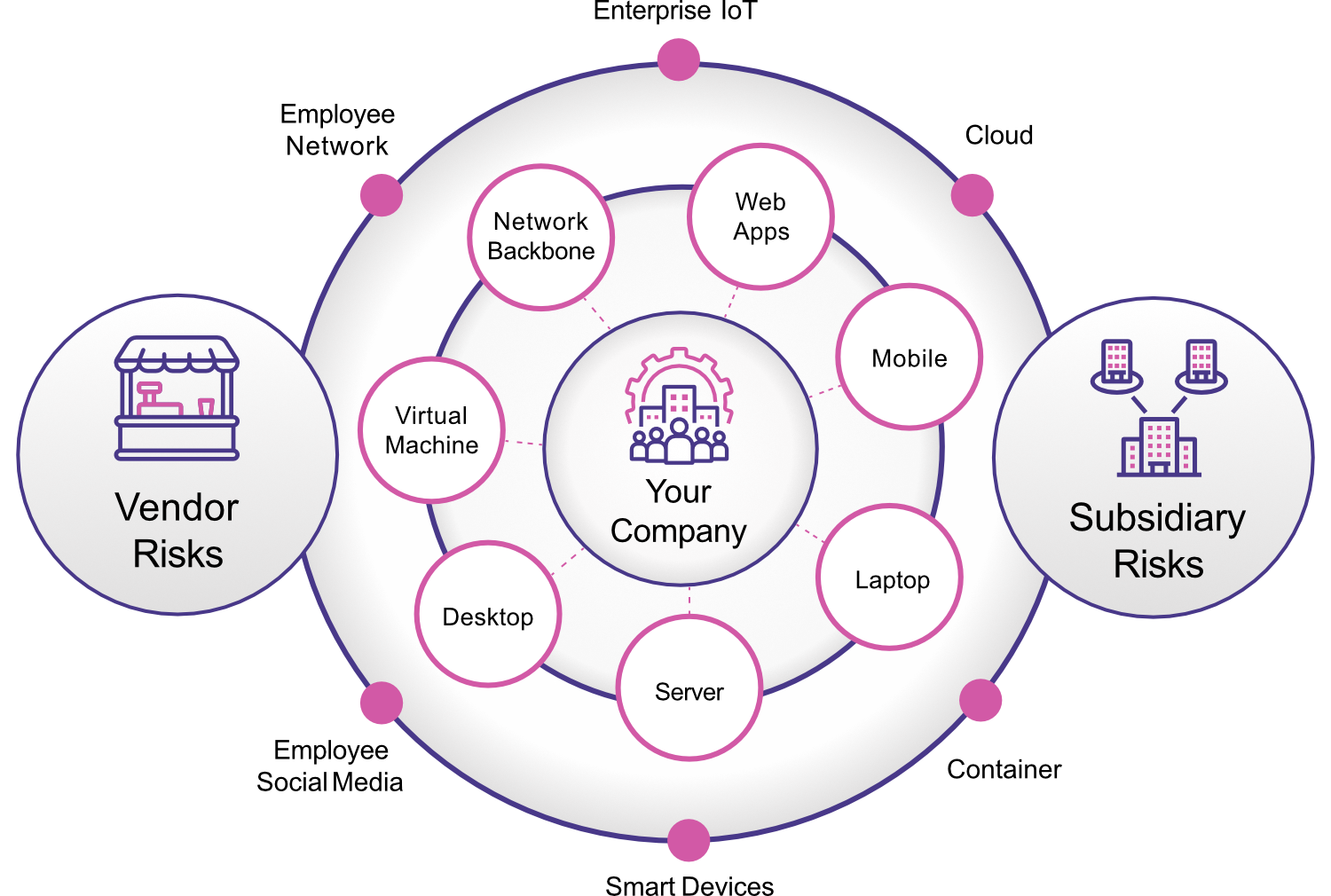
Attack Surface Management Complete Visibility Threat Protection Upcoming research shows organizations are working to reduce their attack surfaces. check out ways to manage them, which include zero trust and other options. What is attack surface management? attack surface management is the continuous discovery, monitoring, evaluation, prioritization and remediation of attack vectors within an organization's it infrastructure. Attack surface management is essential to reducing risk across hybrid environments. attack surface management helps organizations find, catalog, prioritize, and monitor all potential entry points (attack vectors) across cloud, on premises, and saas environments. Learn how attack surface management (asm) enhances cybersecurity by providing visibility into all potential entry points, enabling proactive defense against vulnerabilities in complex digital landscapes. This guide breaks down what asm is, how its lifecycle works, the types of attack surfaces organizations must monitor, and how to build a program that keeps pace with an ever expanding digital footprint. Attack surface management finds exposed cloud assets before attackers do. learn how asm differs from cspm and vulnerability management, with sql examples.

Attack Surface Management A Cybersecurity Essential Netquest Attack surface management is essential to reducing risk across hybrid environments. attack surface management helps organizations find, catalog, prioritize, and monitor all potential entry points (attack vectors) across cloud, on premises, and saas environments. Learn how attack surface management (asm) enhances cybersecurity by providing visibility into all potential entry points, enabling proactive defense against vulnerabilities in complex digital landscapes. This guide breaks down what asm is, how its lifecycle works, the types of attack surfaces organizations must monitor, and how to build a program that keeps pace with an ever expanding digital footprint. Attack surface management finds exposed cloud assets before attackers do. learn how asm differs from cspm and vulnerability management, with sql examples.

Mastering Attack Surface Management This guide breaks down what asm is, how its lifecycle works, the types of attack surfaces organizations must monitor, and how to build a program that keeps pace with an ever expanding digital footprint. Attack surface management finds exposed cloud assets before attackers do. learn how asm differs from cspm and vulnerability management, with sql examples.
Comments are closed.