What Is Attack Path Analysis
Attack Path Analysis Technology Radar Thoughtworks What is attack path analysis? attack path analysis is a method of cybersecurity that elicits and evaluates the possibilities of how attackers might exploit existing vulnerabilities within a network to gain unauthorized access to critical systems or sensitive data. Attack path analysis (apa) in cybersecurity is a way of identifying the potential routes attackers could exploit to infiltrate your network or system.
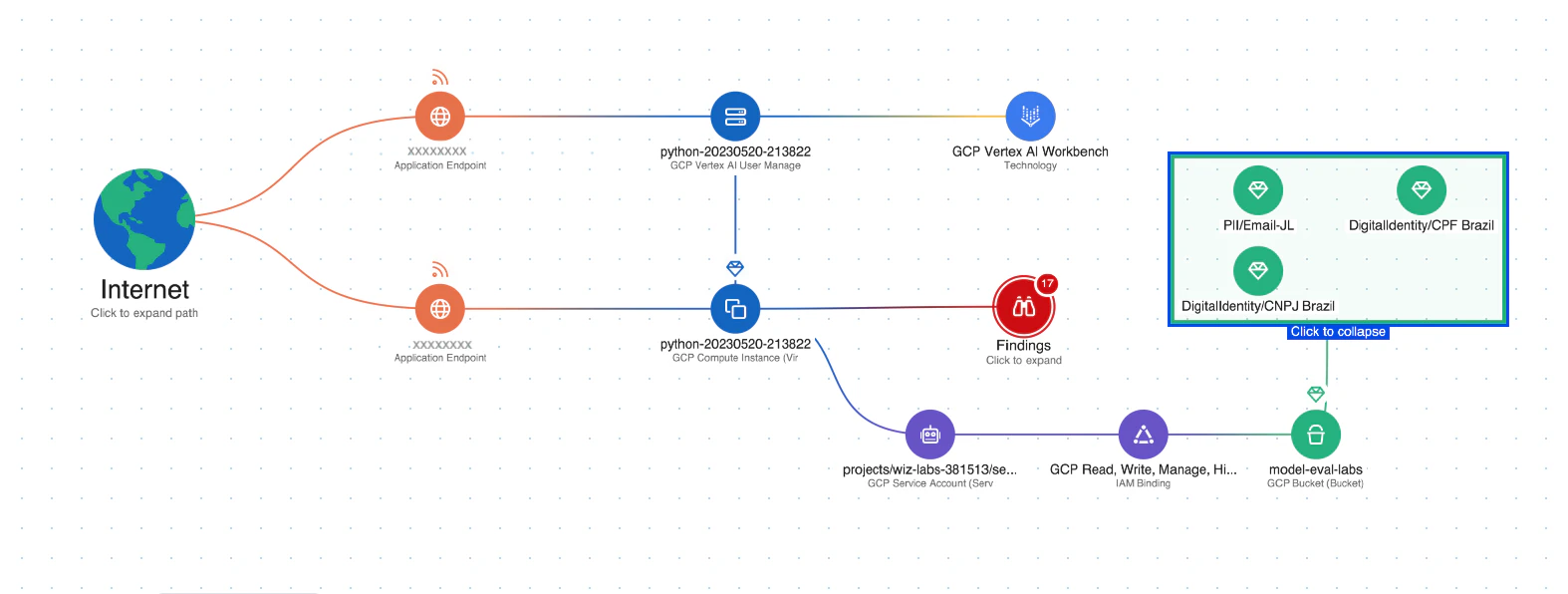
What Is Attack Path Analysis Wiz Attack path analysis is the practice of identifying and evaluating the ways an attacker could move through your environment to reach sensitive systems. What is attack path analysis? attack path analysis (apa) is a security methodology that identifies and maps the routes attackers could use to move through your environment and reach critical assets. Attack path analysis (apa) is a cybersecurity technique that helps security teams visualize and mitigate potential attack routes before adversaries can exploit them. Attack path analysis (apa) is a cybersecurity technique used to proactively identify, visualize, and analyze all the possible routes an attacker could take through an it environment to reach critical assets.

Attack Path Analysis Redseal Attack path analysis (apa) is a cybersecurity technique that helps security teams visualize and mitigate potential attack routes before adversaries can exploit them. Attack path analysis (apa) is a cybersecurity technique used to proactively identify, visualize, and analyze all the possible routes an attacker could take through an it environment to reach critical assets. Attack path analysis is a simplified way of graphically visualizing the avenues bad actors can use to navigate your on prem and cloud environments. attackers can leverage these different “paths” to access sensitive information and, unsurprisingly, exploit a vulnerable configuration or resource. Attack path analysis (apa) is a cybersecurity method used to identify and map potential attack routes that threat actors could exploit to infiltrate systems or networks by targeting vulnerabilities. Learn how to identify and remediate attack paths in microsoft defender for cloud and enhance the security of your environment. Path analysis turns attack models into computable paths. learn how to enumerate reachability, identify chokepoints, score impact, and map evidence and controls, including ot and cyber physical constraints.
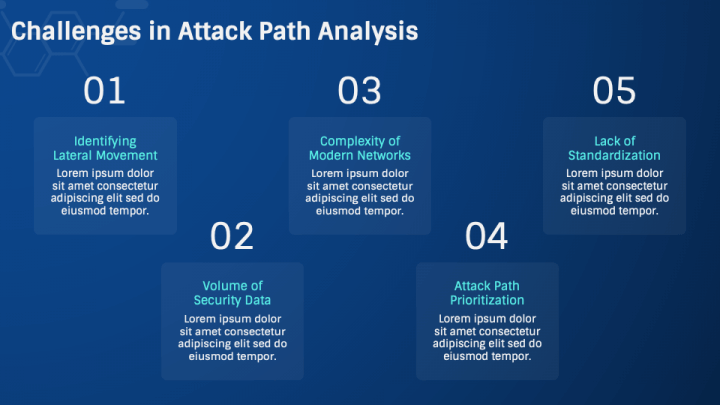
Attack Path Analysis Powerpoint And Google Slides Template Ppt Slides Attack path analysis is a simplified way of graphically visualizing the avenues bad actors can use to navigate your on prem and cloud environments. attackers can leverage these different “paths” to access sensitive information and, unsurprisingly, exploit a vulnerable configuration or resource. Attack path analysis (apa) is a cybersecurity method used to identify and map potential attack routes that threat actors could exploit to infiltrate systems or networks by targeting vulnerabilities. Learn how to identify and remediate attack paths in microsoft defender for cloud and enhance the security of your environment. Path analysis turns attack models into computable paths. learn how to enumerate reachability, identify chokepoints, score impact, and map evidence and controls, including ot and cyber physical constraints.
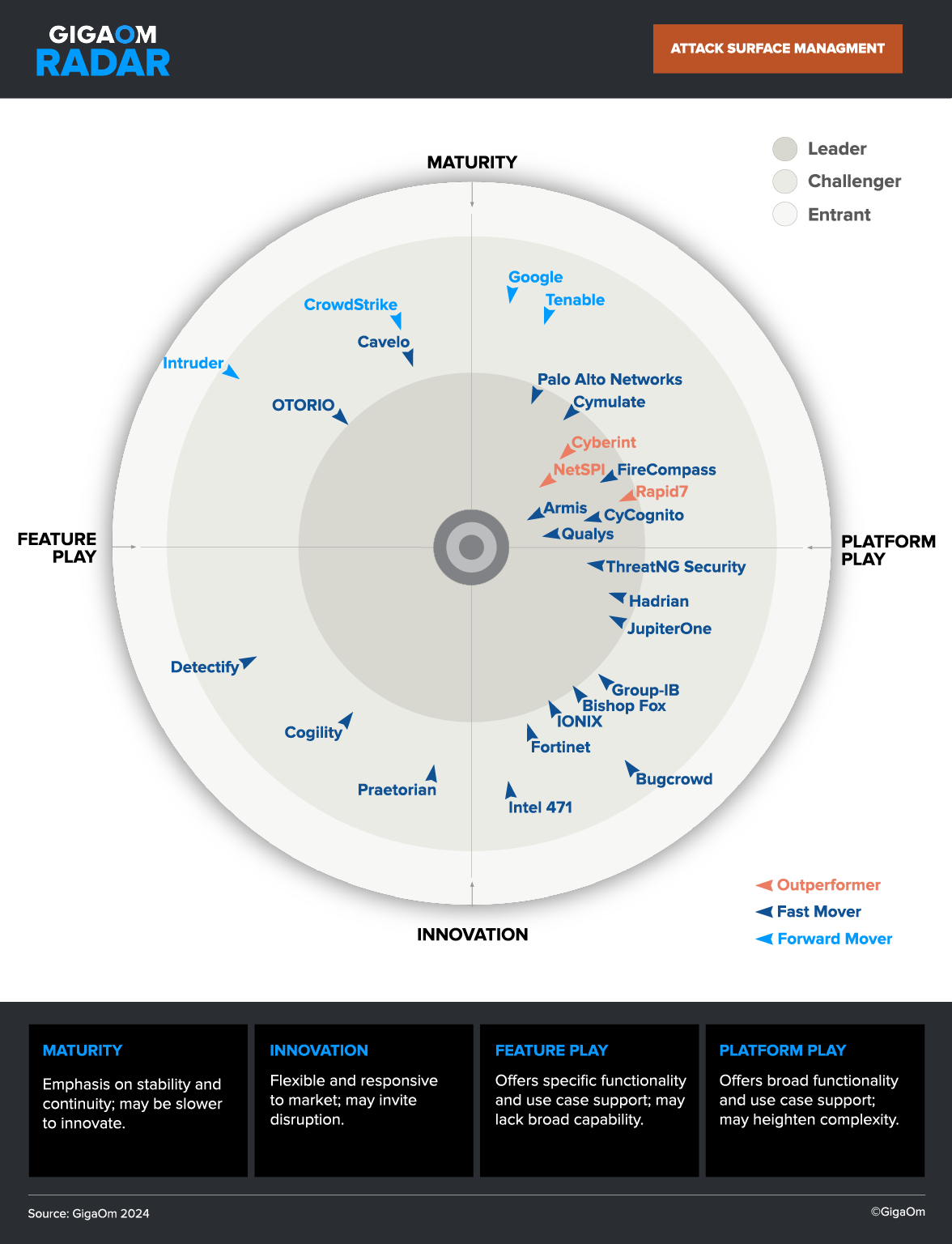
Attack Path Analysis How It Works Use Cases Best Practices Cycognito Learn how to identify and remediate attack paths in microsoft defender for cloud and enhance the security of your environment. Path analysis turns attack models into computable paths. learn how to enumerate reachability, identify chokepoints, score impact, and map evidence and controls, including ot and cyber physical constraints.
Comments are closed.