What Is Application Vulnerability Management Next Lvl Programming
What Is Application Vulnerability Management Wiz This in depth guide examines what is application security vulnerability management, including the need, common risks, key components, best practices, and how sentinelone fortifies app protection. This guide explains how to integrate avm effectively within your sdlc. appsec leaders rely on application vulnerability management (avm) to integrate security within the sdlc, enforce consistent policies, and achieve faster remediation cycles while ensuring risk visibility and compliance.

Application Vulnerability Management Ibm Concert What is application vulnerability management? application vulnerability management is a continuous process of discovering, assessing, prioritizing, and remediating security weaknesses in your software code, apis, and dependencies across the entire development lifecycle. Vulnerability management is the process of identifying, assessing, remediating and mitigating security vulnerabilities in software and computer systems. it's a critical part of managing cybersecurity risk in it environments, as vulnerabilities that are not found and fixed can expose an organization to damaging cyberattacks and data breaches. Vulnerability management is a continuous, proactive, and often automated process that keeps your computer systems, networks, and enterprise applications safe from cyberattacks and data breaches. as such, it is an important part of an overall security program. Application security posture management (aspm) enhances vulnerability management by providing a centralized view that correlates security data across the software lifecycle, allowing teams to prioritize the most critical risks based on business context and actual reachability.

Rh Isac Best Practices For Application Vulnerability Management Rh Isac Vulnerability management is a continuous, proactive, and often automated process that keeps your computer systems, networks, and enterprise applications safe from cyberattacks and data breaches. as such, it is an important part of an overall security program. Application security posture management (aspm) enhances vulnerability management by providing a centralized view that correlates security data across the software lifecycle, allowing teams to prioritize the most critical risks based on business context and actual reachability. In this informative video, we will guide you through the essential steps of vulnerability management in the realm of cybersecurity. this process is critical for organizations aiming to. To build resilience in an increasingly hostile digital environment, organizations must adopt risk based vulnerability management—a modern approach that enables teams to focus on vulnerabilities that present the most significant risk to business operations. Learn what vulnerability management is, what steps are involved in the process, and how you can implement a robust vulnerability management program that leverages automation. Application vulnerability management is all about identifying, assessing, and fixing security flaws in your apps. with cyber threats growing, this process is essential for protecting sensitive data and keeping your business running smoothly.
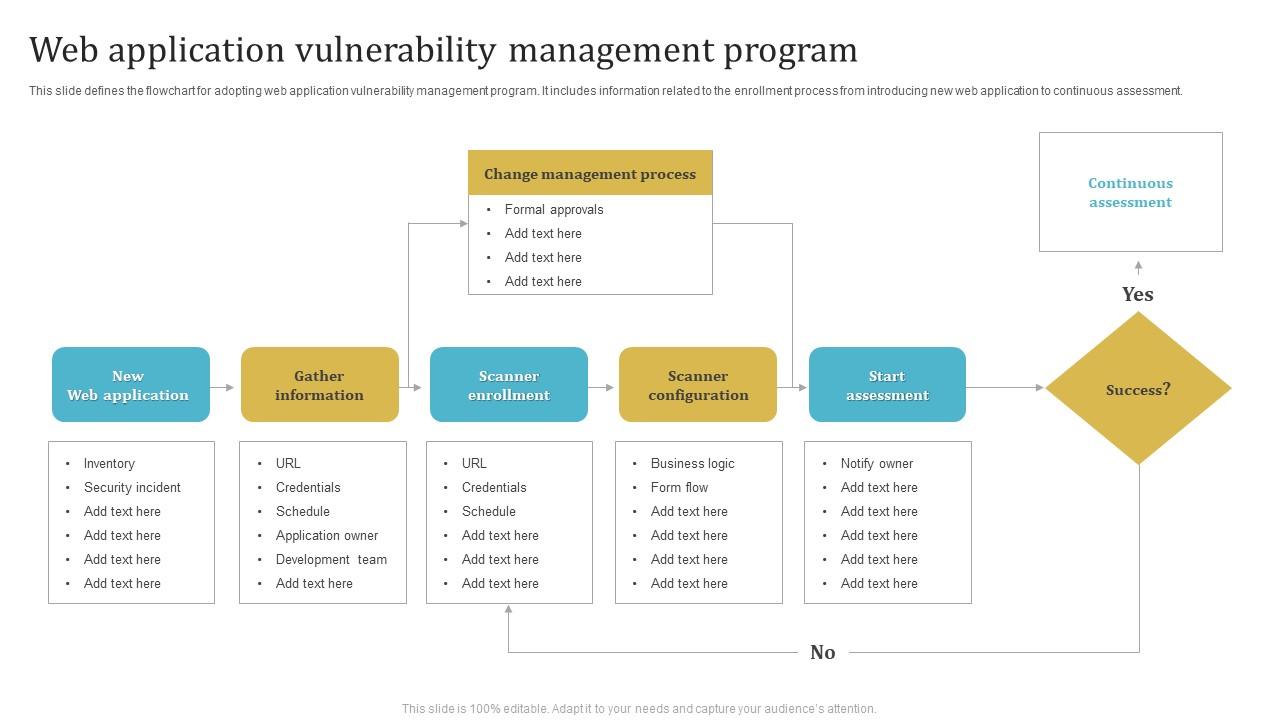
Web Application Vulnerability Management Program Ppt Powerpoint In this informative video, we will guide you through the essential steps of vulnerability management in the realm of cybersecurity. this process is critical for organizations aiming to. To build resilience in an increasingly hostile digital environment, organizations must adopt risk based vulnerability management—a modern approach that enables teams to focus on vulnerabilities that present the most significant risk to business operations. Learn what vulnerability management is, what steps are involved in the process, and how you can implement a robust vulnerability management program that leverages automation. Application vulnerability management is all about identifying, assessing, and fixing security flaws in your apps. with cyber threats growing, this process is essential for protecting sensitive data and keeping your business running smoothly.
Comments are closed.