What Is A Zero Day Threat

What Is A Zero Day Threat Geeky Gadgets A zero day attack occurs when adversaries exploit a previously unknown vulnerability in a live environment to compromise a system, steal confidential data, or undermine its infrastructure. A zero day (also known as a 0 day) is a vulnerability or security hole in a computer system unknown to its developers or anyone capable of mitigating it. [1] until the vulnerability is remedied, threat actors can exploit it in a zero day exploit, or zero day attack. [2][3] the term "zero day" originally referred to the number of days since a new piece of software was released to the public, so.
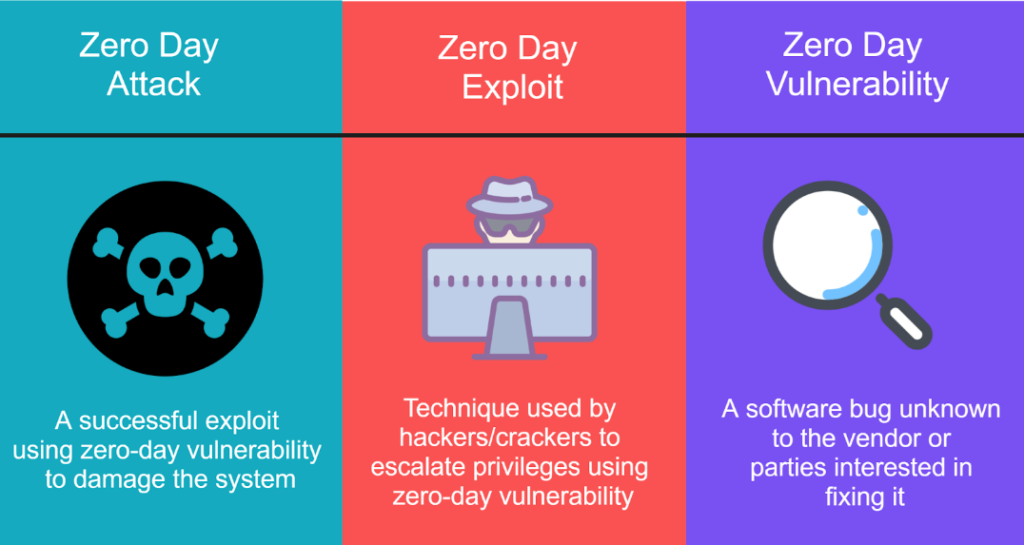
Understanding Zero Day Vulnerability Exploits A zero day attack begins with a hacker discovering a zero day vulnerability, which is an error in code or software that the target has yet to discover. the attacker then works on a zero day exploit, a method of attack, that they can use to take advantage of the existing vulnerability. What is zero day attack or threat? a zero day attack is a cyberattack that exploits an unknown vulnerability in your computer or mobile device’s software or hardware before the vendor has released a fix. A zero day exploit is a cyberattack vector or technique that takes advantage of an unknown or unaddressed security flaw in computer software, hardware or firmware. A zero day exploit, also called a zero day threat or attack, takes advantage of a security vulnerability that does not have a fix in place.

Zero Day Attacks Understanding The Hidden Threat A zero day exploit is a cyberattack vector or technique that takes advantage of an unknown or unaddressed security flaw in computer software, hardware or firmware. A zero day exploit, also called a zero day threat or attack, takes advantage of a security vulnerability that does not have a fix in place. A zero day exploit is one of the most dangerous tools in a threat actor’s arsenal. it allows attackers to exploit a software vulnerability before the affected vendor discovers it—and before any fix exists. A zero day exploit is a form of attack whereby the attacker takes advantage of an undiscovered hole in a software program, a piece of hardware, or firmware. nowadays advanced technological progress is embedded in people’s lives and as a result, cyber security has become one of the biggest issues in society for individuals, companies, and nations. small and large threats are regarded as quite. A zero day attack targets an undiscovered software vulnerability before developers can patch it, making organizations unaware of the flaw until after an attack has already occurred. Zero day attacks exploit unidentified vulnerabilities in your systems, rendering you helpless. zero day exploits do not signal themselves like other traditional threats do. they appear with no notice at all, and security teams will have zero seconds to patch and prepare.

What Is Zero Day Threat Simplify It Solutions A zero day exploit is one of the most dangerous tools in a threat actor’s arsenal. it allows attackers to exploit a software vulnerability before the affected vendor discovers it—and before any fix exists. A zero day exploit is a form of attack whereby the attacker takes advantage of an undiscovered hole in a software program, a piece of hardware, or firmware. nowadays advanced technological progress is embedded in people’s lives and as a result, cyber security has become one of the biggest issues in society for individuals, companies, and nations. small and large threats are regarded as quite. A zero day attack targets an undiscovered software vulnerability before developers can patch it, making organizations unaware of the flaw until after an attack has already occurred. Zero day attacks exploit unidentified vulnerabilities in your systems, rendering you helpless. zero day exploits do not signal themselves like other traditional threats do. they appear with no notice at all, and security teams will have zero seconds to patch and prepare.

Decoding Zero Day Vulnerabilities Unmasking Stealthy Threats A zero day attack targets an undiscovered software vulnerability before developers can patch it, making organizations unaware of the flaw until after an attack has already occurred. Zero day attacks exploit unidentified vulnerabilities in your systems, rendering you helpless. zero day exploits do not signal themselves like other traditional threats do. they appear with no notice at all, and security teams will have zero seconds to patch and prepare.
Comments are closed.