What Is A Zero Day Exploit Simply Explained

5 Ways To Protect Yourself From A Zero Day Exploit Zero day exploit refers to a security vulnerability that is unknown to the software vendor or the public, allowing attackers to exploit it before it can be patched. A zero day exploit is the technique or tactic a malicious actor uses to leverage the vulnerability to attack a system. a zero day attack occurs when a hacker releases malware to exploit the software vulnerability before the software developer has patched the flaw.
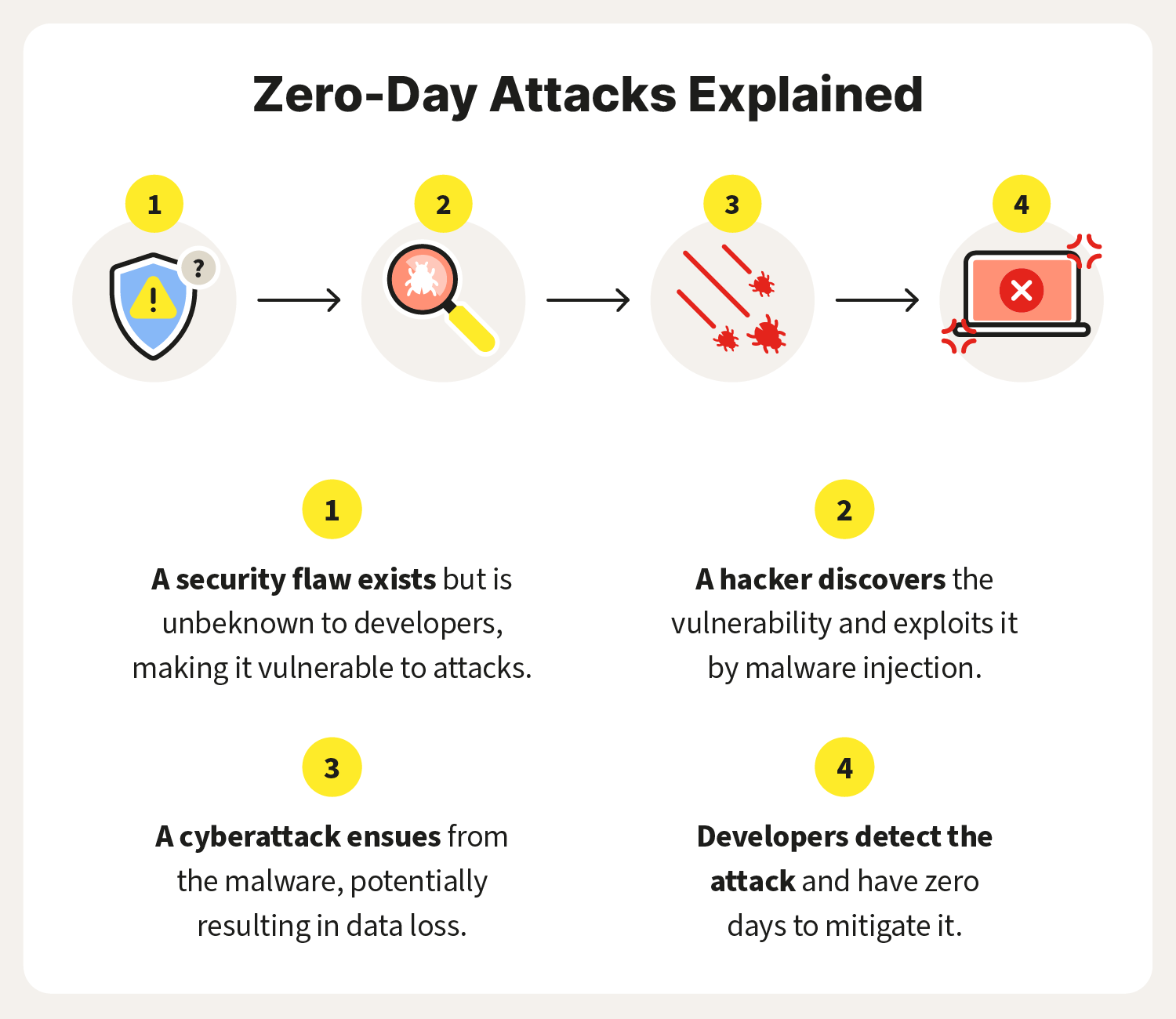
What Is A Zero Day Exploit Definition And Prevention Tips 41 Off A zero day exploit is a cyberattack vector or technique that takes advantage of an unknown or unaddressed security flaw in computer software, hardware or firmware. With no fix or patch available, attackers can exploit it immediately, posing a serious security threat. a zero day exploit is one of the most dangerous methods of cyber attack. it targets an unpatched vulnerability, leaving systems highly susceptible to exploitation. What is a zero day exploit? a zero day exploit (also called a zero day threat) is an attack that takes advantage of a security vulnerability that does not have a fix in place. What is a zero day exploit and why is it so dangerous? learn what a zero day exploit is, why it poses such a severe risk, and how organizations can detect and mitigate zero day attacks using proactive threat intelligence.
Preventing Zero Day Exploits And Attacks Scan On Computer What is a zero day exploit? a zero day exploit (also called a zero day threat) is an attack that takes advantage of a security vulnerability that does not have a fix in place. What is a zero day exploit and why is it so dangerous? learn what a zero day exploit is, why it poses such a severe risk, and how organizations can detect and mitigate zero day attacks using proactive threat intelligence. A zero day exploit is a method or code specifically engineered to trigger the underlying vulnerability. it enables attackers to take desired actions—such as executing commands, escalating privileges, or bypassing authentication—by exploiting the flaw. A zero day exploit is attack code that targets a previously unknown software vulnerability. the name comes from the fact that vendors have had zero days to develop and release a fix. In simple terms, a zero day exploit is a type of cyber attack that takes advantage of a security flaw in software that is unknown to the developers or the public. because the flaw is not yet known, there are no patches or fixes available, making it a highly effective and dangerous form of attack. A zero day exploit is how an attacker actually uses a zero day vulnerability to break into a system. if the vulnerability is the hidden door, the exploit is the key—or the set of instructions—that lets someone walk through it.

What Is A Zero Day Exploit Askcybersecurity A zero day exploit is a method or code specifically engineered to trigger the underlying vulnerability. it enables attackers to take desired actions—such as executing commands, escalating privileges, or bypassing authentication—by exploiting the flaw. A zero day exploit is attack code that targets a previously unknown software vulnerability. the name comes from the fact that vendors have had zero days to develop and release a fix. In simple terms, a zero day exploit is a type of cyber attack that takes advantage of a security flaw in software that is unknown to the developers or the public. because the flaw is not yet known, there are no patches or fixes available, making it a highly effective and dangerous form of attack. A zero day exploit is how an attacker actually uses a zero day vulnerability to break into a system. if the vulnerability is the hidden door, the exploit is the key—or the set of instructions—that lets someone walk through it.

Understanding Zero Day Exploit What S That And How To Prevent It In simple terms, a zero day exploit is a type of cyber attack that takes advantage of a security flaw in software that is unknown to the developers or the public. because the flaw is not yet known, there are no patches or fixes available, making it a highly effective and dangerous form of attack. A zero day exploit is how an attacker actually uses a zero day vulnerability to break into a system. if the vulnerability is the hidden door, the exploit is the key—or the set of instructions—that lets someone walk through it.

What Is A Zero Day Exploit And Why Are They Dangerous
Comments are closed.