What Is A Zero Day Attack
Zero Day Attack Definition Types And Examples A zero day attack occurs when adversaries exploit a previously unknown vulnerability in a live environment to compromise a system, steal confidential data, or undermine its infrastructure. A zero day vulnerability is a security hole in a computer system unknown to its owners, developers or anyone capable of mitigating it. until the vulnerability is remedied, threat actors can exploit it in a zero day attack, which is a severe threat that can disrupt, install malware, or exfiltrate data.

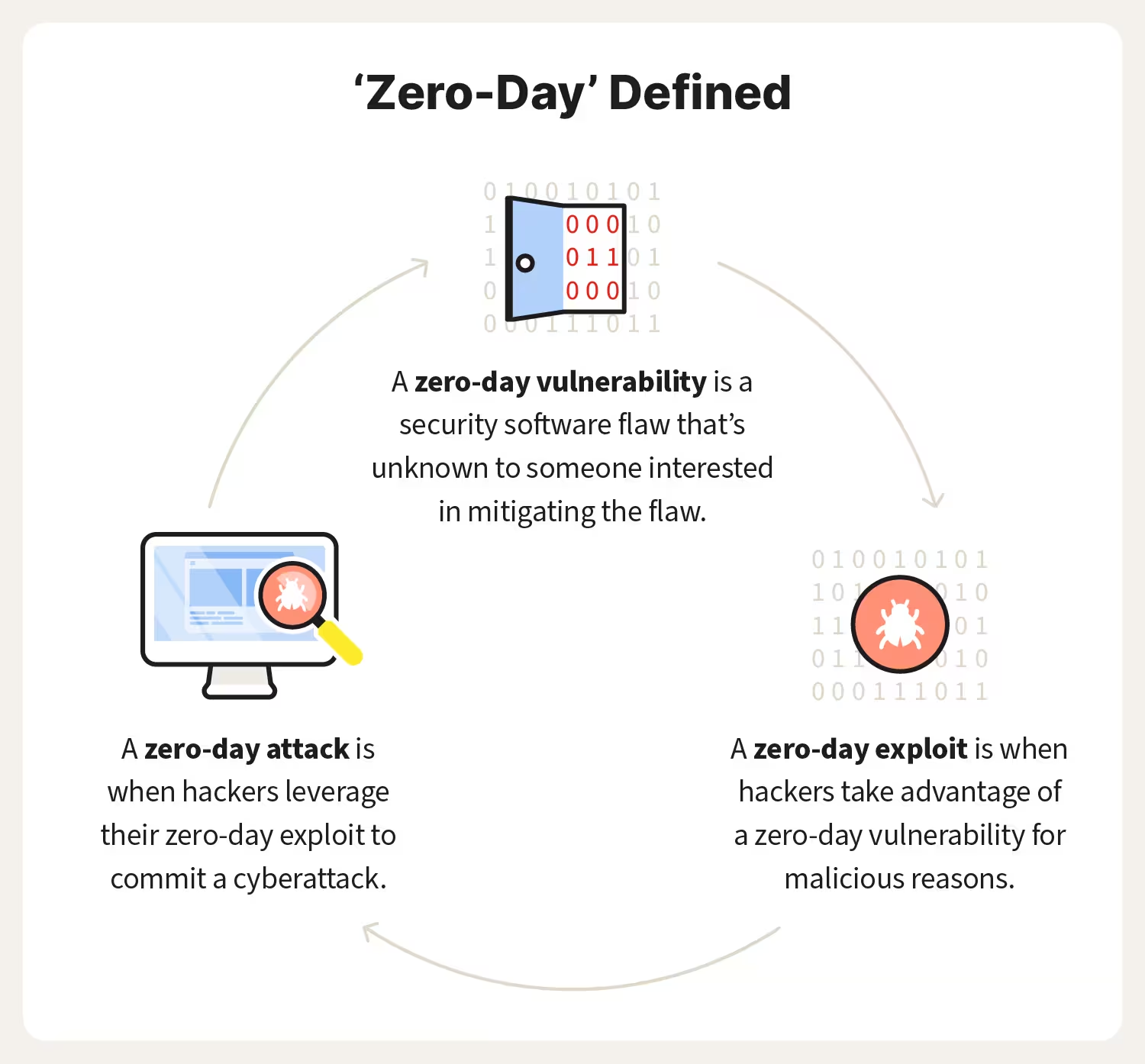
Zero Day Attack Iaspoint A zero day attack begins with a hacker discovering a zero day vulnerability, which is an error in code or software that the target has yet to discover. the attacker then works on a zero day exploit, a method of attack, that they can use to take advantage of the existing vulnerability. A zero day exploit is a form of attack whereby the attacker takes advantage of an undiscovered hole in a software program, a piece of hardware, or firmware. nowadays advanced technological progress is embedded in people’s lives and as a result, cyber security has become one of the biggest issues in society for individuals, companies, and nations. small and large threats are regarded as quite. A zero‑day attack happens when hackers exploit a software vulnerability before the developer has created or released a patch. the name “zero‑day” reflects that developers have zero days to fix the flaw once attackers begin exploiting it. A zero day vulnerability is a flaw in software or hardware that the vendor doesn’t yet know about. once an attacker discovers and weaponizes it, the vulnerability becomes a zero day exploit.
What S A Zero Day Attack A Diagram Of The Vulnerability Timeline A zero‑day attack happens when hackers exploit a software vulnerability before the developer has created or released a patch. the name “zero‑day” reflects that developers have zero days to fix the flaw once attackers begin exploiting it. A zero day vulnerability is a flaw in software or hardware that the vendor doesn’t yet know about. once an attacker discovers and weaponizes it, the vulnerability becomes a zero day exploit. A zero day exploit is a cyberattack vector or technique that takes advantage of an unknown or unaddressed security flaw in computer software, hardware or firmware. A zero day exploit is a technique or tactic that leverages an unknown software vulnerability to attack a system. learn about the difference between zero day vulnerability, exploit, and attack, and see some recent examples of zero day attacks and how to protect against them. A zero day (or 0 day) attack happens when a hacker finds and exploits a vulnerability before the developers or owners of the system have time to fix the problem, or in some cases, even become aware of it. A zero day attack is one that is discovered while it is already in progress, meaning a security team has “zero days” to prepare or remediate the vector through which the attacker gained entry.
-1.png?width=600&height=333&name=Zero-day attack Vs (1)-1.png)
5 Security Experts Share Best Practices To Prevent Zero Day Attacks A zero day exploit is a cyberattack vector or technique that takes advantage of an unknown or unaddressed security flaw in computer software, hardware or firmware. A zero day exploit is a technique or tactic that leverages an unknown software vulnerability to attack a system. learn about the difference between zero day vulnerability, exploit, and attack, and see some recent examples of zero day attacks and how to protect against them. A zero day (or 0 day) attack happens when a hacker finds and exploits a vulnerability before the developers or owners of the system have time to fix the problem, or in some cases, even become aware of it. A zero day attack is one that is discovered while it is already in progress, meaning a security team has “zero days” to prepare or remediate the vector through which the attacker gained entry.
Zero Day Attack Google Chrome Vulnerability Upsc A zero day (or 0 day) attack happens when a hacker finds and exploits a vulnerability before the developers or owners of the system have time to fix the problem, or in some cases, even become aware of it. A zero day attack is one that is discovered while it is already in progress, meaning a security team has “zero days” to prepare or remediate the vector through which the attacker gained entry.
Comments are closed.