What Does Zero Trust Security Architecture Mean
What Does Zero Trust Security Architecture Mean Zero trust architecture (zta) is an enterprise’s cybersecurity plan that utilizes zero trust concepts and encompasses component relationships, workflow planning, and access policies.” nine out of ten security leaders agree zero trust is key to strengthening cyber defenses. What does zero trust architecture mean? zero trust architecture (zta) is a security framework that verifies every access request to ensure only authorized users and devices can enter your network, view sensitive data, and use business resources.

Zero Trust Architecture Adoption For Enterprise Security In 2025 Zero trust is a security model where the core architecture assumes no entity, inside or outside the network, is trustworthy by default and requires strict verification. What it is: zero trust architecture (zta) is a cybersecurity framework built on the principle of “never trust, always verify.” it assumes every user, device, and application is untrusted until verified, enforcing strict identity, access, and policy controls. Zero trust security, also known as a zero trust architecture or perimeterless security, assumes no one and no device or application is universally trusted, whether inside or outside the network. Zero trust represents a fundamental shift in cybersecurity philosophy. it moves away from location based trust, where simply being “inside” the corporate network grants access, to a model of continuous, identity centric verification. this shift is operationalized through several key principles.
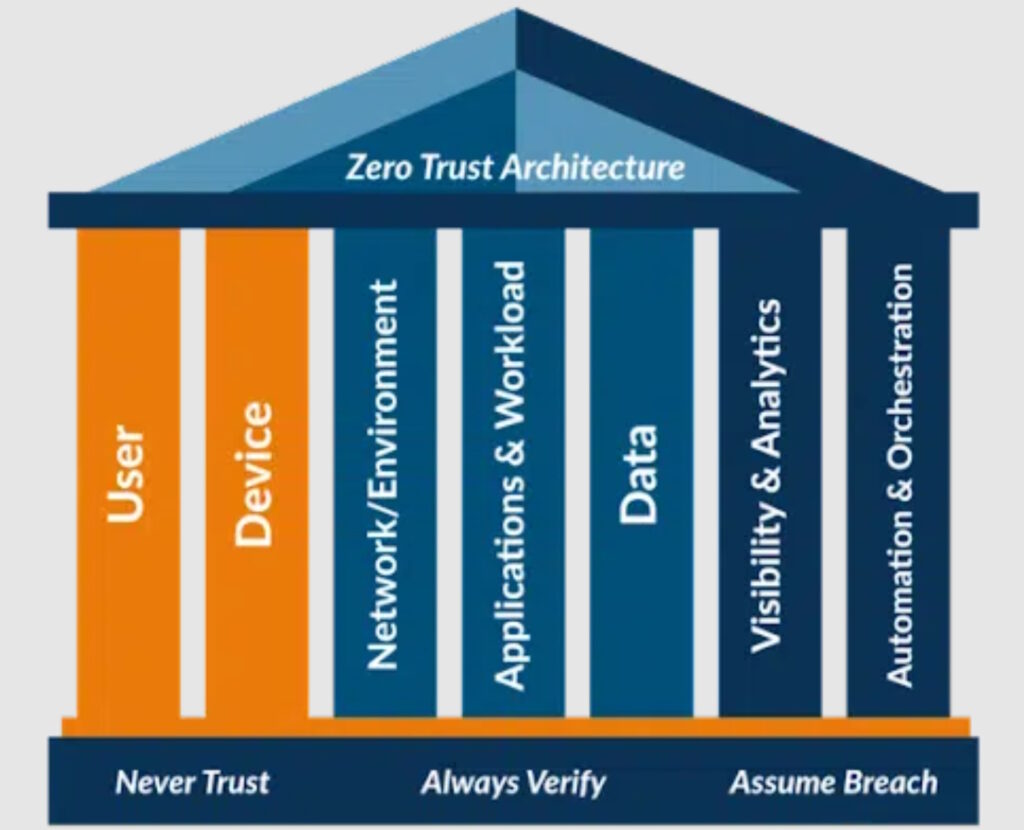
How Does A Zero Trust Security Architecture Work Zero trust security, also known as a zero trust architecture or perimeterless security, assumes no one and no device or application is universally trusted, whether inside or outside the network. Zero trust represents a fundamental shift in cybersecurity philosophy. it moves away from location based trust, where simply being “inside” the corporate network grants access, to a model of continuous, identity centric verification. this shift is operationalized through several key principles. Zero trust architecture (zta) is a modern cyber security architecture that is designed on one foundational principle: never trust anyone, and always verify. unlike traditional security models where you grant privileges by default and treat the network perimeter as safe, zero trust follows zero trust principles. Zero trust is a robust security model that works on the principle of “never trust, always verify” to ensure secure connections. understanding what is zero trust and implementing it can help organizations safeguard their crucial applications, devices, data, and resources. Zero trust architecture (zta) is a security model based on the principle of least privilege. least privilege means that users and devices are only granted the permissions they need to perform their tasks. Zero trust architecture addresses security for all physical and virtual infrastructure, including routers, switches, servers, cloud services, and iot devices. it ensures that every component is continuously verified and protected, regardless of whether it resides on premises or in the cloud.
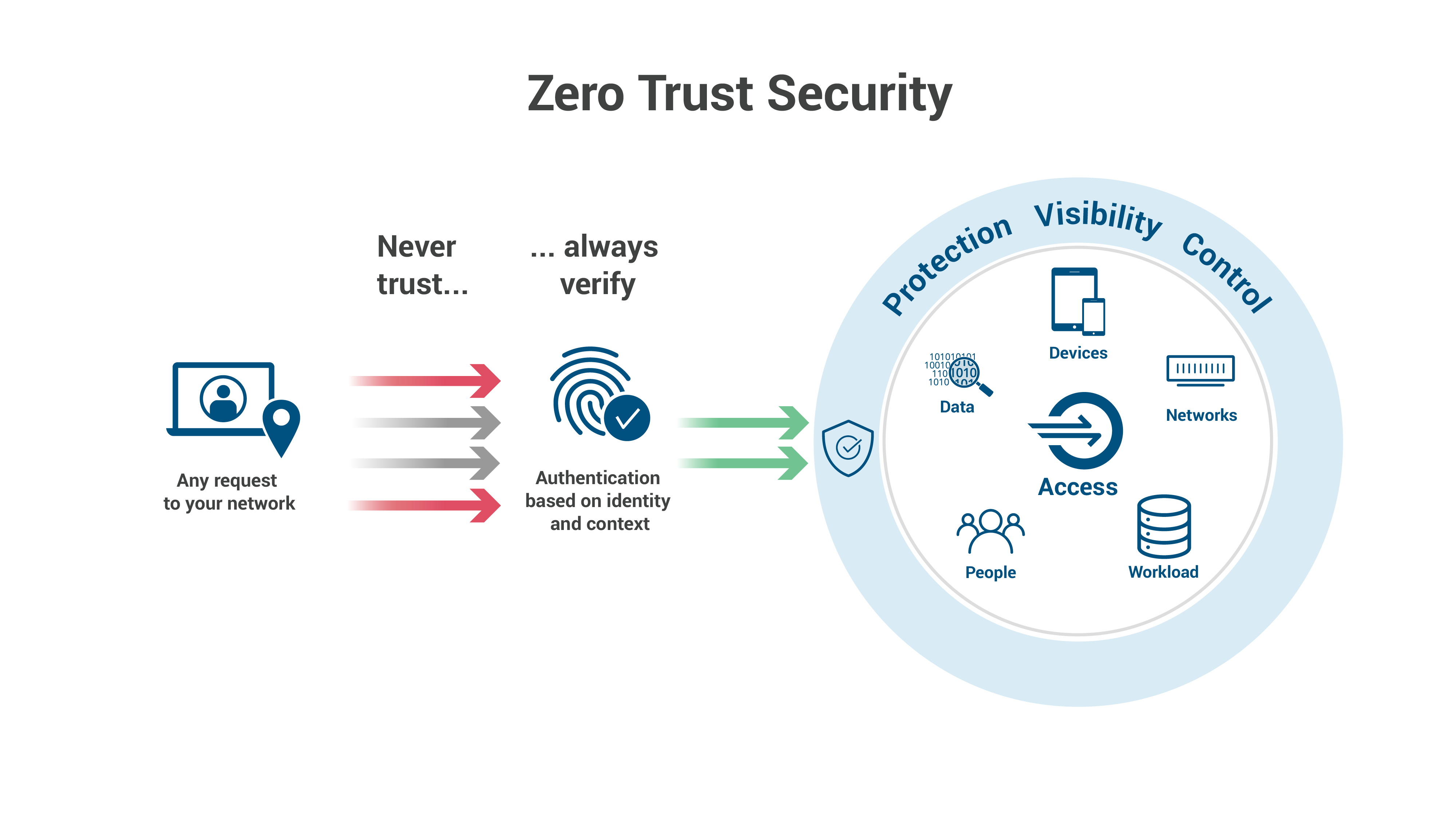
What Is Zero Trust Architecture Zero Trust Security Model Zero trust architecture (zta) is a modern cyber security architecture that is designed on one foundational principle: never trust anyone, and always verify. unlike traditional security models where you grant privileges by default and treat the network perimeter as safe, zero trust follows zero trust principles. Zero trust is a robust security model that works on the principle of “never trust, always verify” to ensure secure connections. understanding what is zero trust and implementing it can help organizations safeguard their crucial applications, devices, data, and resources. Zero trust architecture (zta) is a security model based on the principle of least privilege. least privilege means that users and devices are only granted the permissions they need to perform their tasks. Zero trust architecture addresses security for all physical and virtual infrastructure, including routers, switches, servers, cloud services, and iot devices. it ensures that every component is continuously verified and protected, regardless of whether it resides on premises or in the cloud.

What Is Zero Trust Architecture Zero Trust Security Model Zero trust architecture (zta) is a security model based on the principle of least privilege. least privilege means that users and devices are only granted the permissions they need to perform their tasks. Zero trust architecture addresses security for all physical and virtual infrastructure, including routers, switches, servers, cloud services, and iot devices. it ensures that every component is continuously verified and protected, regardless of whether it resides on premises or in the cloud.
Comments are closed.