What Are Vulnerability Assessments
Vulnerability Assessments A vulnerability assessment is a systematic process used to identify, evaluate and report on security weaknesses across an organization’s digital environment. Vulnerability assessment is an evaluation method that enables organizations to review their systems for potential security weaknesses.
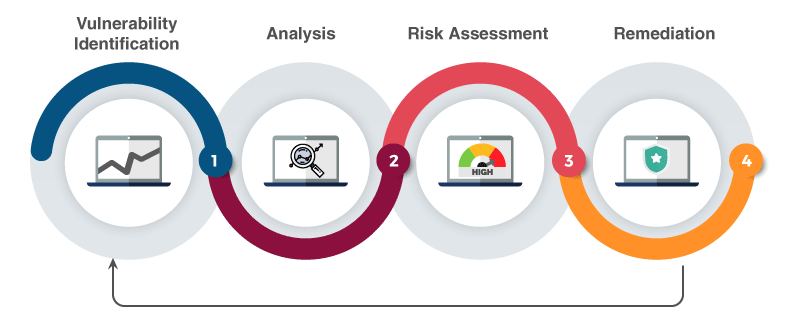
Vulnerability Assessments A Quick Guide A vulnerability assessment is the process of defining, identifying, classifying and prioritizing vulnerabilities in computer systems, applications and network infrastructures. What is a vulnerability assessment? a vulnerability assessment is a procedure that is employed in an information system to determine and rate potential risks. What is vulnerability assessment? vulnerability assessment is essentially a systematic and methodological process that allows you to identify, classify, and prioritize security weaknesses in your organization’s it infrastructure. A vulnerability assessment is a systematic review of security weaknesses in an information system. it evaluates if the system is susceptible to any known vulnerabilities, assigns severity levels to those vulnerabilities, and recommends remediation or mitigation, if and whenever needed.
Vulnerability Assessments A Quick Guide What is vulnerability assessment? vulnerability assessment is essentially a systematic and methodological process that allows you to identify, classify, and prioritize security weaknesses in your organization’s it infrastructure. A vulnerability assessment is a systematic review of security weaknesses in an information system. it evaluates if the system is susceptible to any known vulnerabilities, assigns severity levels to those vulnerabilities, and recommends remediation or mitigation, if and whenever needed. What is a vulnerability assessment? a vulnerability assessment helps identify, classify, and prioritize vulnerabilities in network infrastructure, computer systems, and applications. a vulnerability is a security weaknesses that might expose the organization to cyber threats or risks. Vulnerability assessment (va) is a highly specialized method of identifying security flaws in a system or programming environment. va is entirely a search and find method, intending to ensure that none of the provisos are overlooked. What is vulnerability assessment? the purpose of vulnerability analysis, or vulnerability assessment, is to create a structured process for discovering vulnerabilities in a system, prioritizing them, and creating a mitigation strategy. A vulnerability assessment finds, classifies, and prioritizes vulnerabilities in a computer system’s network infrastructure and applications. it means an organization’s weakness to be attacked by cyber threats and risks.

Vulnerability Assessments Explained Businesspara What is a vulnerability assessment? a vulnerability assessment helps identify, classify, and prioritize vulnerabilities in network infrastructure, computer systems, and applications. a vulnerability is a security weaknesses that might expose the organization to cyber threats or risks. Vulnerability assessment (va) is a highly specialized method of identifying security flaws in a system or programming environment. va is entirely a search and find method, intending to ensure that none of the provisos are overlooked. What is vulnerability assessment? the purpose of vulnerability analysis, or vulnerability assessment, is to create a structured process for discovering vulnerabilities in a system, prioritizing them, and creating a mitigation strategy. A vulnerability assessment finds, classifies, and prioritizes vulnerabilities in a computer system’s network infrastructure and applications. it means an organization’s weakness to be attacked by cyber threats and risks.
Comments are closed.