What Are The Best Practices For Securing It Infrastructure Logs Sys
What Are The Best Practices For Securing It Infrastructure Logs Sys Here’s a quick summary of the 10 essential security measures to improve your syslog management: encrypt your data: use tls encryption (port 6514) to secure log transmission. access controls: implement role based access control (rbac) and multi factor authentication (mfa). Logs contain valuable information that can help diagnose issues, monitor performance, and detect security threats. however, if not properly secured, they can become a target for attackers. below are the best practices for securing it infrastructure logs:.
Securing Your Infrastructure Best Practices Engineerhow It Learn how to conduct security log management that provides visibility into it infrastructure activities and traffic, improves troubleshooting and prevents service disruptions. Learn to implement a powerful syslog infrastructure with rsyslog, syslog ng, effective server setup, siem integration, and essential security best practices for your production systems. Learn why security events are vital for cyber defense. discover types of security logs, log management best practices, and how to ensure log security. This article considers some logging best practices that can lay the groundwork for a robust and scalable logging infrastructure. learn more!.
.png)
Cloud Security Best Practices For Securing Your Cloud Infrastructure Learn why security events are vital for cyber defense. discover types of security logs, log management best practices, and how to ensure log security. This article considers some logging best practices that can lay the groundwork for a robust and scalable logging infrastructure. learn more!. Developing and implementing an enterprise approved logging policy improves an organisation’s chances of detecting malicious behaviour on their systems and enforces a consistent method of logging across an organisation’s environments. Event logging, combined with effective log analysis, is fundamental to securing critical systems and services. it provides necessary visibility into networks and systems, enabling timely. In this article, we’ll explore the key components of effective log management and best practices for 2026 to help you transform raw data into valuable security and operational insights. Centralized, standardized logs can catch attacks early and streamline compliance. learn how to log smarter with these 7 best practices.

Best Practices For Securing Your Systems Developing and implementing an enterprise approved logging policy improves an organisation’s chances of detecting malicious behaviour on their systems and enforces a consistent method of logging across an organisation’s environments. Event logging, combined with effective log analysis, is fundamental to securing critical systems and services. it provides necessary visibility into networks and systems, enabling timely. In this article, we’ll explore the key components of effective log management and best practices for 2026 to help you transform raw data into valuable security and operational insights. Centralized, standardized logs can catch attacks early and streamline compliance. learn how to log smarter with these 7 best practices.
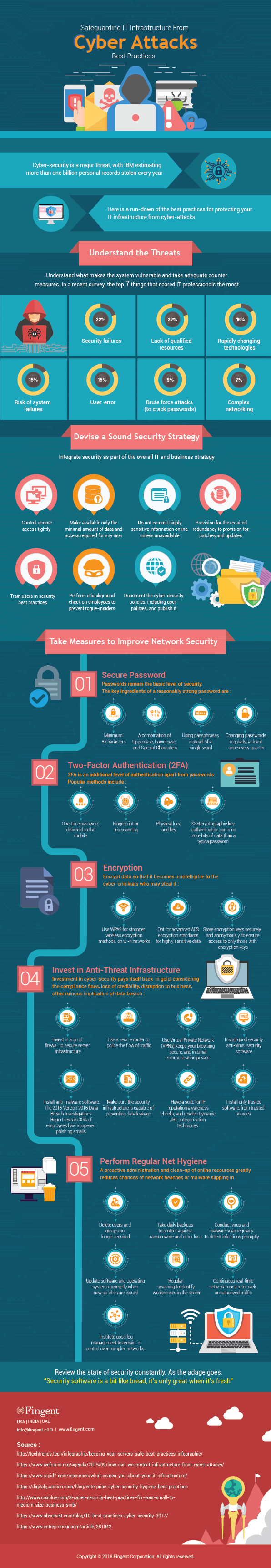
Safeguarding It Infrastructure From Cyber Attacks Best Practices In this article, we’ll explore the key components of effective log management and best practices for 2026 to help you transform raw data into valuable security and operational insights. Centralized, standardized logs can catch attacks early and streamline compliance. learn how to log smarter with these 7 best practices.
Comments are closed.