Website Vulnerability Scanning With Zap
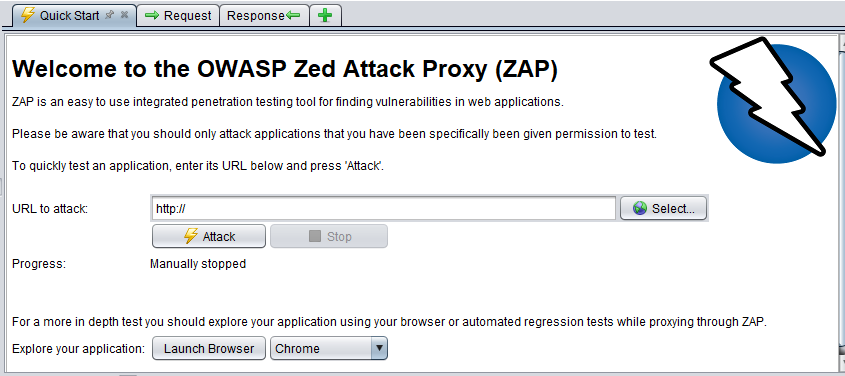
Website Vulnerability Scanning With Zap Zap is a free, open source web application security scanner actively maintained by an international community. The main goal of this lab was to conduct a dynamic application security testing (dast) scan against a vulnerable target (damn vulnerable web application dvwa) to identify security flaws.
Website Vulnerability Scanning With Zap Online web application vulnerability scan powered by owasp zap. scan websites for security vulnerabilities. Vulnerability scanning tools description web application vulnerability scanners are automated tools that scan web applications, normally from the outside, to look for security vulnerabilities such as cross site scripting, sql injection, command injection, path traversal and insecure server configuration. Owasp zap (zed attack proxy) is one of the most widely used tools for web application security testing, and it provides an easy way to scan websites for vulnerabilities. One of the most powerful tools for testing web application vulnerabilities is owasp zap (zed attack proxy). this guide will walk you through its features, how to test a website, and generate reports while highlighting where to include images for better illustration.

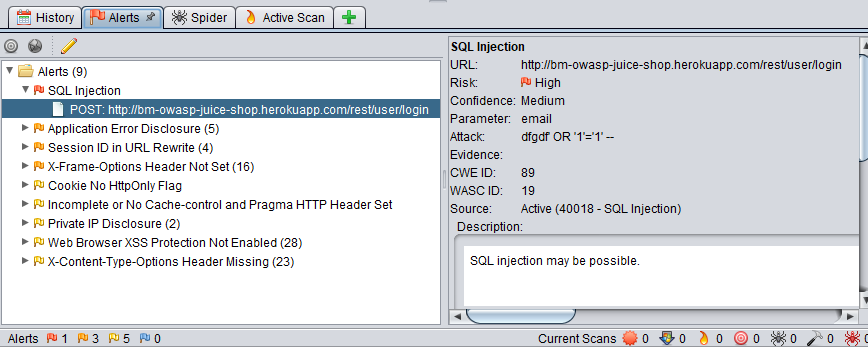
Web Server Vulnerability Scanning With Zap Owasp zap (zed attack proxy) is one of the most widely used tools for web application security testing, and it provides an easy way to scan websites for vulnerabilities. One of the most powerful tools for testing web application vulnerabilities is owasp zap (zed attack proxy). this guide will walk you through its features, how to test a website, and generate reports while highlighting where to include images for better illustration. Discover how to detect web app vulnerabilities using owasp zap with step by step guidance on installation, configuration, and advanced scanning. If you’re looking for a free, powerful way to test your website or api for security vulnerabilities, owasp zap is one of the best tools available. in this guide, you’ll learn what owasp zap is, how it works, why it matters, and how to use it in real world scenarios. Owasp zap (zed attack proxy) is an open source, free to use web application security testing tool maintained by the open web application security project (owasp). it is designed to identify vulnerabilities in web applications during development, testing, and deployment phases. Owasp zap can identify vulnerabilities in web applications including compromised authentication, exposure of sensitive data, security misconfigurations, sql injection, cross site scripting (xss), insecure deserialization, and components with known vulnerabilities.

Web Server Vulnerability Scanning With Owasp Zap Discover how to detect web app vulnerabilities using owasp zap with step by step guidance on installation, configuration, and advanced scanning. If you’re looking for a free, powerful way to test your website or api for security vulnerabilities, owasp zap is one of the best tools available. in this guide, you’ll learn what owasp zap is, how it works, why it matters, and how to use it in real world scenarios. Owasp zap (zed attack proxy) is an open source, free to use web application security testing tool maintained by the open web application security project (owasp). it is designed to identify vulnerabilities in web applications during development, testing, and deployment phases. Owasp zap can identify vulnerabilities in web applications including compromised authentication, exposure of sensitive data, security misconfigurations, sql injection, cross site scripting (xss), insecure deserialization, and components with known vulnerabilities.

Vulnerability Scanning Using Owasp Zap Pdf Owasp zap (zed attack proxy) is an open source, free to use web application security testing tool maintained by the open web application security project (owasp). it is designed to identify vulnerabilities in web applications during development, testing, and deployment phases. Owasp zap can identify vulnerabilities in web applications including compromised authentication, exposure of sensitive data, security misconfigurations, sql injection, cross site scripting (xss), insecure deserialization, and components with known vulnerabilities.
Web Application Vulnerability Scanning With Owasp Zap Tryhackme
Comments are closed.