Web Security Academy Insecure Deserialization 5 Exploiting Java Deserialization Apache Commons

Exploiting Insecure Deserialization Vulnerabilities Web Security Academy This write up for the lab exploiting java deserialization with apache commons is part of my walk through series for portswigger's web security academy. learning path: advanced topics → insecure deserialization. Walkthrough videos regarding the solutions of the lab "insecure deserialization:lab #5 exploiting java deserialization with apache commons" of "insecure deserialization".

Owasp Top 10 In 2017 Insecure Deserialization Security Vulnerability In this section, we'll cover what insecure deserialization is and describe how it can potentially expose websites to high severity attacks. we'll highlight typical scenarios and demonstrate some widely applicable techniques using concrete examples of php, ruby, and java deserialization. In this section, we'll teach you how to exploit some common scenarios using examples from php, ruby, and java deserialization. we hope to demonstrate how. In this article, we’ll explore how deserialization vulnerabilities arise, look at real world attack scenarios, understand gadget chains, and walk through practical defenses to secure your java applications. Insecure deserialization is a vulnerability that occurs when an application accepts serialized data from users and restores it into objects without proper validation, allowing attackers to.
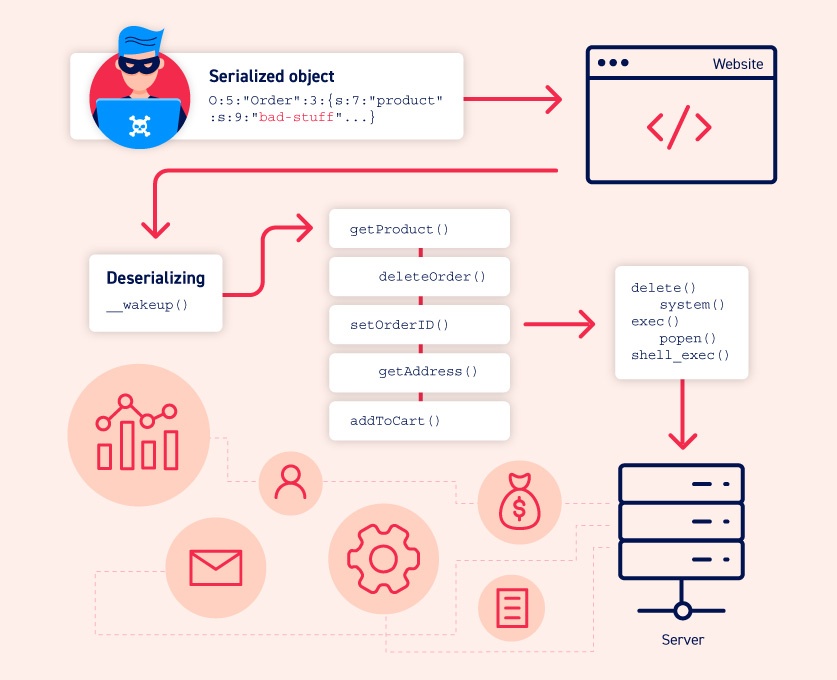
Insecure Deserialization Web Security Academy In this article, we’ll explore how deserialization vulnerabilities arise, look at real world attack scenarios, understand gadget chains, and walk through practical defenses to secure your java applications. Insecure deserialization is a vulnerability that occurs when an application accepts serialized data from users and restores it into objects without proper validation, allowing attackers to. This lab uses a serialization based session mechanism and loads the apache commons collections library. although you don't have source code access, you can still exploit this lab using pre built gadget chains. In this lab, we explore a critical vulnerability arising from insecure java deserialization, specifically when an application uses apache commons collections—a library known to be exploitable when deserialization is not properly secured. Without further ado, let's dive in. this lab uses a serialization based session mechanism and loads the apache commons collections library. although you don't have source code access, you can still exploit this lab using pre built gadget chains. We don’t just teach students how to identify deserialization bugs — we show them how to exploit, chain, and escalate them like pros. from custom gadget development to analyzing obfuscated code in real targets, our advanced labs simulate real world exploitation in java, , and python.
Comments are closed.