Web Checklist Pdf Computing Computer Data

Computing Learner Checklist Pdf Software Computing The document is a web security checklist authored by venkatesan subramanian, outlining essential security measures to protect web applications. it includes 53 requirements such as using https, avoiding sql injection, implementing content security policy, and ensuring strong password policies. Withsecure presents a comprehensive checklist, developed through collaboration with experts from multiple fields. this unique list provides a broad and unparalleled perspective on cyber security, organizing tasks by both priority and complexity.

Getting Started Checklist Pdf Computer Network Cloud Computing Check if your desktop and laptop computers are equipped with anti theft devices. check if your network servers are physically secure in a separate area. make sure you have an accurate inventory of all computing equipment and software that is stored off site. Be considerate of the information you give out online. posting information about your current location, address or routine can leave you vulnerable. look into the privacy settings of applications and the websites you visit to see what and how information is collected from you. Cybersecurity is defined as a system of technologies, processes, and practices designed to protect your computers, networks, applications, and data from attack, damage, or unauthorized access. The national checklist program (ncp), defined by the nist sp 800 70, is the u.s. government repository of publicly available security checklists (or benchmarks) that provide detailed low level guidance on setting the security configuration of operating systems and applications.

Confidential Computing System Technology Checklist To Implement Confidentia Cybersecurity is defined as a system of technologies, processes, and practices designed to protect your computers, networks, applications, and data from attack, damage, or unauthorized access. The national checklist program (ncp), defined by the nist sp 800 70, is the u.s. government repository of publicly available security checklists (or benchmarks) that provide detailed low level guidance on setting the security configuration of operating systems and applications. The checklist contains a number of elements each of which addresses a different aspect of computer security or risk and is important for protecting your organisational data and computing resources. Learn to protect your information where it is stored, processed, and transmitted. have a contingency plan, which generally starts with being able to recover systems, networks, and data from known, accurate backups. A cyber security checklist template is a tool used to assess and ensure the security of computer systems, networks, and data. it includes a list of best practices and security measures to be taken to protect against cyber threats such as malware, viruses, and unauthorized access. The key to preventing major data leakage and minimizing the consequences of a cyber attack is to be able to detect it and know what to do about it. you can become an important asset to your own cyber security defenses if you can learn about cyber security threats and get adequate protection.
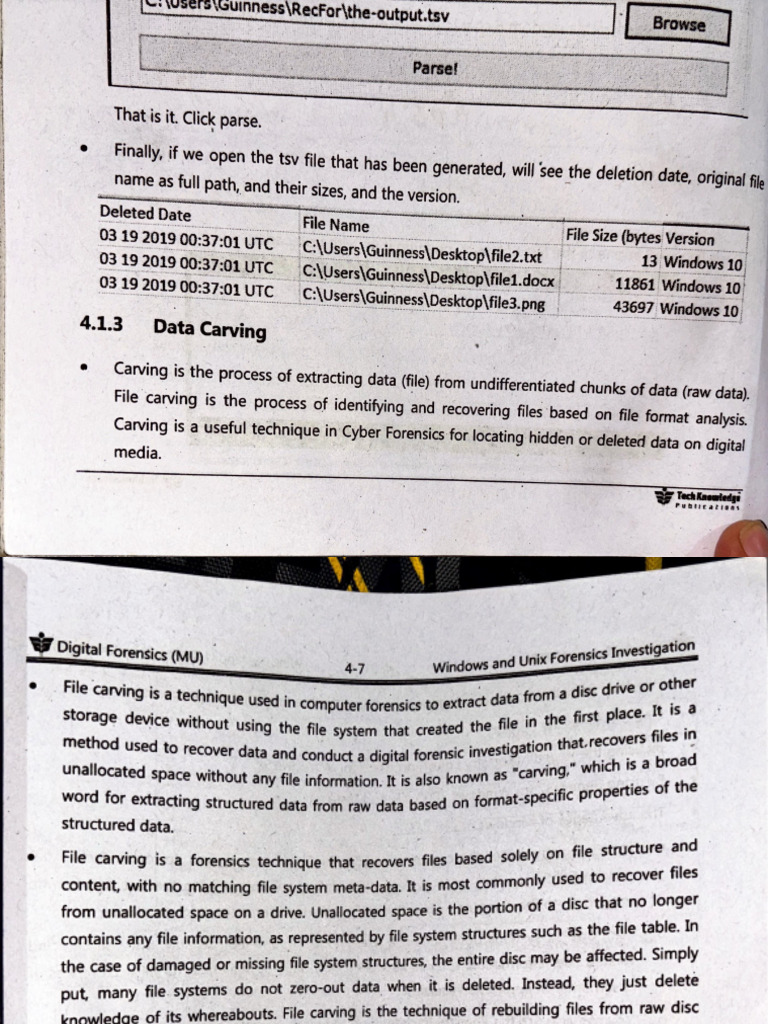
Data Carving Pdf Computing Computer Data The checklist contains a number of elements each of which addresses a different aspect of computer security or risk and is important for protecting your organisational data and computing resources. Learn to protect your information where it is stored, processed, and transmitted. have a contingency plan, which generally starts with being able to recover systems, networks, and data from known, accurate backups. A cyber security checklist template is a tool used to assess and ensure the security of computer systems, networks, and data. it includes a list of best practices and security measures to be taken to protect against cyber threats such as malware, viruses, and unauthorized access. The key to preventing major data leakage and minimizing the consequences of a cyber attack is to be able to detect it and know what to do about it. you can become an important asset to your own cyber security defenses if you can learn about cyber security threats and get adequate protection.
Comments are closed.