Web Application Penetration Testing Insecure Cryptographic Storage
Web App Penetration Testing Service Bytium Llc Collection of articles [cryptographic weaknesses in web applications: attacks and fixes; what is security misconfiguration in owasp?]. Insecure cryptographic storage vulnerability is a type of flaw in the way that data is being stored and secured online. it's an issue that impacts nearly all websites and online organizations, but it can be especially problematic with sensitive private data.

Web Penetration Testing Understanding Different Web Application Cryptographic failures refer to security issues that arise from incorrect or insecure use of cryptographic functions within a web application. cryptography involves securing information through techniques like encryption and hashing. Ing conditions: the open web application security project (owasp) is a worldwide free and open com munity focused on improving the security of appli. ation software. our mission is to make application security “visible”, so that people and organizations can make informed decisions about application. As it is a famous framework for web application pen testing traing, i want to start to write down my practice & solutions on the lessons and challenges of security shepherd for tracking. Cryptographic algorithms are the methods by which data is scrambled to prevent observation or influence by unauthorized actors. insecure cryptography can be exploited to expose sensitive information, modify data in unexpected ways, spoof identities of other users or devices, or other impacts.
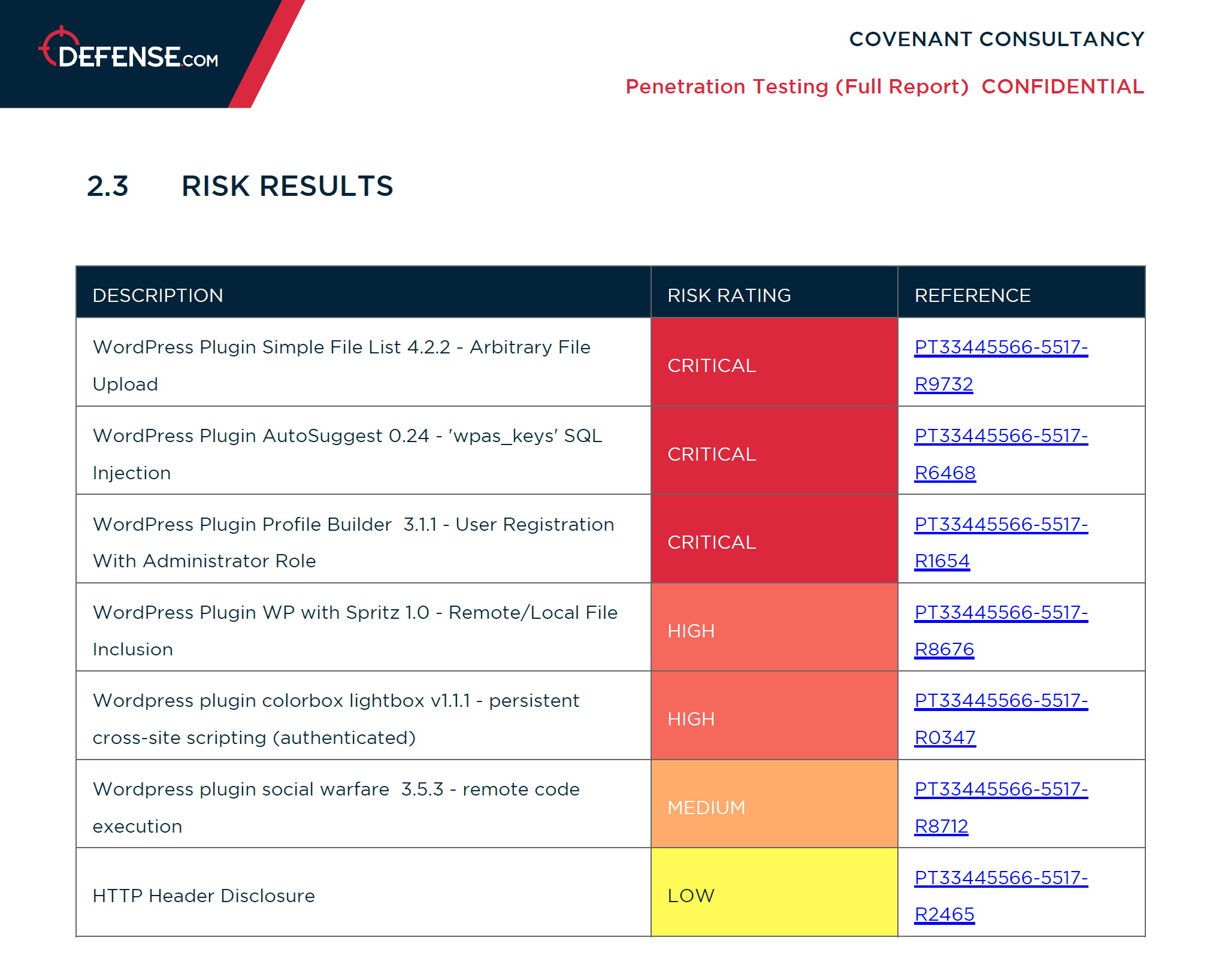
Web Application Penetration Testing As it is a famous framework for web application pen testing traing, i want to start to write down my practice & solutions on the lessons and challenges of security shepherd for tracking. Cryptographic algorithms are the methods by which data is scrambled to prevent observation or influence by unauthorized actors. insecure cryptography can be exploited to expose sensitive information, modify data in unexpected ways, spoof identities of other users or devices, or other impacts. Understanding the steps involved in a web application penetration testing for enhanced security and the tools used in each step, how proactive web security testing can help prevent significant loss, and how it can help you choose the right web app pentesting service provider. Our objective is to summarize the state of the art in web application security testing which could benefit practitioners to potentially utilize that information. Using home grown algorithms insecure use of strong algorithms continued use of proven weak algorithms (md5, sha 1, rc3, rc4, etc.) hard coding keys, and storing keys in unprotected stores. In this work, penetration tests were carried out on the website to identify vulnerability of the website. however, attack recovery mechanisms were not investigated in this work.
Comments are closed.