Weak Service Permissions
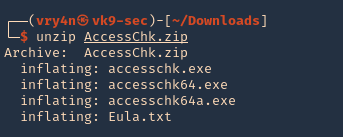
Windows Weak Service Permissions Vk9 Security In this post we will be exploring yet another technique that involves weak permissions; however, instead of a folder file misconfiguration, this time we will be exploiting weak service permissions. Learn windows privilege escalation through weak service permissions, insecure configurations, and exploitation techniques like ptoc and pto.

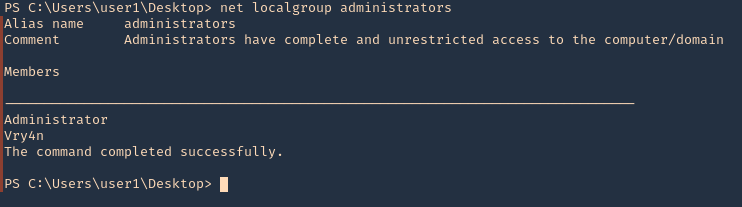
Windows Weak Service Permissions Vk9 Security Weak service permissions" on windows indicate insufficient or incorrect permissions within services. exploiting this vulnerability enables attackers to gain unauthorized access or elevated privileges by manipulating a service's configuration. Since services usually run under nt authority\system, our malicious binary gets executed with system privileges:. Weak service permissions occur when a service's configuration or binary can be modified by non administrative users. this allows us to either replace the service binary with a malicious one, or change the service's configuration to point to our payload. If the permissions for this binary allow a local user without special privileges to modify or replace it with a malicious version, the attacker may gain the privileges of the service account, which is often a high privilege account.
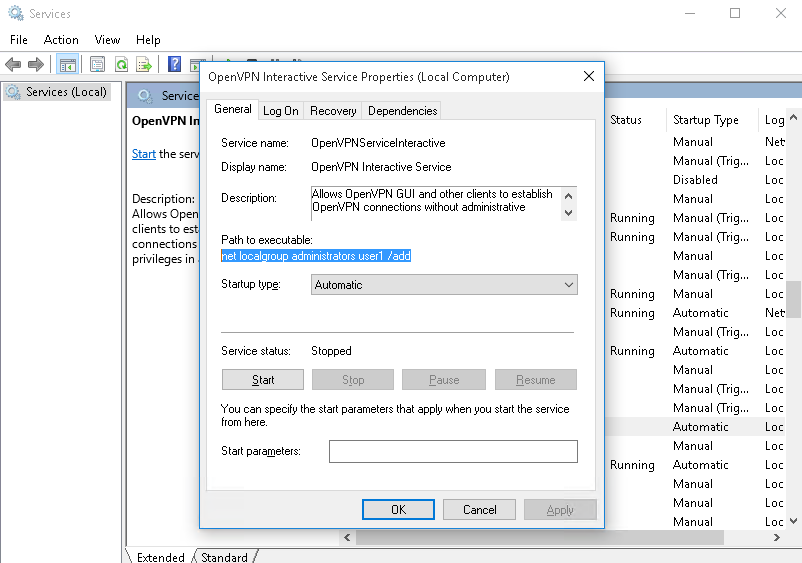
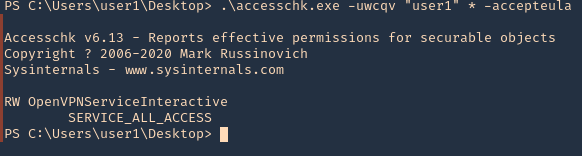
Windows Weak Service Permissions Vk9 Security Weak service permissions occur when a service's configuration or binary can be modified by non administrative users. this allows us to either replace the service binary with a malicious one, or change the service's configuration to point to our payload. If the permissions for this binary allow a local user without special privileges to modify or replace it with a malicious version, the attacker may gain the privileges of the service account, which is often a high privilege account. In this article, we will discuss how windows services can be misconfigured and provide ways to mitigate these risks. the steps for the demonstration are in the tryhackme windows privilege. Weak service permissions are a common and critical security flaw in windows environments. according to recent analyses, a significant percentage of windows machines have at least one service with insecure permissions, making this an effective and reliable privilege escalation vector. Some common methods include, insecure permissions on service executable, and insecure service permissions. in this article, we will discuss how windows services can be misconfigured and provide ways to mitigate these risks. ⚡ attack highlights 🔐 modify service configuration (binpath) 📂 overwrite service executable 👤 abuse weak acl permissions 🚀 escalate to nt authority\system 💡 if a user has permissions like service change config or write access to service binaries, they can replace them with malicious payloads and gain elevated privileges.
Windows Weak Service Permissions Vk9 Security In this article, we will discuss how windows services can be misconfigured and provide ways to mitigate these risks. the steps for the demonstration are in the tryhackme windows privilege. Weak service permissions are a common and critical security flaw in windows environments. according to recent analyses, a significant percentage of windows machines have at least one service with insecure permissions, making this an effective and reliable privilege escalation vector. Some common methods include, insecure permissions on service executable, and insecure service permissions. in this article, we will discuss how windows services can be misconfigured and provide ways to mitigate these risks. ⚡ attack highlights 🔐 modify service configuration (binpath) 📂 overwrite service executable 👤 abuse weak acl permissions 🚀 escalate to nt authority\system 💡 if a user has permissions like service change config or write access to service binaries, they can replace them with malicious payloads and gain elevated privileges.
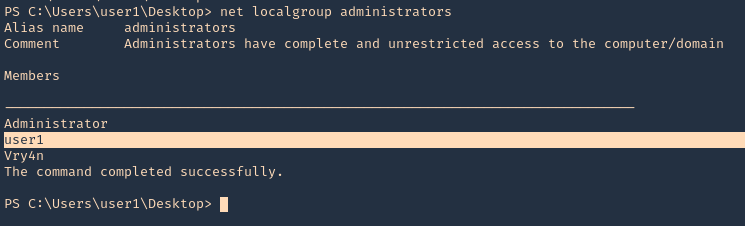
Windows Weak Service Permissions Vk9 Security Some common methods include, insecure permissions on service executable, and insecure service permissions. in this article, we will discuss how windows services can be misconfigured and provide ways to mitigate these risks. ⚡ attack highlights 🔐 modify service configuration (binpath) 📂 overwrite service executable 👤 abuse weak acl permissions 🚀 escalate to nt authority\system 💡 if a user has permissions like service change config or write access to service binaries, they can replace them with malicious payloads and gain elevated privileges.
Windows Weak Service Permissions Vk9 Security
Comments are closed.