Vulnerability Scanning Using Nessus Pdf

Vulnerability Scanning With Nessus A Practical Guide Pdf Pdf | this report presents the findings of a comprehensive vulnerability analysis conducted using the nessus vulnerability scanner. This project involves conducting a local and network vulnerability assessment using free tools to identify common security issues on targets. perform a basic vulnerability scan using nessus nessus report.pdf at main · cyberdarwan perform a basic vulnerability scan using nessus.

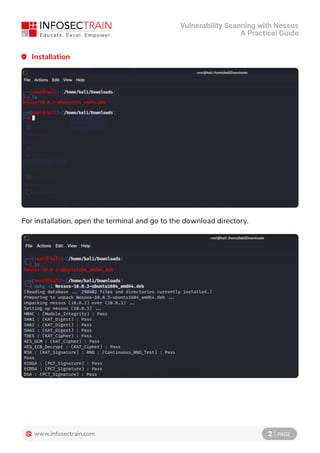
Scanning For Vulnerabilities Using Nessus Computers And Course Hero Vulnerability scanning with nessus – a practical guide offers a step by step approach to identifying, assessing, and managing security weaknesses in your network. Vulnerability scanning using nessus free download as pdf file (.pdf), text file (.txt) or read online for free. nessus is a vulnerability scanner that is free for non enterprise use but has paid enterprise options. It will detect ftp running on port 31337. much better about not crashing targets! which ones should i do? nessus will crash systems, routers, firewalls, and any other devices on the network! challenges – what about the application? make sure you have at least one other tool to test the application! challenges – scan what? when?. Conducting network scans => running a basic network scan => interpreting scan results: vulnerabilities, risks, and remediations => understanding risk ratings (critical, high, medium, low) => navigating scan results: identifying high priority vulnerabilities => generating reports.

Vulnerability Assessment Using Nessus Tool Pptx It will detect ftp running on port 31337. much better about not crashing targets! which ones should i do? nessus will crash systems, routers, firewalls, and any other devices on the network! challenges – what about the application? make sure you have at least one other tool to test the application! challenges – scan what? when?. Conducting network scans => running a basic network scan => interpreting scan results: vulnerabilities, risks, and remediations => understanding risk ratings (critical, high, medium, low) => navigating scan results: identifying high priority vulnerabilities => generating reports. Nassar almutairi ail. mm nassar almutairi ail. mm nassar almutairi ail. mm nassar almutairi nassar almutairi ail. mm nassar almutairi ail. mm nassar almutairi ail. mm nassar almutairi nassar almutairi ail. mm nassar almutairi ail. mm nassar almutairi ail. mm nassar almutairi security* network vulnerability scanners tenable nessus openvas. These reports can be saved to a log directory or repository to be reviewed by other team members and to demonstrate that scans have taken place according to company policy. You can create a scan report to help you analyze the vulnerabilities and remediations on affected hosts. you can create a scan report in pdf, html, or csv format, and customize it to contain only certain information. Nessus scans a computer and raises an alert if any exploitable vulnerability is discovered. the paper discusses its key features, its operation and setup procedures and provides an overview.
Vulnerability Scanning With Nessus A Practical Guide Pdf Nassar almutairi ail. mm nassar almutairi ail. mm nassar almutairi ail. mm nassar almutairi nassar almutairi ail. mm nassar almutairi ail. mm nassar almutairi ail. mm nassar almutairi nassar almutairi ail. mm nassar almutairi ail. mm nassar almutairi ail. mm nassar almutairi security* network vulnerability scanners tenable nessus openvas. These reports can be saved to a log directory or repository to be reviewed by other team members and to demonstrate that scans have taken place according to company policy. You can create a scan report to help you analyze the vulnerabilities and remediations on affected hosts. you can create a scan report in pdf, html, or csv format, and customize it to contain only certain information. Nessus scans a computer and raises an alert if any exploitable vulnerability is discovered. the paper discusses its key features, its operation and setup procedures and provides an overview.
Comments are closed.