Vulnerability Risk Assessment 5 Essential Steps

Vulnerability Risk Assessment Empty Pdf Risk Supply Chain The five stages are generally considered to be asset & vulnerability identification, vulnerability scanning, risk ranking, mitigation, and verification & monitoring. Discover how a vulnerability risk assessment protects your organization. learn essential steps to identify, prioritize, and remediate risks effectively.
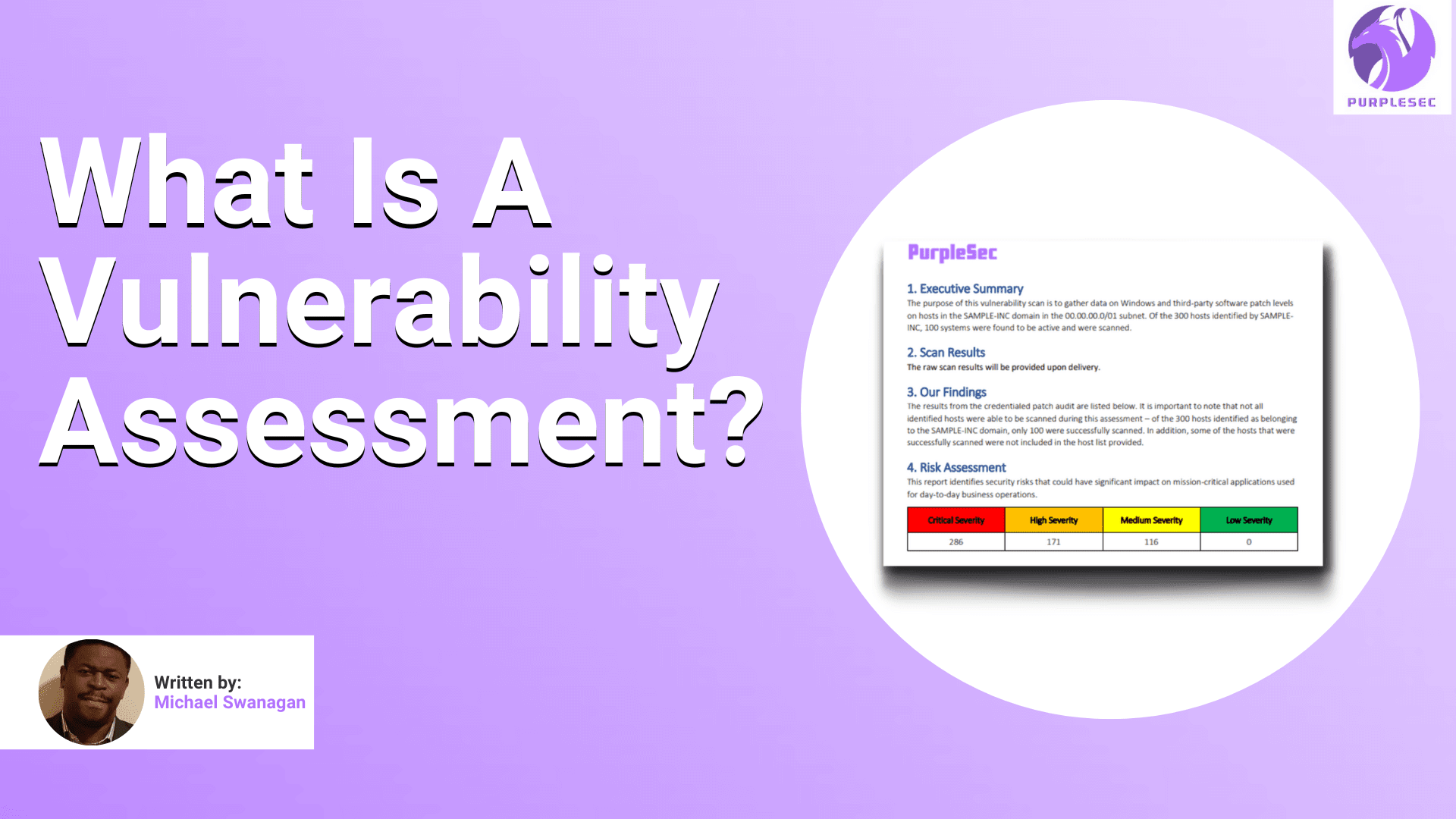
What Is A Vulnerability Assessment A Complete Guide For 2023 If you're looking to stay ahead of cyber threats, vulnerability management is a must have. our handy checklist will help you succeed. Discover the essential steps to safeguard your systems from cyber threats. learn how to conduct an external vulnerability assessment with charles it. Discover step by step methods for vulnerability risk assessment to identify, prioritize,fix security gaps & ensures continuous protection against cyberattacks. Conducting a vulnerability assessment is an essential part of any organization’s security strategy. by following these steps, you can identify potential vulnerabilities in your systems, networks, and applications, and take action to mitigate them before attackers do.

Steps For Vulnerability And Risk Assessment Download Scientific Diagram Discover step by step methods for vulnerability risk assessment to identify, prioritize,fix security gaps & ensures continuous protection against cyberattacks. Conducting a vulnerability assessment is an essential part of any organization’s security strategy. by following these steps, you can identify potential vulnerabilities in your systems, networks, and applications, and take action to mitigate them before attackers do. By following these five stages – discovery & scanning, reporting & assessment, prioritization, remediation & patch management, and verification & continuous improvement – organizations can establish a comprehensive vulnerability management program. What are the main stages of the vulnerability management life cycle? the life cycle typically includes five stages: discovery (finding vulnerabilities), assessment (evaluating risks), prioritization (ranking vulnerabilities), remediation (fixing issues), and verification (confirming fixes). Discover how vulnerability assessments assist in identifying risks, the keys steps, and the benefits of a proactive security approach. Vulnerability risk assessment (vra) plays a crucial role in cybersecurity by systematically identifying, assessing, and prioritizing vulnerabilities that, if left unaddressed, could expose your organization to significant risks.

Fema Risk And Vulnerability Assessment Ajratw By following these five stages – discovery & scanning, reporting & assessment, prioritization, remediation & patch management, and verification & continuous improvement – organizations can establish a comprehensive vulnerability management program. What are the main stages of the vulnerability management life cycle? the life cycle typically includes five stages: discovery (finding vulnerabilities), assessment (evaluating risks), prioritization (ranking vulnerabilities), remediation (fixing issues), and verification (confirming fixes). Discover how vulnerability assessments assist in identifying risks, the keys steps, and the benefits of a proactive security approach. Vulnerability risk assessment (vra) plays a crucial role in cybersecurity by systematically identifying, assessing, and prioritizing vulnerabilities that, if left unaddressed, could expose your organization to significant risks.

The 5 Essential Steps Of Risk Assessment Abdul Manan Discover how vulnerability assessments assist in identifying risks, the keys steps, and the benefits of a proactive security approach. Vulnerability risk assessment (vra) plays a crucial role in cybersecurity by systematically identifying, assessing, and prioritizing vulnerabilities that, if left unaddressed, could expose your organization to significant risks.
Comments are closed.