Vulnerability Reporting

Vulnerability Assessment Report Template Pdf Security Computer Once a security contact has been identified, an initial report should be made of the details of the vulnerability. ideally this should be done over an encrypted channel (such as the use of pgp keys), although many organizations do not support this. Learn what vulnerability disclosure is, why it matters, and how to handle it responsibly. explore its risks, significance, and best practices to protect digital assets.

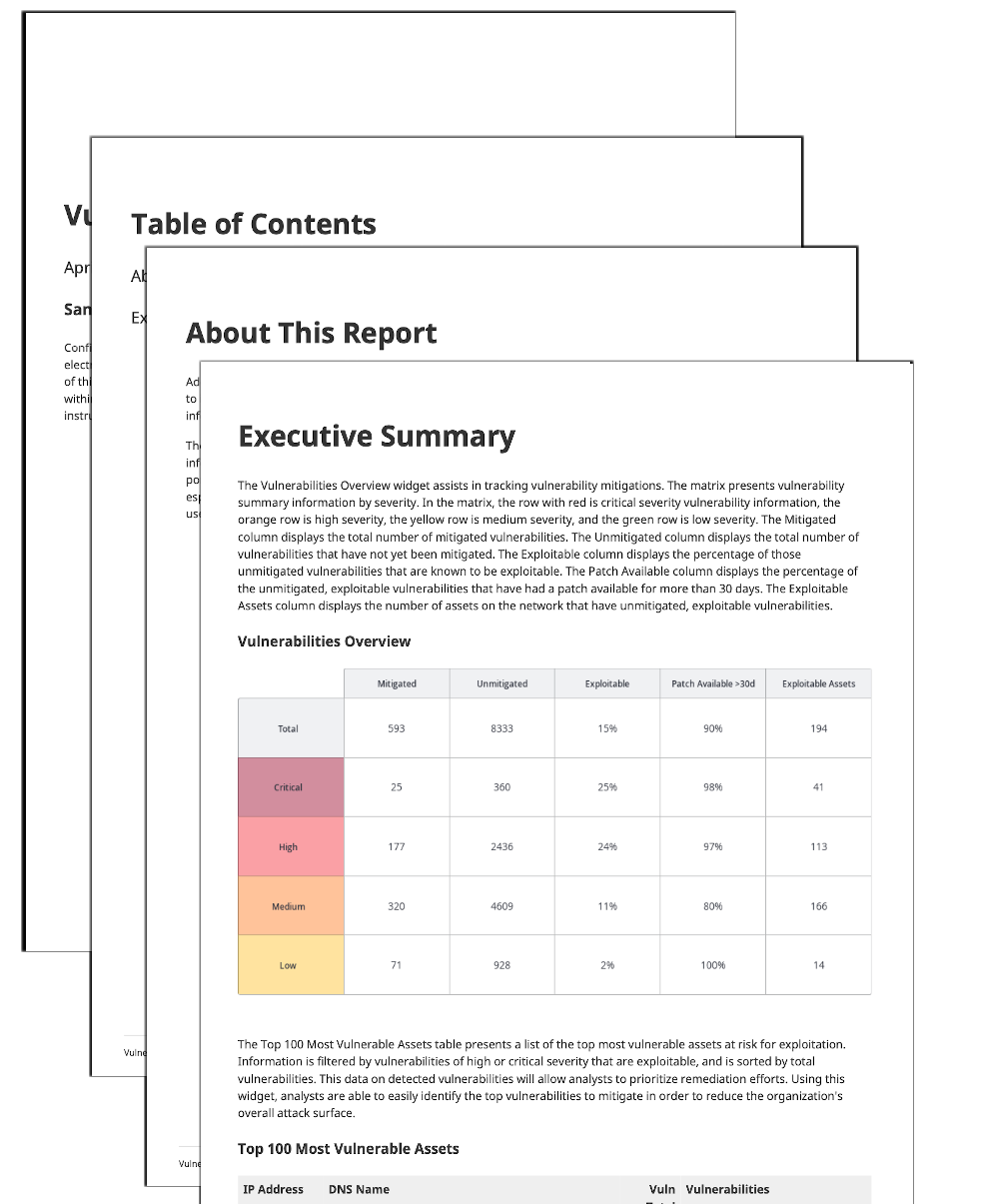
How To Write A Vulnerability Assessment Report Pdf Vulnerability Identify, define, and catalog publicly disclosed cybersecurity vulnerabilities. there are currently over 321,000 cve records accessible via download or keyword search above. the cve program partners with community members worldwide to grow cve content and expand its usage. By the end of this guide, you’ll understand the key components of a vulnerability assessment report, how an effective report empowers you to manage risks efficiently, and how it contributes to long term security and business growth. Find out how to write a good vulnerability report and why it's important to do well. After a vulnerability assessment or penetration test, the security team or third party vendor delivers a report detailing their findings. this document is critical; it communicates identified weaknesses, assesses their potential impact, and provides recommendations for fixing them.

Security Vulnerability Reporting Nano Documentation Find out how to write a good vulnerability report and why it's important to do well. After a vulnerability assessment or penetration test, the security team or third party vendor delivers a report detailing their findings. this document is critical; it communicates identified weaknesses, assesses their potential impact, and provides recommendations for fixing them. Reporting: vulnerability management tools provide reports that give organizations an overview of their vulnerabilities and their risk level. these reports help organizations prioritize their remediation efforts and track their progress over time. Creating a comprehensive vulnerability assessment report is a crucial step in maintaining and improving the cybersecurity posture of any organization. this section will guide you through the initial steps in how to create a comprehensive vulnerability assessment report. Understand the key components of a high quality vulnerability report. learn how to reproduce and document vulnerabilities using technical proofs (commands, scripts, or video pocs). This document recommends guidance for establishing a federal vulnerability disclosure framework, properly handling vulnerability reports, and communicating the mitigation and or remediation of vulnerabilities.
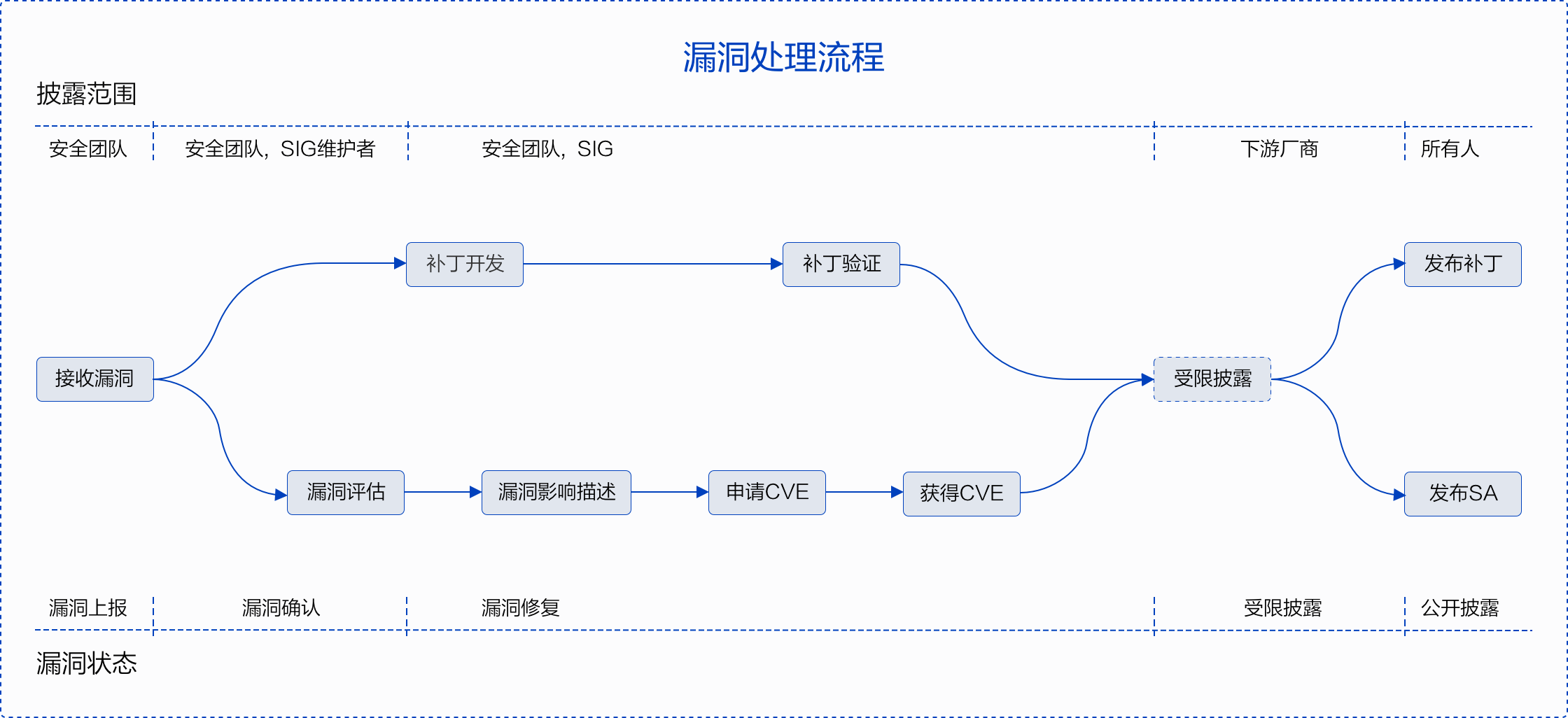
Vulnerability Reporting Cloudwego Reporting: vulnerability management tools provide reports that give organizations an overview of their vulnerabilities and their risk level. these reports help organizations prioritize their remediation efforts and track their progress over time. Creating a comprehensive vulnerability assessment report is a crucial step in maintaining and improving the cybersecurity posture of any organization. this section will guide you through the initial steps in how to create a comprehensive vulnerability assessment report. Understand the key components of a high quality vulnerability report. learn how to reproduce and document vulnerabilities using technical proofs (commands, scripts, or video pocs). This document recommends guidance for establishing a federal vulnerability disclosure framework, properly handling vulnerability reports, and communicating the mitigation and or remediation of vulnerabilities.
Vulnerability Reporting Template Understand the key components of a high quality vulnerability report. learn how to reproduce and document vulnerabilities using technical proofs (commands, scripts, or video pocs). This document recommends guidance for establishing a federal vulnerability disclosure framework, properly handling vulnerability reports, and communicating the mitigation and or remediation of vulnerabilities.

Rh Isac Why Reporting Results Of A Vulnerability Assessment Is An
Comments are closed.