Vulnerability Report The Basics Hd

Vulnerability Assessment Report Template Pdf Security Computer The vulnerability report provides information about vulnerabilities from scans of the default branch. #emerasoft consiglia: vulnerability report the basics (hd) the vulnerability report provides information about vulnerabilities from scans of the default branch.
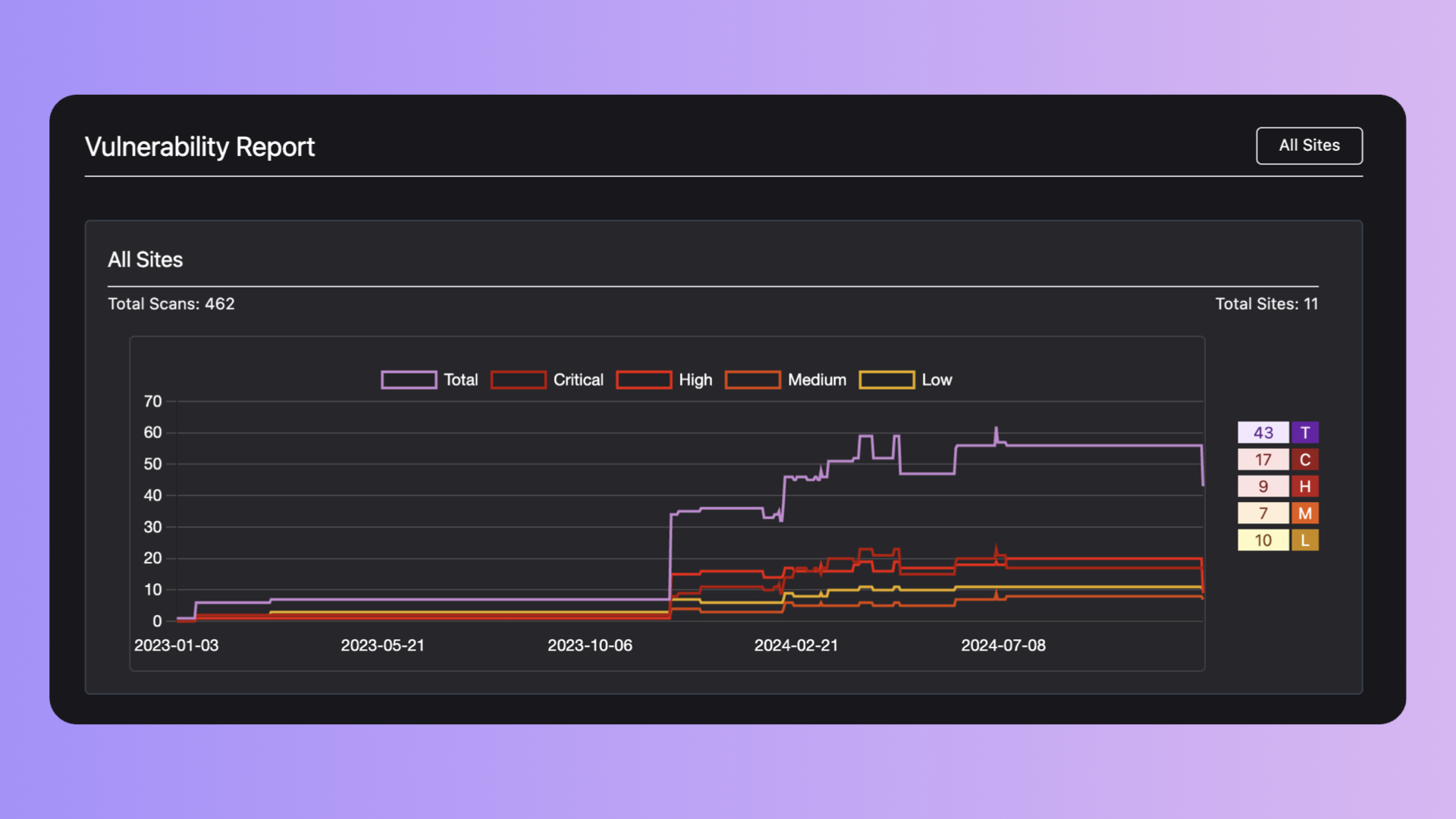
Introducing Vulnerability Report Analytics In Paraxial Io By the end of this guide, you’ll understand the key components of a vulnerability assessment report, how an effective report empowers you to manage risks efficiently, and how it contributes to long term security and business growth. This report will show vulnerabilities found, their severity, what host they are on, and the location of the vulenrabilities. from here you can export data in multiple available formats. In this article, we will discuss the essential parts of an effective vulnerability report and share valuable tips and tricks to improve its quality. Our reports are template based so you can easily change report settings and rerun reports to get different views of your vulnerability data and security risk. you can configure existing report templates and create new ones.
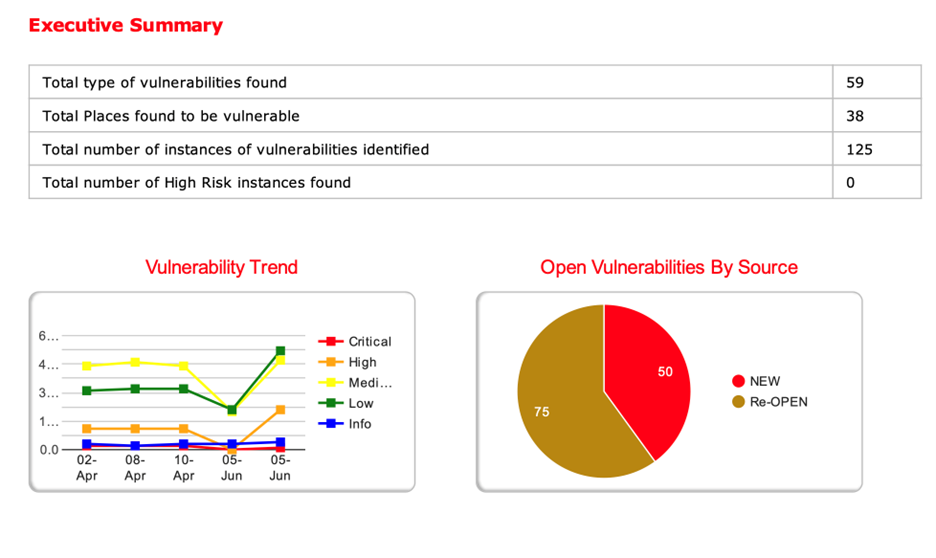
Vulnerability Assessment Report Qualysec In this article, we will discuss the essential parts of an effective vulnerability report and share valuable tips and tricks to improve its quality. Our reports are template based so you can easily change report settings and rerun reports to get different views of your vulnerability data and security risk. you can configure existing report templates and create new ones. Read this guide to find out all you need about vulnerability assessment reporting and how to demonstrate your security posture. Understand the key components of a high quality vulnerability report. learn how to reproduce and document vulnerabilities using technical proofs (commands, scripts, or video pocs). The vulnerability report starts by clearly summarizing the assessment and the key findings regarding assets, security flaws, and overall risk. it then goes into more detail about the most relevant vulnerabilities for the program owners and how they could impact various aspects of the organization. Understanding how to read and interpret a vulnerability report example is essential for stakeholders, including it teams, developers, and management, to effectively prioritize and address security risks.
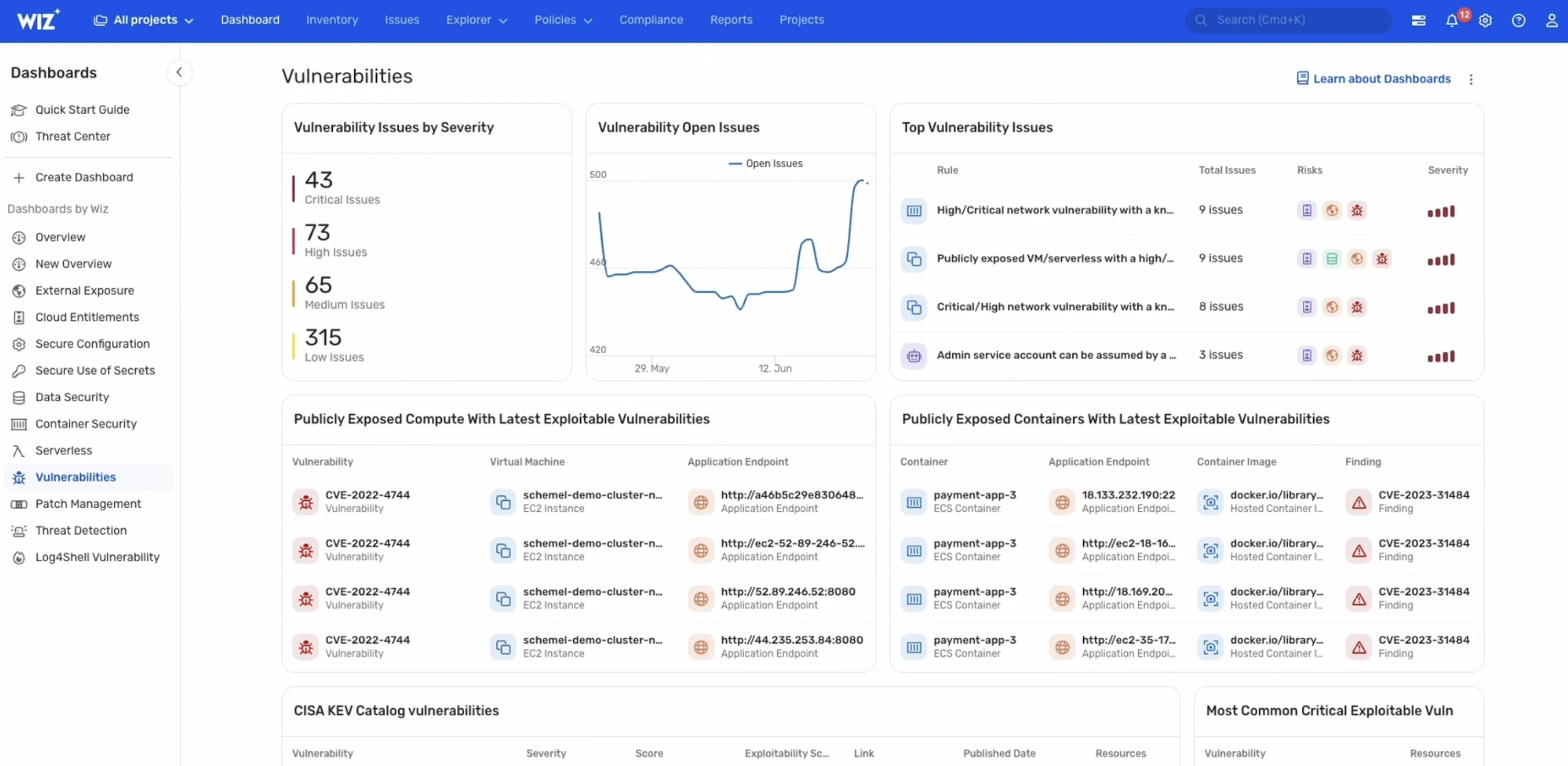
What Is A Vulnerability Scanning Report Definition And Tips Wiz Read this guide to find out all you need about vulnerability assessment reporting and how to demonstrate your security posture. Understand the key components of a high quality vulnerability report. learn how to reproduce and document vulnerabilities using technical proofs (commands, scripts, or video pocs). The vulnerability report starts by clearly summarizing the assessment and the key findings regarding assets, security flaws, and overall risk. it then goes into more detail about the most relevant vulnerabilities for the program owners and how they could impact various aspects of the organization. Understanding how to read and interpret a vulnerability report example is essential for stakeholders, including it teams, developers, and management, to effectively prioritize and address security risks.
The Global Cyber Vulnerability Report Premiumjs Store The vulnerability report starts by clearly summarizing the assessment and the key findings regarding assets, security flaws, and overall risk. it then goes into more detail about the most relevant vulnerabilities for the program owners and how they could impact various aspects of the organization. Understanding how to read and interpret a vulnerability report example is essential for stakeholders, including it teams, developers, and management, to effectively prioritize and address security risks.
How To Read A Vulnerability Assessment Report Indusface
Comments are closed.