Vulnerability Management Vs Vulnerability Assessment Why You Need Both
Vulnerability Assessment Vs Penetration Testing Explore the key differences between vulnerability management and assessment, including definitions, best practices, and how modern security solutions combine both for stronger protection. While a vulnerability scan is a single point in time check, vulnerability management is an ongoing, dynamic process. it helps security teams manage and remediate weaknesses discovered during a scan.

Vulnerability Management Vs Vulnerability Assessment Comparison Vulnerability assessment and vulnerability management serve different purposes in your security strategy. understanding these differences helps you use both effectively. In summary, vulnerability management and vulnerability assessment are both critical components of an effective cybersecurity strategy. while they share some similarities, they differ in their approach, scope, and ongoing nature. Both vulnerability management and vulnerability assessment play pivotal roles. they are twofold processes that together form a cohesive line of defense against cyber threats. vulnerability assessments are the foundation, providing an initial understanding of potential vulnerabilities and risks. While vulnerability assessments focus on identifying security flaws and vulnerabilities in the network and it infrastructure, vulnerability management involves the ongoing process of identifying, prioritizing, and remedying these vulnerabilities to enhance overall cybersecurity.
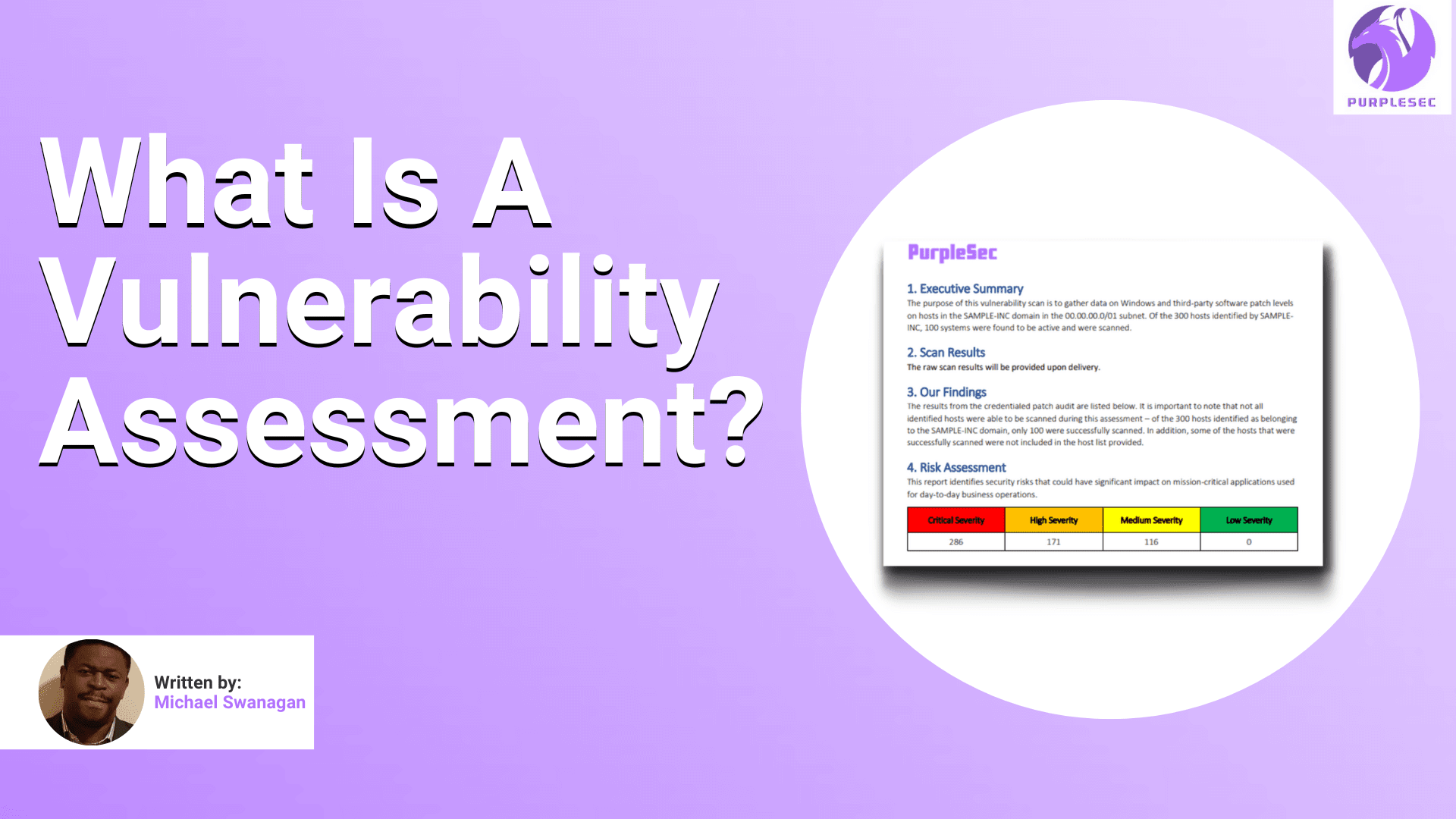
What Is A Vulnerability Assessment A Complete Guide For 2023 Both vulnerability management and vulnerability assessment play pivotal roles. they are twofold processes that together form a cohesive line of defense against cyber threats. vulnerability assessments are the foundation, providing an initial understanding of potential vulnerabilities and risks. While vulnerability assessments focus on identifying security flaws and vulnerabilities in the network and it infrastructure, vulnerability management involves the ongoing process of identifying, prioritizing, and remedying these vulnerabilities to enhance overall cybersecurity. Vulnerability assessment provides the critical first step in identifying potential weaknesses, while vulnerability management ensures that these vulnerabilities are addressed effectively and continuously. While vulnerability assessment is a one time or periodic scan of it infrastructure to identify security vulnerabilities, vulnerability management is a continuous process that aims to keep computer systems, networks, and enterprise applications safe from cyberattacks and data breaches. Vulnerability assessment is the first step in vulnerability management. this means assessing the network and endpoint infrastructure of an organization for potential vulnerabilities. scanning and assessment are varied according to the part of the network infrastructure being assessed. While vulnerability assessment focuses on identifying weaknesses in an organization’s systems and networks, vulnerability management involves remediation and mitigation of these vulnerabilities on an ongoing basis. both approaches are necessary to ensure maximum protection against cyber threats.

Tul Si Vulnerability assessment provides the critical first step in identifying potential weaknesses, while vulnerability management ensures that these vulnerabilities are addressed effectively and continuously. While vulnerability assessment is a one time or periodic scan of it infrastructure to identify security vulnerabilities, vulnerability management is a continuous process that aims to keep computer systems, networks, and enterprise applications safe from cyberattacks and data breaches. Vulnerability assessment is the first step in vulnerability management. this means assessing the network and endpoint infrastructure of an organization for potential vulnerabilities. scanning and assessment are varied according to the part of the network infrastructure being assessed. While vulnerability assessment focuses on identifying weaknesses in an organization’s systems and networks, vulnerability management involves remediation and mitigation of these vulnerabilities on an ongoing basis. both approaches are necessary to ensure maximum protection against cyber threats.

Vulnerability Management Vs Vulnerability Assessment Cyber Sainik Vulnerability assessment is the first step in vulnerability management. this means assessing the network and endpoint infrastructure of an organization for potential vulnerabilities. scanning and assessment are varied according to the part of the network infrastructure being assessed. While vulnerability assessment focuses on identifying weaknesses in an organization’s systems and networks, vulnerability management involves remediation and mitigation of these vulnerabilities on an ongoing basis. both approaches are necessary to ensure maximum protection against cyber threats.

Understanding The Difference Vulnerability Management Vs Vulnerability
Comments are closed.