Vulnerability Management Program Tips To Build A Better Strategy

How To Build An Effective Vulnerability Management Program A vulnerability management program scans, patches & documents software vulnerabilities. here's our advice to improve your strategy for better it security. Learn top vulnerability management, scanning, and remediation best practices to protect your systems and reduce security risks effectively. read today!.

Tips For A Better Enterprise Vulnerability Management Program Ppt Example Learn what is a vulnerability management plan and how to create it, measure key kpis, and strengthen security posture for lasting organizational protection. Let's look at how to improve your organization's vulnerability management, whether it already has a vulnerability management program or is thinking about starting one. A successful vulnerability management program isn't built overnight, but the steps outlined here provide a practical framework that addresses the real world challenges organizations face. Security experts share their best advice for the essential ingredients of a solid vulnerability management program, including foundational elements to put in place, workflows to establish,.

4 Steps To A Winning Vulnerability Management Program 2 Coding With A successful vulnerability management program isn't built overnight, but the steps outlined here provide a practical framework that addresses the real world challenges organizations face. Security experts share their best advice for the essential ingredients of a solid vulnerability management program, including foundational elements to put in place, workflows to establish,. In this article, we provide a full view of the vulnerability challenges facing organizations today that align with their business model. it will walk you through the steps of building a vulnerability management program. In this guide, we’ll walk through what vulnerability management really means in practice, how it differs from a basic vulnerability assessment, and the key steps involved in building a program that actually works. Learn about the best practices for vulnerability management and how to protect your business from cyber threats. read our ultimate guide now. Learn how to build an effective vulnerability management program with best practices and tools for asset discovery, risk prioritization, and streamlined remediation.
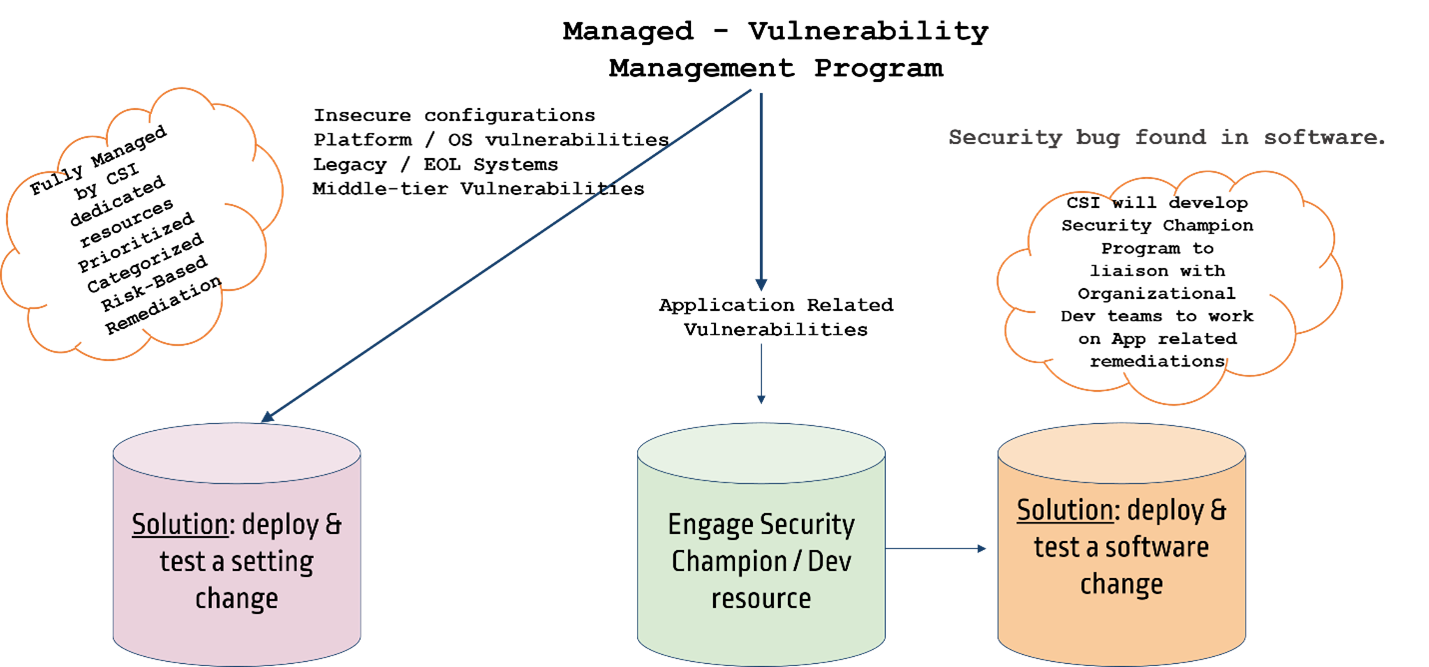
Managed Vulnerability Management Program Cybersecurityinc In this article, we provide a full view of the vulnerability challenges facing organizations today that align with their business model. it will walk you through the steps of building a vulnerability management program. In this guide, we’ll walk through what vulnerability management really means in practice, how it differs from a basic vulnerability assessment, and the key steps involved in building a program that actually works. Learn about the best practices for vulnerability management and how to protect your business from cyber threats. read our ultimate guide now. Learn how to build an effective vulnerability management program with best practices and tools for asset discovery, risk prioritization, and streamlined remediation.
5 Steps To Build An Effective Vulnerability Management Program Learn about the best practices for vulnerability management and how to protect your business from cyber threats. read our ultimate guide now. Learn how to build an effective vulnerability management program with best practices and tools for asset discovery, risk prioritization, and streamlined remediation.

Vulnerability Management Programs Codingwithcookie
Comments are closed.