Vulnerability Management Lifecycle Tool System Podcast
Vulnerability Management Lifecycle 5 Step Process Explained Get familiar with some basic concepts of vulnerability management, and understand in a broader perspective how organizations should focus on these areas. Explore diverse perspectives on vulnerability management with structured content covering tools, strategies, challenges, and industry specific applications.
Vulnerability Management Lifecycle A Comprehensive Guide King Obi On today’s episode, we’ll demystify vulnerability management by defining some context, outlining an effective vulnerability management program, discussing potential challenges, and tying it all back to compliance. Chris shares insights on the evolving landscape of cybersecurity, discussing software supply chain threats, vulnerability management, relationships between security and development, and the future impacts of ai. Master the vulnerability management lifecycle with insights on identification, detection, and the role of sanernow’s scanning capabilities. In each episode, nopsec’s ceo lisa xu will interview industry experts and leading practitioners about what can be done to prepare for the future of vulnerability management. this show is brought to you by nopsec . in this episode, we talk with hussein syed, ciso of rwjbarnabas health.

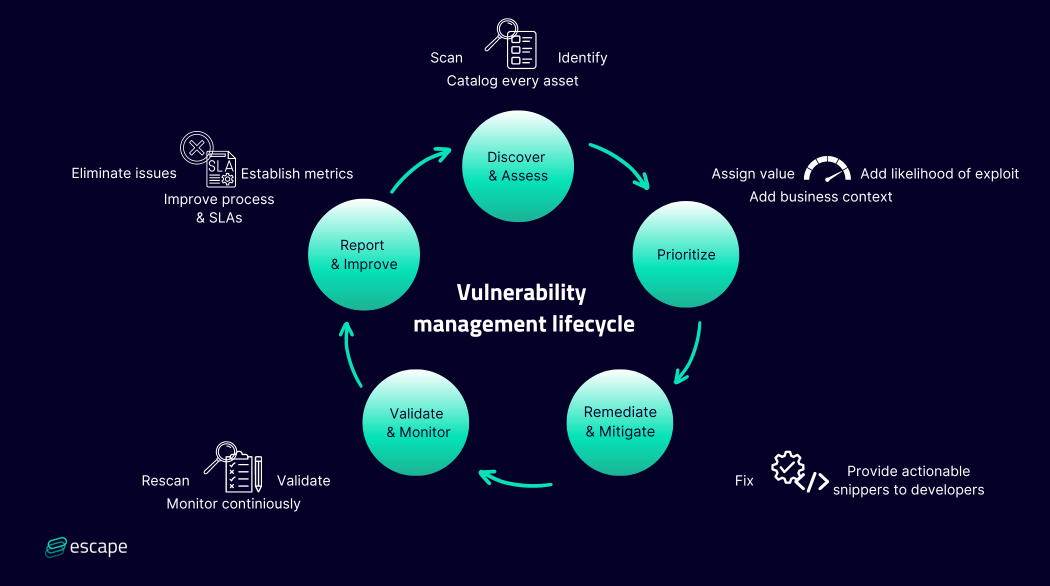
Vulnerability Management Lifecycle Communicate Master the vulnerability management lifecycle with insights on identification, detection, and the role of sanernow’s scanning capabilities. In each episode, nopsec’s ceo lisa xu will interview industry experts and leading practitioners about what can be done to prepare for the future of vulnerability management. this show is brought to you by nopsec . in this episode, we talk with hussein syed, ciso of rwjbarnabas health. By regularly examining the entire vulnerability lifecycle and looking for ways to evolve and improve, you can proactively defend against any kind of vulnerability an attacker could use to threaten your organization. Learn how to mature your vulnerability management (vm) program success by following a consistent “lifecycle”. in this session, we talk through optimizing the activities required to take a “risk based” approach to prioritize remediation and mitigation efforts. New vulnerabilities can arise in a network at any time, so the vulnerability management lifecycle is a continuous loop rather than a series of distinct events. each round of the lifecycle feeds directly into the next. The guide provides in depth coverage of the full vulnerability management lifecycle including the preparation phase, the vulnerability identification scanning phase, the reporting phase, and remediation phase.

How To Set Up A Good Vulnerability Management Lifecycle Geek911 By regularly examining the entire vulnerability lifecycle and looking for ways to evolve and improve, you can proactively defend against any kind of vulnerability an attacker could use to threaten your organization. Learn how to mature your vulnerability management (vm) program success by following a consistent “lifecycle”. in this session, we talk through optimizing the activities required to take a “risk based” approach to prioritize remediation and mitigation efforts. New vulnerabilities can arise in a network at any time, so the vulnerability management lifecycle is a continuous loop rather than a series of distinct events. each round of the lifecycle feeds directly into the next. The guide provides in depth coverage of the full vulnerability management lifecycle including the preparation phase, the vulnerability identification scanning phase, the reporting phase, and remediation phase.

Understanding The Intricacies Of Vulnerability Management Lifecycle New vulnerabilities can arise in a network at any time, so the vulnerability management lifecycle is a continuous loop rather than a series of distinct events. each round of the lifecycle feeds directly into the next. The guide provides in depth coverage of the full vulnerability management lifecycle including the preparation phase, the vulnerability identification scanning phase, the reporting phase, and remediation phase.
Vulnerability Management Lifecycle A Comprehensive Guide
Comments are closed.