Vulnerability Management In Microsoft 365
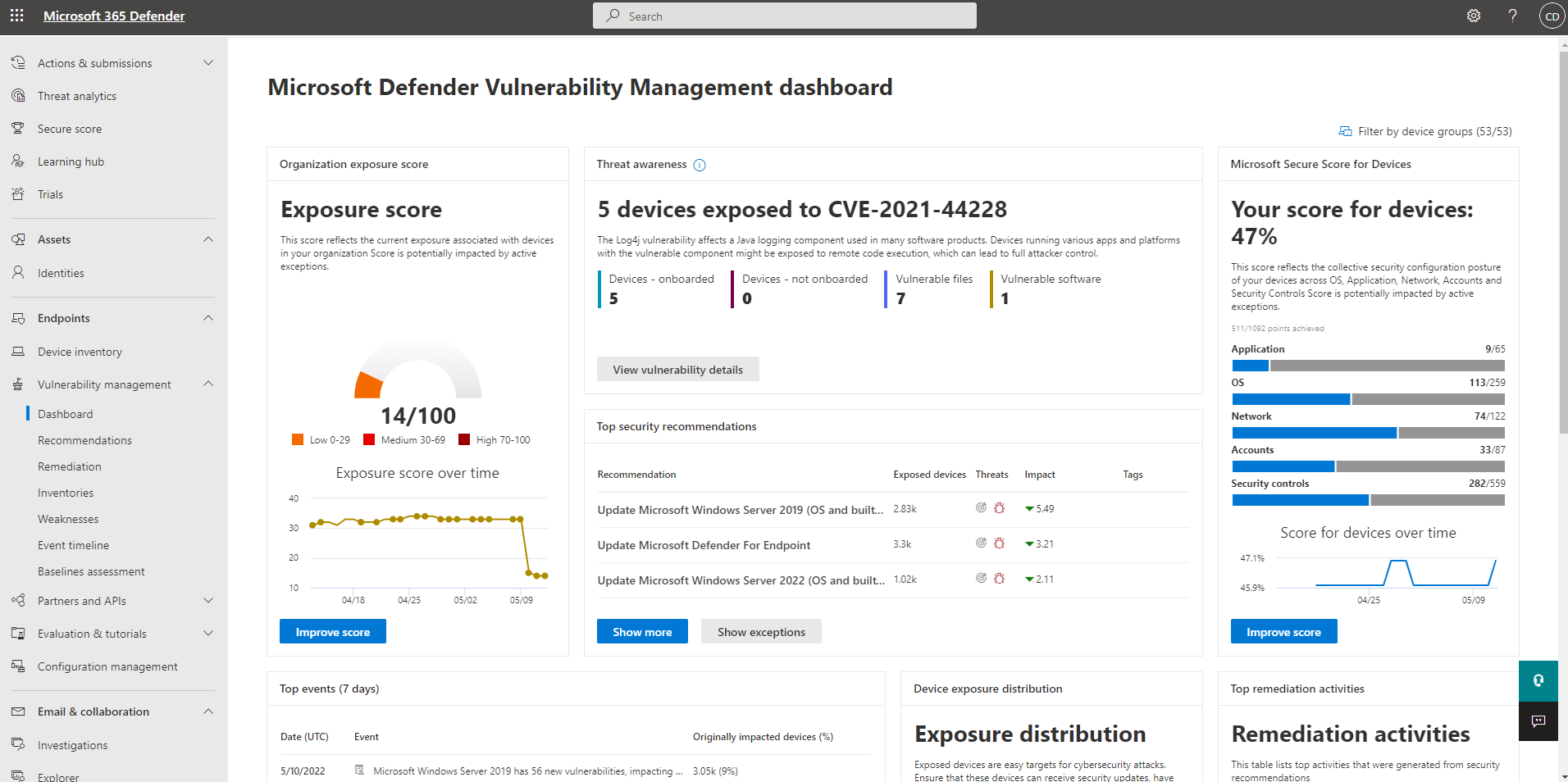
Microsoft Defender Vulnerability Management Dashboard Microsoft Learn The vulnerability management section in the microsoft defender portal is now located under exposure management. with this change, you can now consume and manage security exposure data and vulnerability data in a unified location, to enhance your existing vulnerability management features. For most businesses, microsoft 365 business premium provides sufficient vulnerability management capabilities while offering excellent value for collaboration and security features.

Microsoft Defender Portal Overview Unified Security Operations This article, provides an overview the routine vulnerability scanning and remediation process in microsoft 365. Welcome to our comprehensive guide to microsoft's powerful suite of vulnerability management systems. Each piece of software can have vulnerabilities that create security risks. Leveraging microsoft threat intelligence, breach likelihood predictions, business contexts, and devices assessments, defender vulnerability management rapidly and continuously prioritizes the biggest vulnerabilities on your most critical assets and provides security recommendations to mitigate risk.
Microsoft Defender Vulnerability Management Microsoft Learn Each piece of software can have vulnerabilities that create security risks. Leveraging microsoft threat intelligence, breach likelihood predictions, business contexts, and devices assessments, defender vulnerability management rapidly and continuously prioritizes the biggest vulnerabilities on your most critical assets and provides security recommendations to mitigate risk. In this video, we'll show you how to use the built in vulnerability management capabilities of microsoft 365 to identify and remediate vulnerabilities in your environment. The vulnerability management section in the microsoft defender portal is now located under exposure management. with this change, you can now consume and manage security exposure data and vulnerability data in a unified location, to enhance your existing vulnerability management features. How do microsoft online services conduct vulnerability management? no matter how well a system is designed, its security posture can degrade over time. machines can go unpatched, inadvertent configuration changes can be introduced, and regressions to security code can accumulate. We recommend the following actions be taken: apply appropriate updates provided by microsoft to vulnerable systems immediately after appropriate testing. (m1051: update software) safeguard 7.1: establish and maintain a vulnerability management process: establish and maintain a documented vulnerability management process for enterprise assets. review and update documentation annually, or when.
New Threat And Vulnerability Management Experiences In Microsoft 365 In this video, we'll show you how to use the built in vulnerability management capabilities of microsoft 365 to identify and remediate vulnerabilities in your environment. The vulnerability management section in the microsoft defender portal is now located under exposure management. with this change, you can now consume and manage security exposure data and vulnerability data in a unified location, to enhance your existing vulnerability management features. How do microsoft online services conduct vulnerability management? no matter how well a system is designed, its security posture can degrade over time. machines can go unpatched, inadvertent configuration changes can be introduced, and regressions to security code can accumulate. We recommend the following actions be taken: apply appropriate updates provided by microsoft to vulnerable systems immediately after appropriate testing. (m1051: update software) safeguard 7.1: establish and maintain a vulnerability management process: establish and maintain a documented vulnerability management process for enterprise assets. review and update documentation annually, or when.
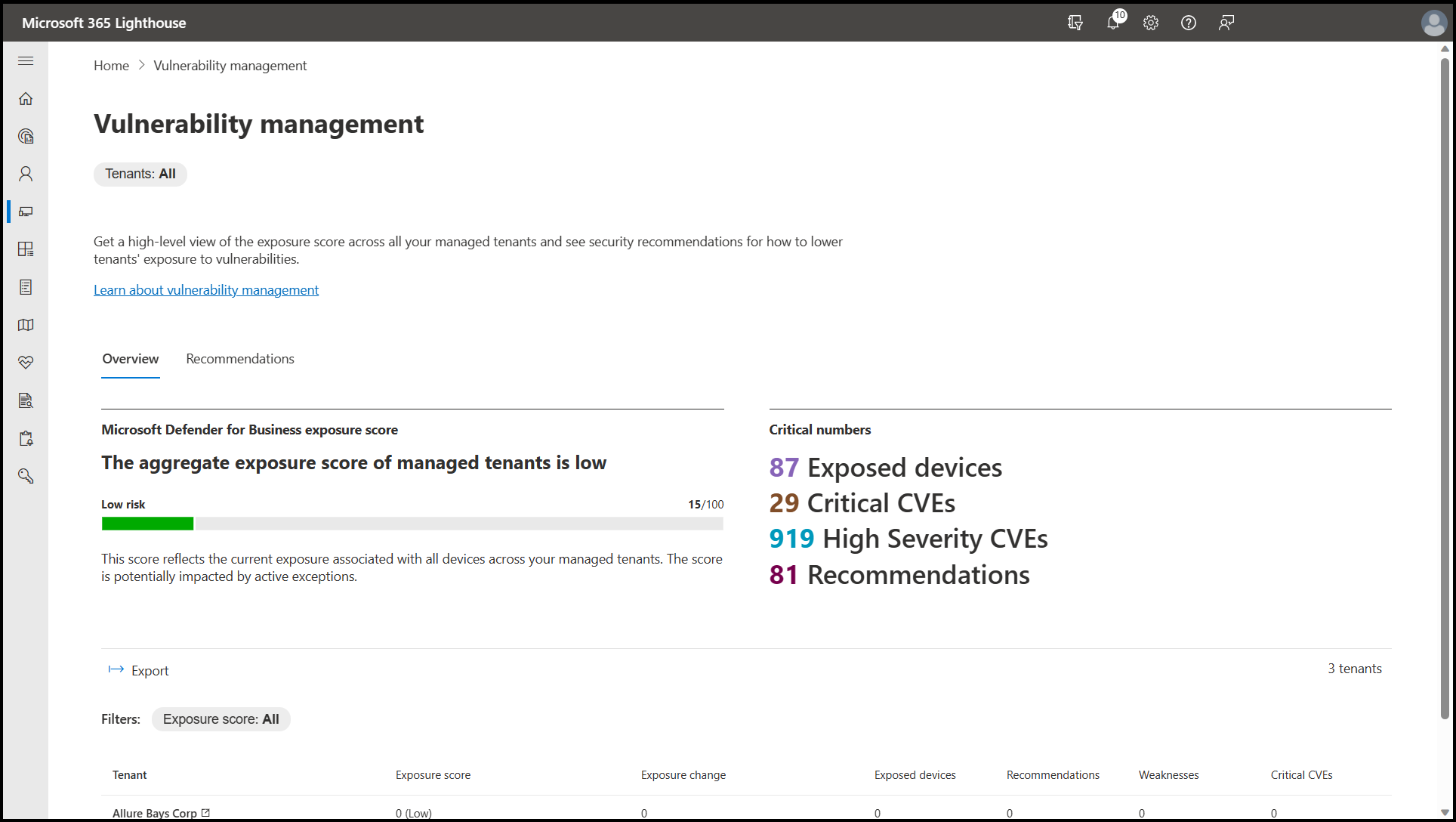
Overview Of The Vulnerability Management Page In Microsoft 365 How do microsoft online services conduct vulnerability management? no matter how well a system is designed, its security posture can degrade over time. machines can go unpatched, inadvertent configuration changes can be introduced, and regressions to security code can accumulate. We recommend the following actions be taken: apply appropriate updates provided by microsoft to vulnerable systems immediately after appropriate testing. (m1051: update software) safeguard 7.1: establish and maintain a vulnerability management process: establish and maintain a documented vulnerability management process for enterprise assets. review and update documentation annually, or when.
Comments are closed.