Vulnerability Management Guard Against Script Attacks

Risk Based Vulnerability Management Medium To protect your business from script based attacks, you need to learn how to handle vulnerabilities. after carefully following the steps in this guide, you can greatly improve the security of your organization. This article explains how to prevent script injection attacks using single quote escaping.

Vulnerability Management System Avoiding The Threat Of Cyberattacks Cross site scripting attacks may occur anywhere that possibly malicious users are allowed to post unregulated material to a trusted website for the consumption of other valid users. Without proper safeguards, applications can be vulnerable to attacks such as cross site scripting (xss), cross site request forgery (csrf), and sql injection. in this post, we'll cover what these vulnerabilities are and how to mitigate them effectively. Xss or cross site scripting is a web application vulnerability that allows an attacker to inject vulnerable javascript content into a website. an attacker exploits this by injecting on websites that doesn't or poorly sanitizes user controlled content. Discover multiple methods for preventing cross site scripting (xss) attacks, such as blocking html inputs, sanitizing data, and using web application firewalls (wafs).
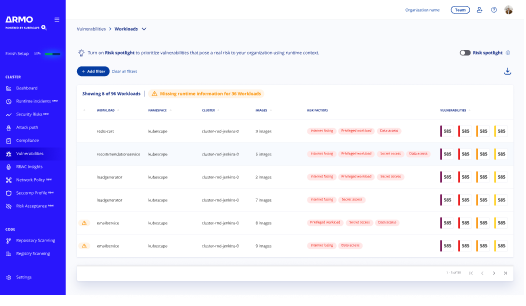
Runtime Based Vulnerability Management Solution Xss or cross site scripting is a web application vulnerability that allows an attacker to inject vulnerable javascript content into a website. an attacker exploits this by injecting on websites that doesn't or poorly sanitizes user controlled content. Discover multiple methods for preventing cross site scripting (xss) attacks, such as blocking html inputs, sanitizing data, and using web application firewalls (wafs). Learn about cross site scripting (xss) and sql injection attacks, two of the most common web vulnerabilities, and discover best practices for preventing them. Learn what cross site scripting (xss) vulnerability is, how it spreads, and how to detect and remove it before it impacts your systems. Among the myriad threats they face, cross site scripting (xss) stands out due to its ability to compromise user data and disrupt services. this article delves into innovative approaches for. Learn about cross site scripting (xss) attacks and how they work. check out its examples, types, impacts, and ways to prevent it.

Vulnerability Management Strategies Fortify Your Defense Learn about cross site scripting (xss) and sql injection attacks, two of the most common web vulnerabilities, and discover best practices for preventing them. Learn what cross site scripting (xss) vulnerability is, how it spreads, and how to detect and remove it before it impacts your systems. Among the myriad threats they face, cross site scripting (xss) stands out due to its ability to compromise user data and disrupt services. this article delves into innovative approaches for. Learn about cross site scripting (xss) attacks and how they work. check out its examples, types, impacts, and ways to prevent it.
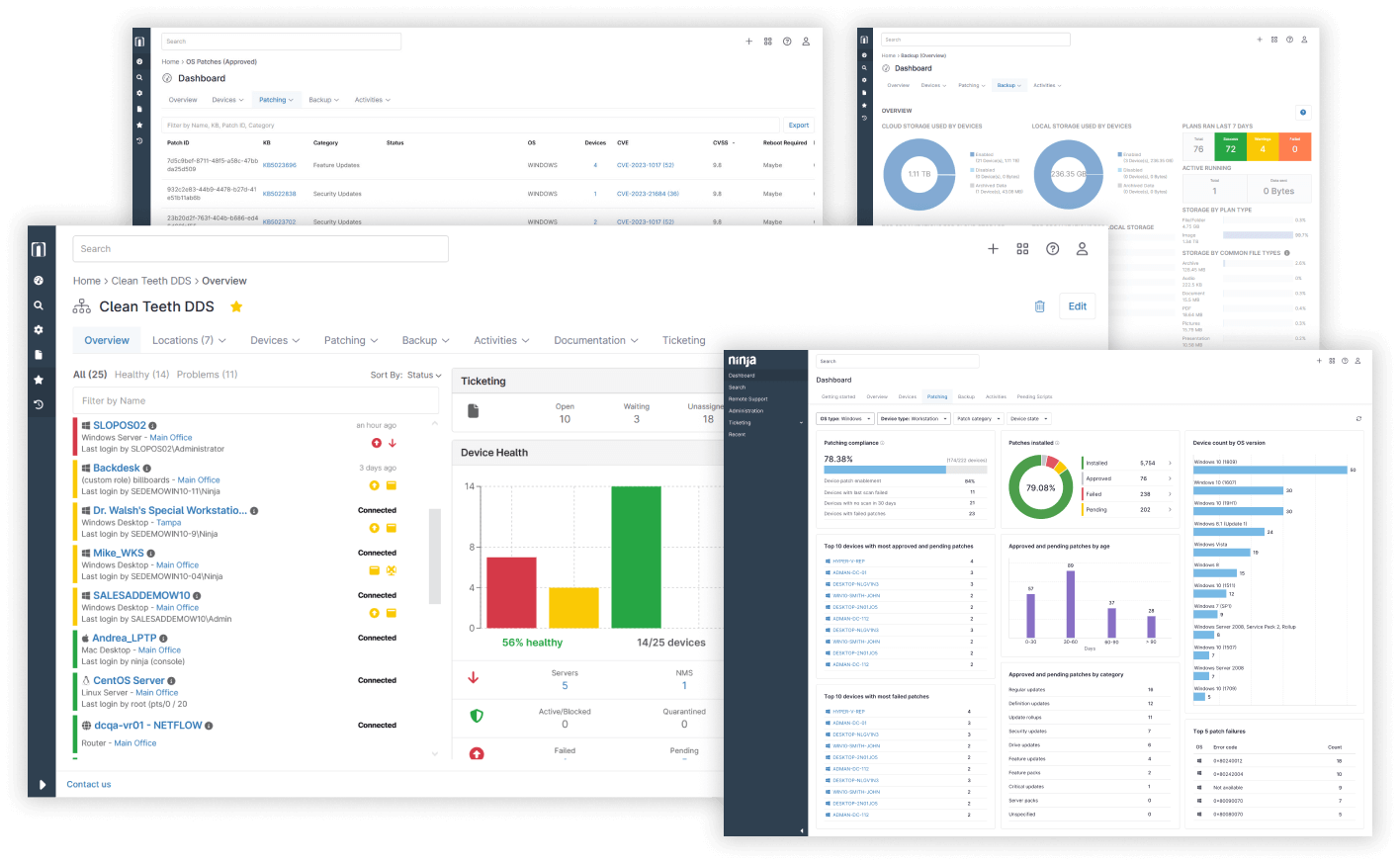
Vulnerability Management Tool Best Rated Software Ninjaone Among the myriad threats they face, cross site scripting (xss) stands out due to its ability to compromise user data and disrupt services. this article delves into innovative approaches for. Learn about cross site scripting (xss) attacks and how they work. check out its examples, types, impacts, and ways to prevent it.

What Is Vulnerability Management Cyber Security Element Four
Comments are closed.