Vulnerability Insights With Power Bi

Power Bi Security Solutions What Should Leaders Prioritize It consolidates crucial security data into actionable insights, enabling proactive risk management. the dashboard provides real time monitoring of threats, incidents, and vulnerabilities, helping security teams respond swiftly to potential breaches. A collection of dashboards, templates, api's and power bi code for vulnerability management and analysis securitybagel vulnbagel.

Vulnerability Insights With Power Bi With these 12 free power bi dashboards for microsoft defender, you can transform how you monitor, manage, and mitigate cybersecurity threats. Are your microsoft power bi reports leaking sensitive data? discover how hidden semantic models expose pii and download our free power bi analyzer tool. Visualize and analyze historical patterns in global cybersecurity threats across a 10 year period, highlighting year over year shifts in volume, severity, and geography. quantify the financial and. The tvm template collection provides comprehensive vulnerability management reporting through power bi dashboards that integrate directly with microsoft defender for endpoint apis.

Data Leakage Vulnerability Discovered In Microsoft Power Bi Service Visualize and analyze historical patterns in global cybersecurity threats across a 10 year period, highlighting year over year shifts in volume, severity, and geography. quantify the financial and. The tvm template collection provides comprehensive vulnerability management reporting through power bi dashboards that integrate directly with microsoft defender for endpoint apis. From threat intelligence and vulnerability management to compliance monitoring, we deliver dashboards that help you gain immense benefits from power bi security dashboards across touchpoints. take quick action against security breaches and unauthorized access attempts through breach alerts. Microsoft power bi can leverage vulncheck kev api as an intelligence source for known exploited vulnerabilities. include timely evidence of cve exploitation such as software vendor, products, reference articles and vulncheck xdb links in your powerbi applications. Learn to create custom security and threat dashboards for an overview of multiple data sources in power bi with this guide. In this article, we’ll explore how a power bi based cybersecurity dashboard works, its key components, advantages, best practices, and answers to common questions from it and data professionals.
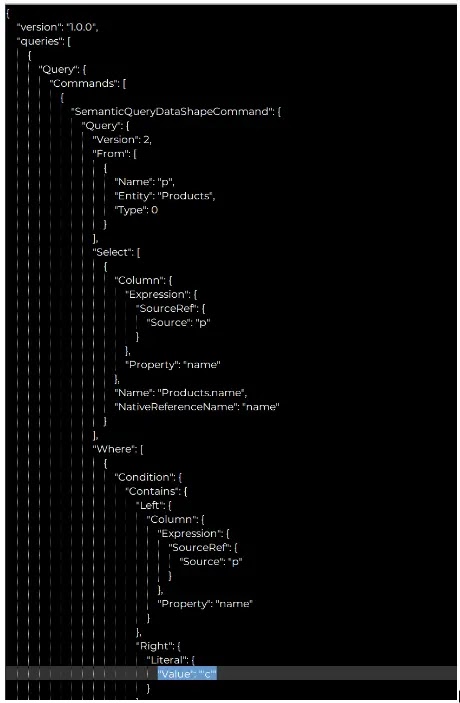
Microsoft Power Bi Vulnerability Let Attackers Access Organizations From threat intelligence and vulnerability management to compliance monitoring, we deliver dashboards that help you gain immense benefits from power bi security dashboards across touchpoints. take quick action against security breaches and unauthorized access attempts through breach alerts. Microsoft power bi can leverage vulncheck kev api as an intelligence source for known exploited vulnerabilities. include timely evidence of cve exploitation such as software vendor, products, reference articles and vulncheck xdb links in your powerbi applications. Learn to create custom security and threat dashboards for an overview of multiple data sources in power bi with this guide. In this article, we’ll explore how a power bi based cybersecurity dashboard works, its key components, advantages, best practices, and answers to common questions from it and data professionals.

Microsoft Power Bi Vulnerability Let Attackers Access Organizations Learn to create custom security and threat dashboards for an overview of multiple data sources in power bi with this guide. In this article, we’ll explore how a power bi based cybersecurity dashboard works, its key components, advantages, best practices, and answers to common questions from it and data professionals.
Comments are closed.