Vulnerability Assessment Pdf Secure Communication Computer Security

Security Policy 24 Vulnerability Assessment Pdf Information Goal driven test focused on identifying all possible routes of entry an attacker could use to gain unauthorized entry into the target. identifies the potential damage and further internal compromise an attacker could carry out once they are past the perimeter. Ain (school of computing and informatics, malaysia) description: vulnerability assessment and risk management are critical components of cybersecurity, focusing on identifying, evaluating, and mitigating.

Vulnerability And Threat Assessment Pdf Image Scanner Threat Everyday professional hackers crack the security and take the advantage of vulnerabilities to access the top secret and confidential data. to avoid these threats we proposed a solution named. The intention of this system is to reduce susceptibility using vulnerability assessment algorithm which covers the process of identifying and ranking the vulnerabilities in a system while ensuring required information is transferred securely without any failure in the middle of transaction. Even with adequate knowledge about the threats, risks and vulnerabilities associated with information processing and communication networks, adequate security cannot be achieved unless security measures are systematically applied in accordance with relevant security policies. To identify and analyze at least five critical vulnerabilities within the network, assess their impact, and propose effective mitigation strategies to enhance security.
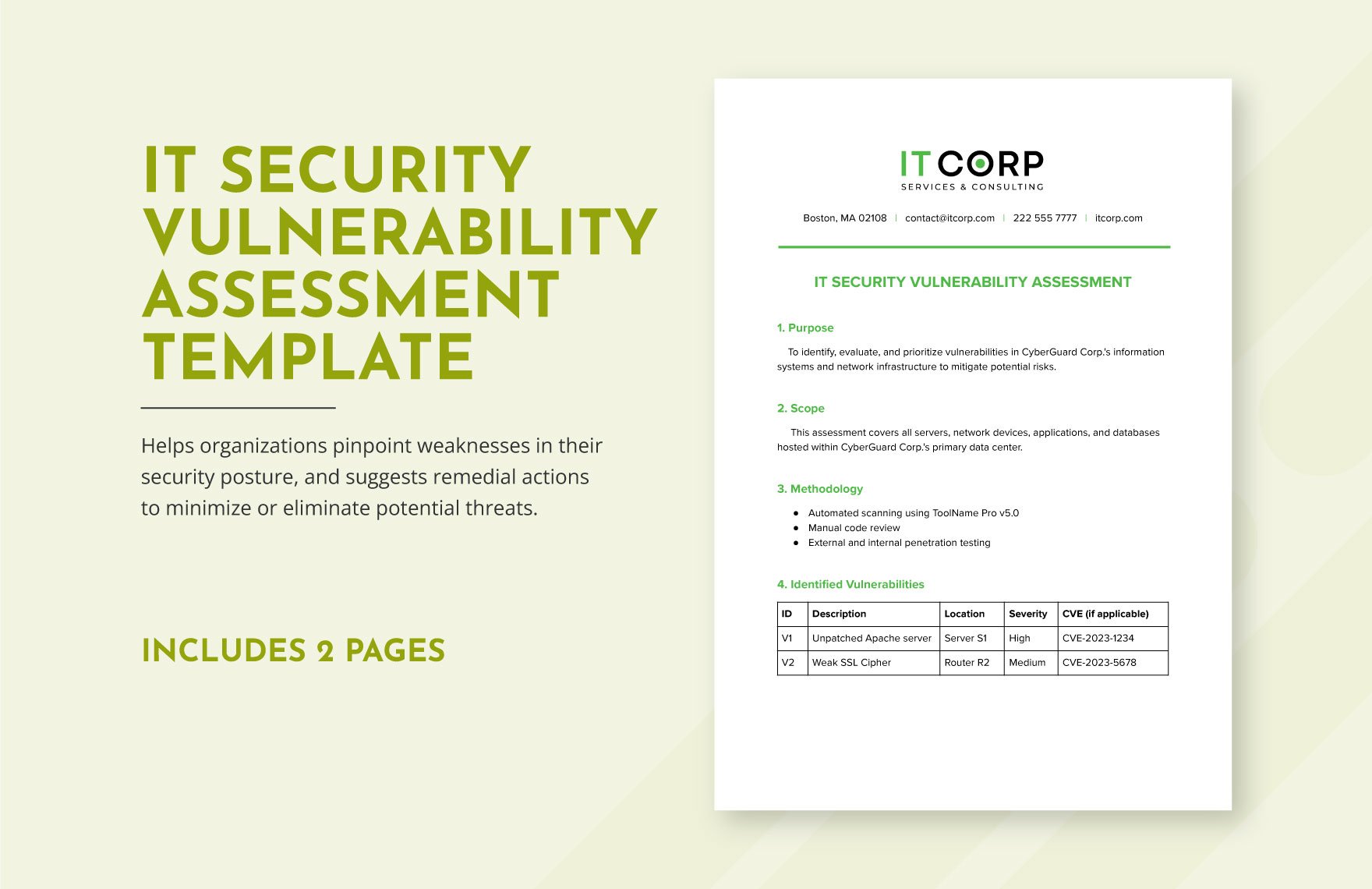
It Security Vulnerability Assessment Template In Word Pdf Google Docs Even with adequate knowledge about the threats, risks and vulnerabilities associated with information processing and communication networks, adequate security cannot be achieved unless security measures are systematically applied in accordance with relevant security policies. To identify and analyze at least five critical vulnerabilities within the network, assess their impact, and propose effective mitigation strategies to enhance security. Inodhini.t abstract vulnerability assessment has become an area of interest in distributed network communication which is capable of detecting the penetrations, break ins and other form of computer. Scan results the scan results provide granular detail of each vulnerability, which are categorized by their severity: critical, high, medium, and low. an expanded definition of the known threat and solutions for remediating the vulnerability are also available. The paper provides a complete overview of web application vulnerability assessment and penetration testing, emphasizing the need of proactive security measures in protecting sensitive data and preserving application integrity. In this guide, we will discuss how to select the right security testing method to meet your goals by understanding the differences between a vulnerability assessment and a penetration test.
Understanding Vulnerability Assessment Pdf Inodhini.t abstract vulnerability assessment has become an area of interest in distributed network communication which is capable of detecting the penetrations, break ins and other form of computer. Scan results the scan results provide granular detail of each vulnerability, which are categorized by their severity: critical, high, medium, and low. an expanded definition of the known threat and solutions for remediating the vulnerability are also available. The paper provides a complete overview of web application vulnerability assessment and penetration testing, emphasizing the need of proactive security measures in protecting sensitive data and preserving application integrity. In this guide, we will discuss how to select the right security testing method to meet your goals by understanding the differences between a vulnerability assessment and a penetration test.
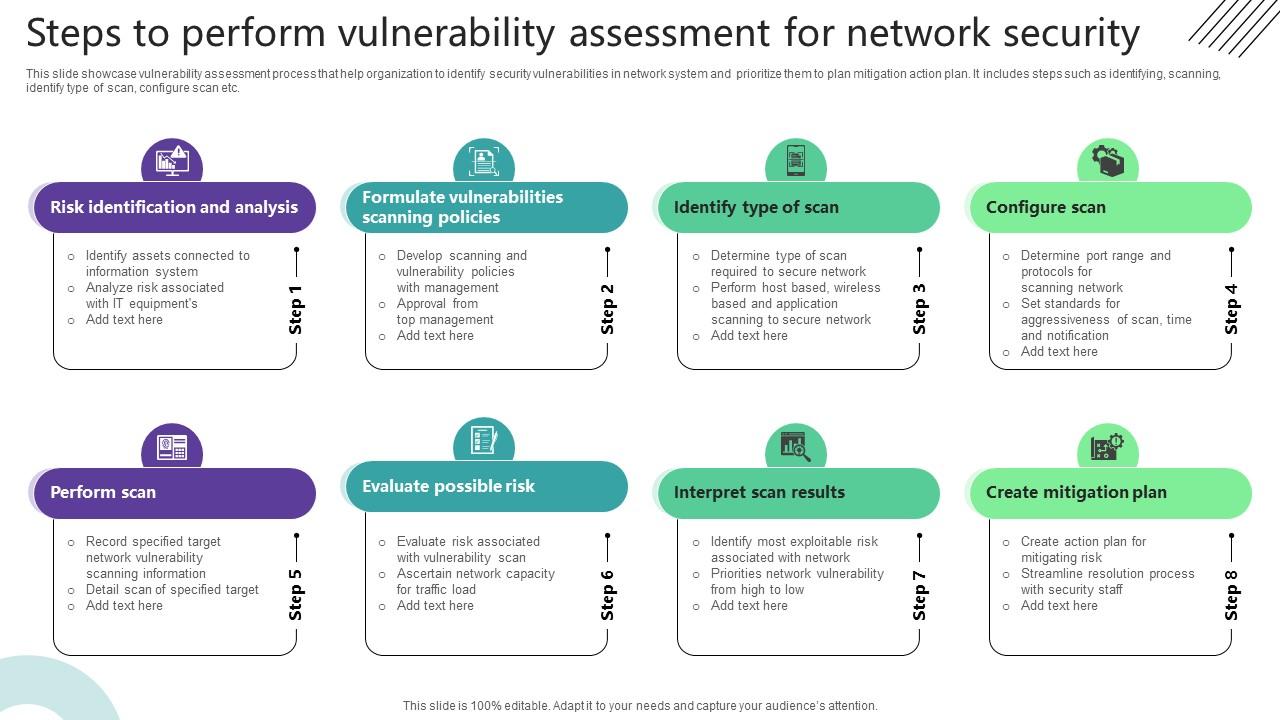
Steps To Perform Vulnerability Assessment For Network Security Ppt Template The paper provides a complete overview of web application vulnerability assessment and penetration testing, emphasizing the need of proactive security measures in protecting sensitive data and preserving application integrity. In this guide, we will discuss how to select the right security testing method to meet your goals by understanding the differences between a vulnerability assessment and a penetration test.
Comments are closed.