Vulnerability Assessment Methodology Risk Register Ppt Ideas Elements Pdf

Vulnerability Assessment Methodology Risk Register Ppt Ideas Elements Pdf The topics discussed in these slides are types of risk, description of risk, impact, risk reduction strategy, contingency plans, risk owner. this is a completely editable powerpoint presentation and is available for immediate download. Various techniques can be used including asset identification, threat modeling, vulnerability scanning, penetration testing, and risk assessment. the goal is to establish a security baseline and mitigate risks through hardening systems and ongoing monitoring. download as a pptx, pdf or view online for free.
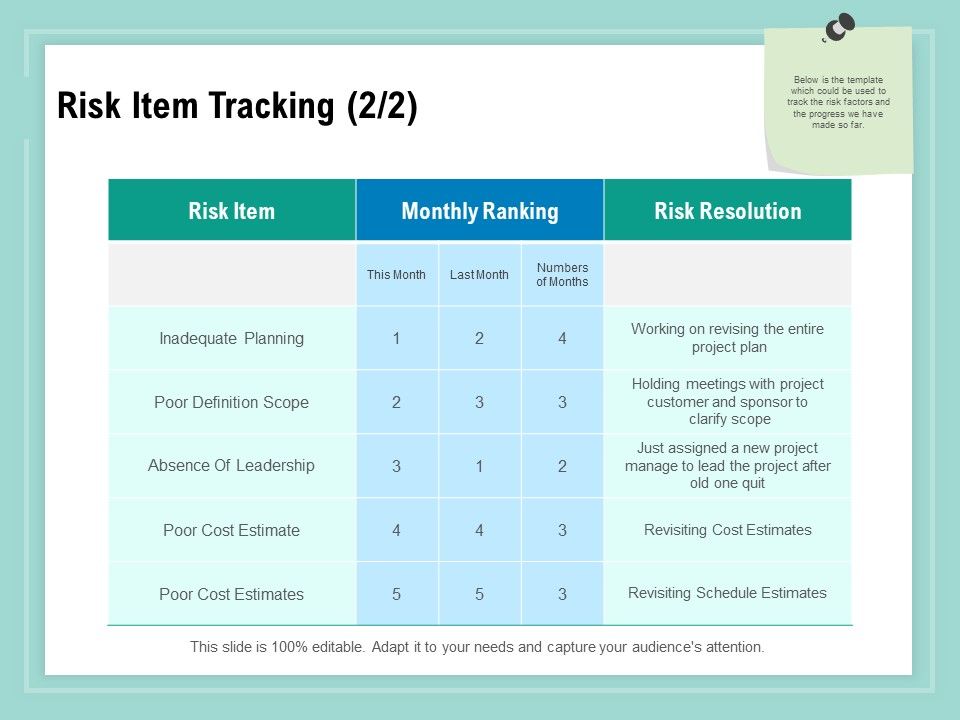
Vulnerability Assessment Methodology Risk Item Tracking Ppt Professional Fo This customizable ppt includes detailed templates, charts, and infographics that facilitate a clear understanding of vulnerability assessment processes, methodologies, and best practices. Itsrm lecture 2 free download as powerpoint presentation (.ppt), pdf file (.pdf), text file (.txt) or view presentation slides online. this document outlines the 9 step risk management methodology used for information system security and risk management. Pdf | a guide on how to do a vulnerability analysis. every step is shown explained and exemplified with a cambodian case study. | find, read and cite all the research you need on researchgate. This article serves as a hub for various threat and vulnerability management templates, each designed to streamline and enhance the efficiency of your threat and vulnerability management process.
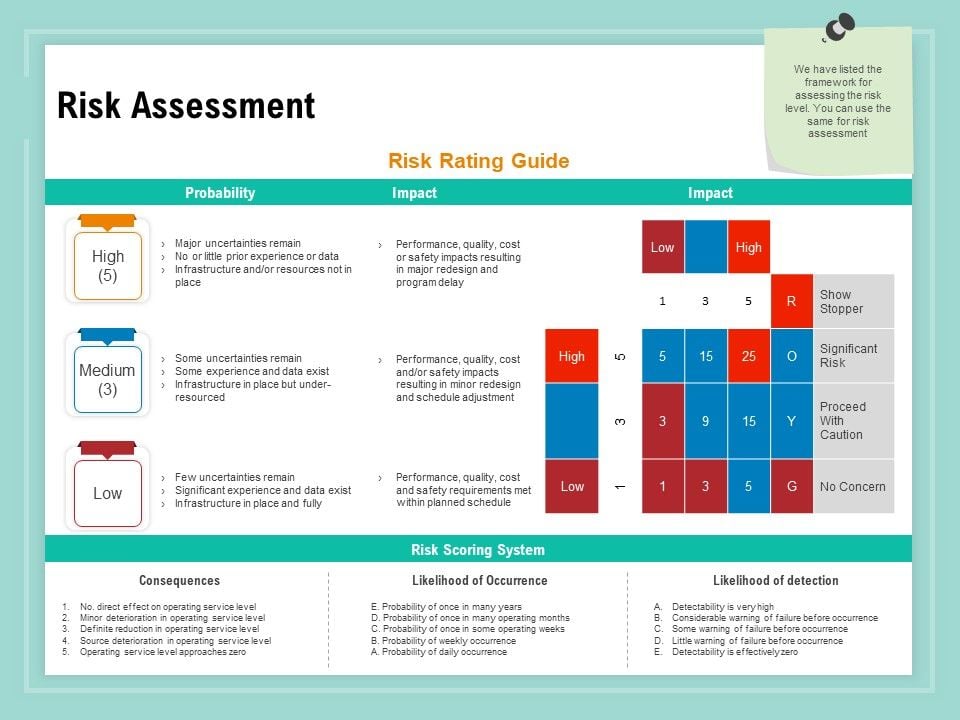
Vulnerability Assessment Methodology Risk Assessment Ppt File Samples Pdf Pdf | a guide on how to do a vulnerability analysis. every step is shown explained and exemplified with a cambodian case study. | find, read and cite all the research you need on researchgate. This article serves as a hub for various threat and vulnerability management templates, each designed to streamline and enhance the efficiency of your threat and vulnerability management process. The purpose of a vulnerability management methodology is to identify, assess, prioritise, and mitigate security vulnerabilities within an organisation’s it infrastructure systematically and proactively. At the end of this module, the trainees will be able to: explain vulnerability and risk elements of a threat and how to conduct vulnerability and risk assessment of threats. In our review of vulnerability assessment methods, we highlight comprehensive vulnerability analysis, such as the household vulnerability index discussed below, which includes discussion of both risk and coping. Download our ready made powerpoint template to illustrate the steps, components, and impact of vulnerability assessment in a well structured manner.
Comments are closed.