Vulnerability Assessment Methodology Risk Management Plan Ppt

Vulnerability Assessment Methodology Risk Management Plan Ppt Following slide shows threat identification and vulnerability impact assessment. it covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Enhance your cybersecurity strategy with our customizable vulnerability management powerpoint presentations. educate your team on identifying, assessing, and mitigating risks effectively.
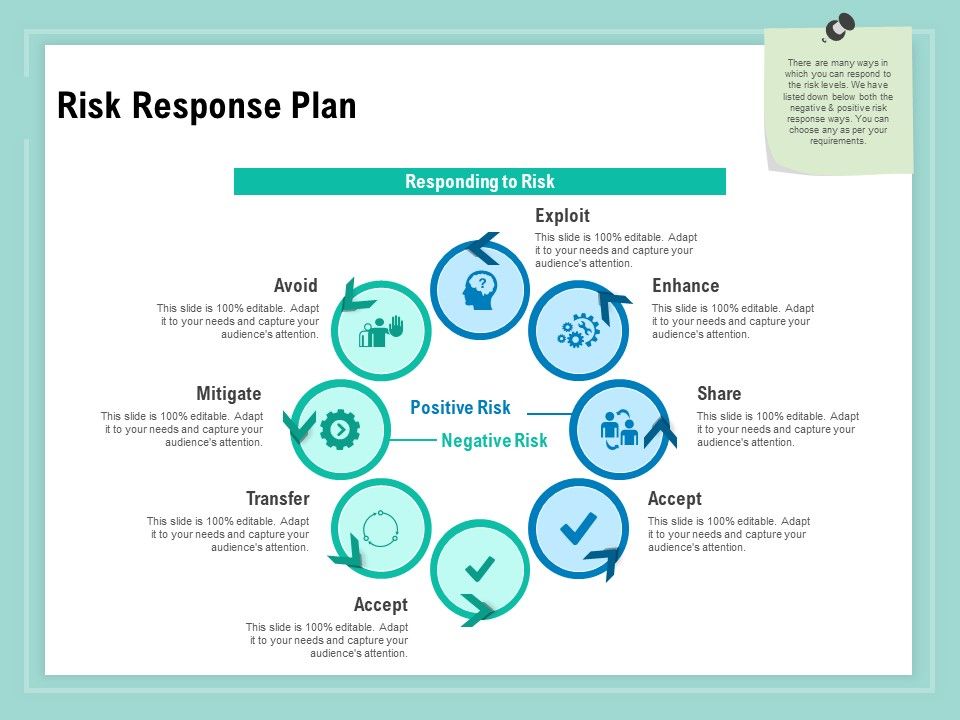
Vulnerability Assessment Methodology Risk Response Plan Ppt Pictures Pdf Various techniques can be used including asset identification, threat modeling, vulnerability scanning, penetration testing, and risk assessment. the goal is to establish a security baseline and mitigate risks through hardening systems and ongoing monitoring. download as a pptx, pdf or view online for free. Download our ready made powerpoint template to illustrate the steps, components, and impact of vulnerability assessment in a well structured manner. Download this entirely editable template on vulnerability management will let you draft visually stunning powerpoint or google slides presentations. available in different color themes. This article by shon harris, ceo of logical security, explores evolving approaches to information security. it outlines the steps of the vulnerability management lifecycle, starting with defining roles and responsibilities, inventory management, developing metrics, assessing and baselining,.
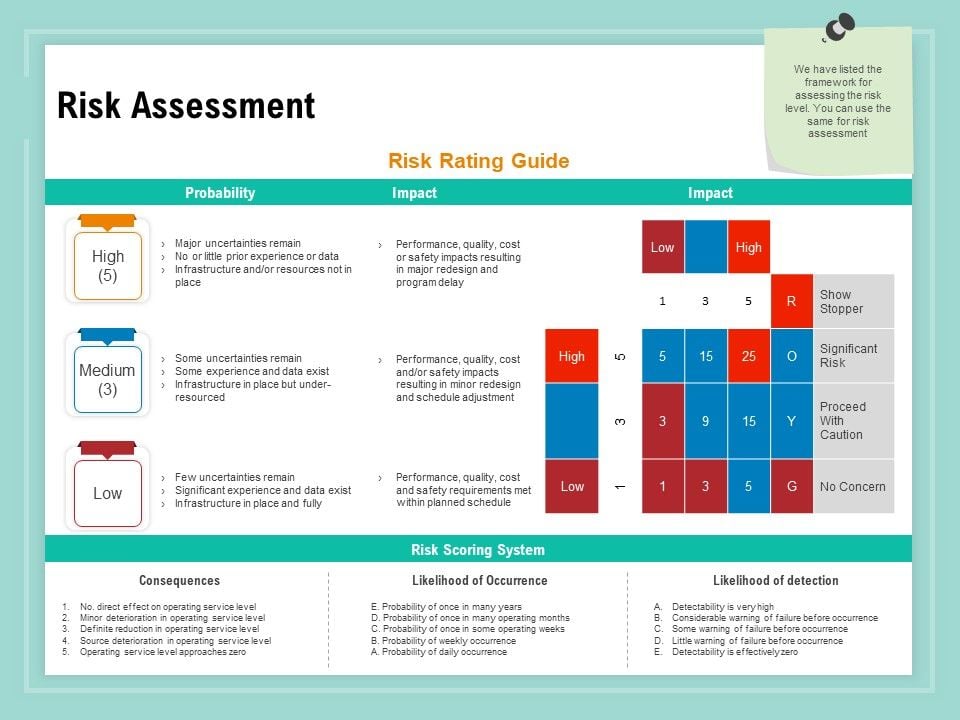
Vulnerability Assessment Methodology Risk Assessment Ppt File Samples Pdf Download this entirely editable template on vulnerability management will let you draft visually stunning powerpoint or google slides presentations. available in different color themes. This article by shon harris, ceo of logical security, explores evolving approaches to information security. it outlines the steps of the vulnerability management lifecycle, starting with defining roles and responsibilities, inventory management, developing metrics, assessing and baselining,. This document outlines an agenda for a summit on campus safety and security. it discusses the importance of conducting risk and vulnerability assessments to identify potential risks and weaknesses. This template features a clear and step by step flow, covering stages such as identifying risks, analyzing vulnerabilities, prioritizing risks, developing mitigation plans, and monitoring and reviewing. A risk assessment presentation template is a pre designed powerpoint layout used to identify, evaluate, and present potential risks in a project, business operation, or process, along with mitigation strategies. By managing our risk, we attempt to reduce the risk by reducing either vulnerability or exposure, since those are two components of risk that we can change; in other words, we cannot control how severe the hazard is, but we can improve how likely we are to get caught in its path or prepare for it.

Vulnerability Assessment Methodology Risk Response Matrix Ppt Diagram This document outlines an agenda for a summit on campus safety and security. it discusses the importance of conducting risk and vulnerability assessments to identify potential risks and weaknesses. This template features a clear and step by step flow, covering stages such as identifying risks, analyzing vulnerabilities, prioritizing risks, developing mitigation plans, and monitoring and reviewing. A risk assessment presentation template is a pre designed powerpoint layout used to identify, evaluate, and present potential risks in a project, business operation, or process, along with mitigation strategies. By managing our risk, we attempt to reduce the risk by reducing either vulnerability or exposure, since those are two components of risk that we can change; in other words, we cannot control how severe the hazard is, but we can improve how likely we are to get caught in its path or prepare for it.

Vulnerability Assessment Methodology Risk Assessment Contd Ppt Show A risk assessment presentation template is a pre designed powerpoint layout used to identify, evaluate, and present potential risks in a project, business operation, or process, along with mitigation strategies. By managing our risk, we attempt to reduce the risk by reducing either vulnerability or exposure, since those are two components of risk that we can change; in other words, we cannot control how severe the hazard is, but we can improve how likely we are to get caught in its path or prepare for it.
Comments are closed.