Vulnerability Assessment Methodology Risk Identification Example Ppt

Vulnerability Assessment Methodology Risk Identification Example Ppt Following slide shows threat identification and vulnerability impact assessment. it covers information of threat agent, affected assets, potential vulnerability, vulnerability ranking, its rank and threats to firm. Vulnerability assessment is the systematic evaluation of an organization's exposure to threats. it involves identifying assets, evaluating threats against those assets, determining vulnerabilities, assessing risks, and selecting appropriate controls.

Vulnerability Assessment Methodology Risk Identification Cost Ppt This slide depicts cybersecurity roadmap for vulnerability assessment illustrating steps such as vulnerability identification, analysis, risk assessment and remediation. The document discusses how to properly document risks in an iso 27001 risk assessment. it provides guidance on matching assets, threats, and vulnerabilities and lists examples of each. Pre designed and available in different themes, this powerpoint and google slides template on vulnerability assessment is incorporated with hd and vector based infographics. Download our ready made powerpoint template to illustrate the steps, components, and impact of vulnerability assessment in a well structured manner.
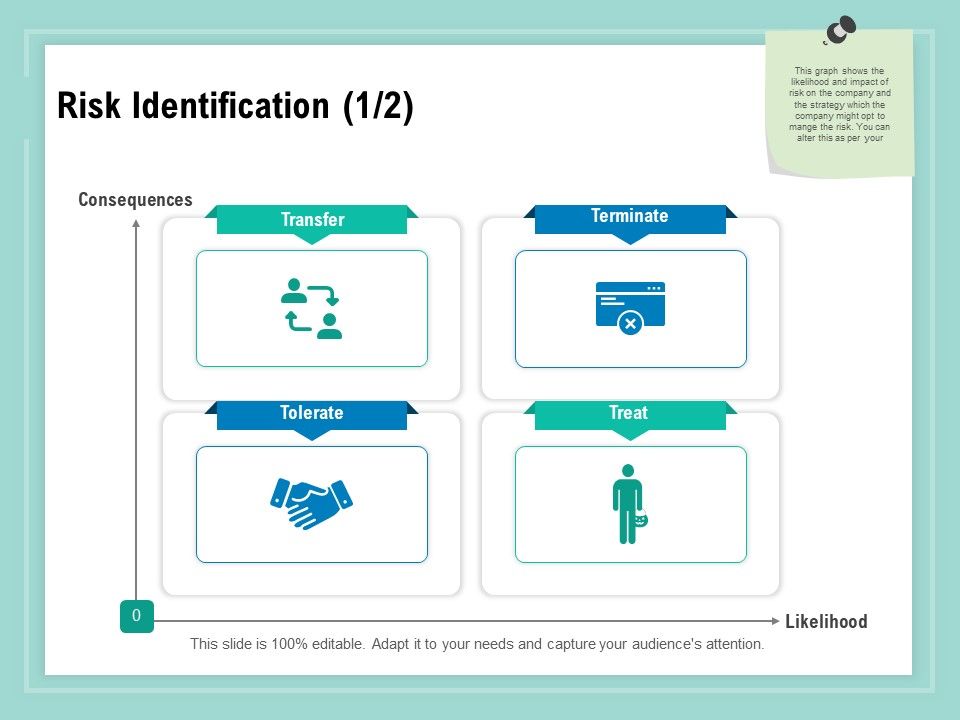
Vulnerability Assessment Methodology Risk Identification Treat Ppt Pre designed and available in different themes, this powerpoint and google slides template on vulnerability assessment is incorporated with hd and vector based infographics. Download our ready made powerpoint template to illustrate the steps, components, and impact of vulnerability assessment in a well structured manner. Dive deep into vulnerability analysis methods, penetration testing, and formal verification in computer security. learn about flaw hypothesis methodology, standards like cve and cwe, and the theory of penetration analysis. Asks a series of questions intended to identify vulnerabilities 5 emergency response planning guide for public drinking water systems. The coastal zone was considered to be made of hard and soft systems. vulnerability was ranked from –3 to 0 and resilience from 0 to 3. What are the vulnerabilities that could lead to compromise? what is the likelihood of compromise? what is the potential impact? what is the most effective use of protection resources? problems with risk assessment. traditional risk assessment: one offs. project not process = limited ongoing benefit. breach response.
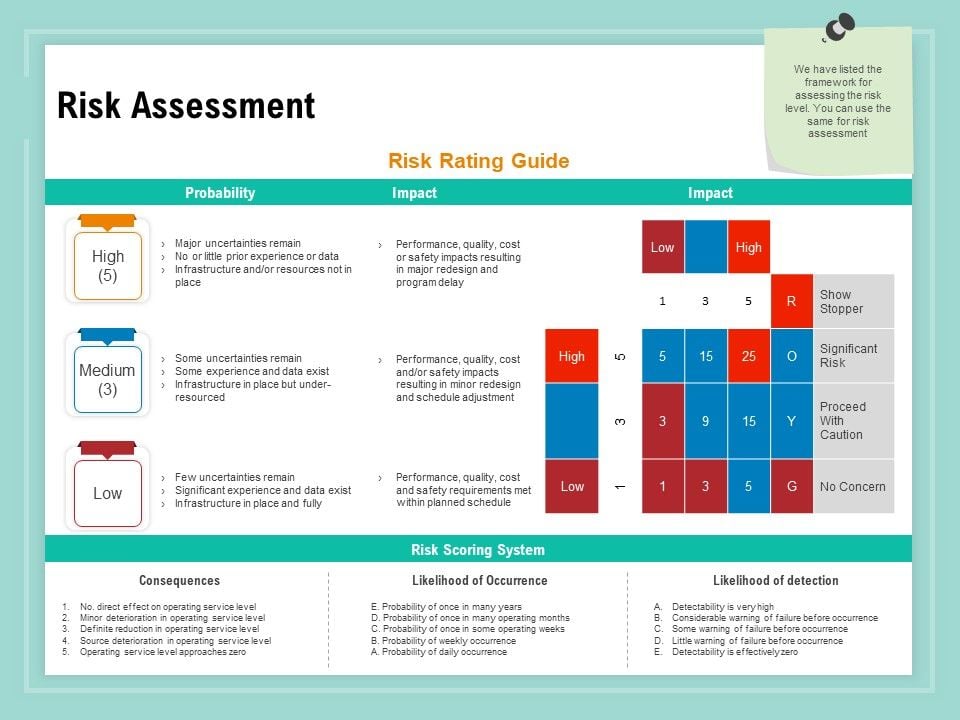
Vulnerability Assessment Methodology Risk Assessment Ppt File Samples Pdf Dive deep into vulnerability analysis methods, penetration testing, and formal verification in computer security. learn about flaw hypothesis methodology, standards like cve and cwe, and the theory of penetration analysis. Asks a series of questions intended to identify vulnerabilities 5 emergency response planning guide for public drinking water systems. The coastal zone was considered to be made of hard and soft systems. vulnerability was ranked from –3 to 0 and resilience from 0 to 3. What are the vulnerabilities that could lead to compromise? what is the likelihood of compromise? what is the potential impact? what is the most effective use of protection resources? problems with risk assessment. traditional risk assessment: one offs. project not process = limited ongoing benefit. breach response.

Vulnerability Assessment Methodology Risk Assessment Contd Ppt Show The coastal zone was considered to be made of hard and soft systems. vulnerability was ranked from –3 to 0 and resilience from 0 to 3. What are the vulnerabilities that could lead to compromise? what is the likelihood of compromise? what is the potential impact? what is the most effective use of protection resources? problems with risk assessment. traditional risk assessment: one offs. project not process = limited ongoing benefit. breach response.

Vulnerability Assessment Methodology Risk Register Ppt Ideas Elements Pdf
Comments are closed.