Vulnerability Assessment Methodology Risk Analysis Complex Ppt Outline

Vulnerability Assessment Methodology Risk Analysis Complex Ppt Outline It also presents valuable insights into the topics including risk assessment, vulnerability assessment, threat assessment, impact assessment. this is a completely customizable powerpoint theme that can be put to use immediately. It involves identifying assets, evaluating threats against those assets, determining vulnerabilities, assessing risks, and selecting appropriate controls. various techniques can be used including asset identification, threat modeling, vulnerability scanning, penetration testing, and risk assessment.

Vulnerability Assessment Methodology Risk Analysis Simplified Format Enhance your understanding of risk assessment and vulnerability analysis with our fully editable powerpoint presentations. tailor the content to fit your needs and effectively communicate critical insights. Download our ready made powerpoint template to illustrate the steps, components, and impact of vulnerability assessment in a well structured manner. Pre designed and available in different themes, this powerpoint and google slides template on vulnerability assessment is incorporated with hd and vector based infographics. Dive deep into vulnerability analysis methods, penetration testing, and formal verification in computer security. learn about flaw hypothesis methodology, standards like cve and cwe, and the theory of penetration analysis.
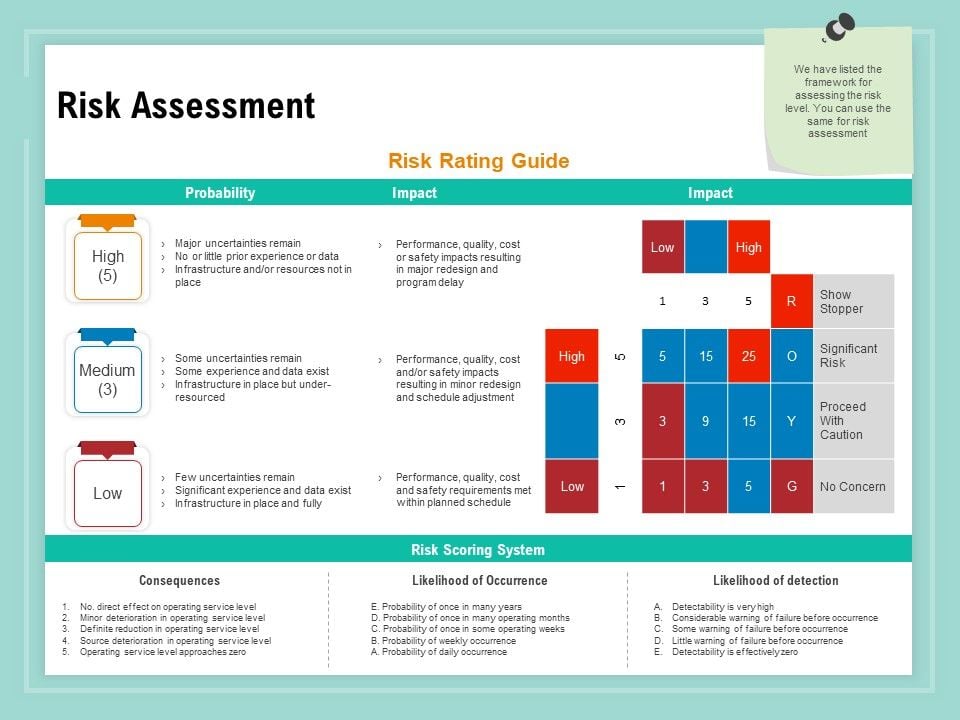
Vulnerability Assessment Methodology Risk Assessment Ppt File Samples Pdf Pre designed and available in different themes, this powerpoint and google slides template on vulnerability assessment is incorporated with hd and vector based infographics. Dive deep into vulnerability analysis methods, penetration testing, and formal verification in computer security. learn about flaw hypothesis methodology, standards like cve and cwe, and the theory of penetration analysis. This document outlines an agenda for a summit on campus safety and security. it discusses the importance of conducting risk and vulnerability assessments to identify potential risks and weaknesses. Whether you’re preparing a risk analysis for a new project, evaluating safety protocols, or outlining mitigation strategies, these templates offer a streamlined way to present complex data. This template features a clear and step by step flow, covering stages such as identifying risks, analyzing vulnerabilities, prioritizing risks, developing mitigation plans, and monitoring and reviewing. At the end of this module, the trainees will be able to: explain vulnerability and risk elements of a threat and how to conduct vulnerability and risk assessment of threats.
Comments are closed.