Vulnerability Assessment Info Savvy Pdf

Vulnerability Assessment Pdf Secure Communication Computer Security The document outlines various types of vulnerability assessments, including active, passive, external, internal, host based, network, application, and wireless network assessments. Pdf | a guide on how to do a vulnerability analysis. every step is shown explained and exemplified with a cambodian case study. | find, read and cite all the research you need on researchgate.
Vulnerability Assessment Info Savvy Pdf In the design of the vulnerability management process, it’s important for assessment and prioritisation, as well as the enrichment of environment specific parameters of detected vulnerabilities, to take place in one process step. This paper describe how vulnerability assessment as a phase in information security framework, how to perform vulnerability assessment, analyzing the result and how deliver the result to the management and give significant impact for the information technology activity and for the business activity in the company. Learn how to conduct a thorough security vulnerability assessment and create a detailed pdf report with this step by step guide. This document provides a guide to conducting risk and vulnerability analyses. it discusses the purpose of such analyses, which is to identify threats, risks, and vulnerabilities in society in order to improve crisis preparedness and safety.

Vulnerability Assessment Methodology Content Ppt Summary Infographics Pdf Learn how to conduct a thorough security vulnerability assessment and create a detailed pdf report with this step by step guide. This document provides a guide to conducting risk and vulnerability analyses. it discusses the purpose of such analyses, which is to identify threats, risks, and vulnerabilities in society in order to improve crisis preparedness and safety. Ain (school of computing and informatics, malaysia) description: vulnerability assessment and risk management are critical components of cybersecurity, focusing on identifying, evaluating, and mitigating. Provides several features for probing computer networks, including host discovery and service and operating system detection; extensible feature set with many scripts that provide more advanced services detection, vulnerability detection and other features. Physical security audits, environmental control checks (hvac, fire suppression), organizational threat assessments, and cyber vulnerability scanners are all key components of a thorough organizational vulnerability assessment. Vulnerability assessment and management (vam) solutions that assess the network, then prioritize the repairs needed and in some cases provide the tools to do the repairs.
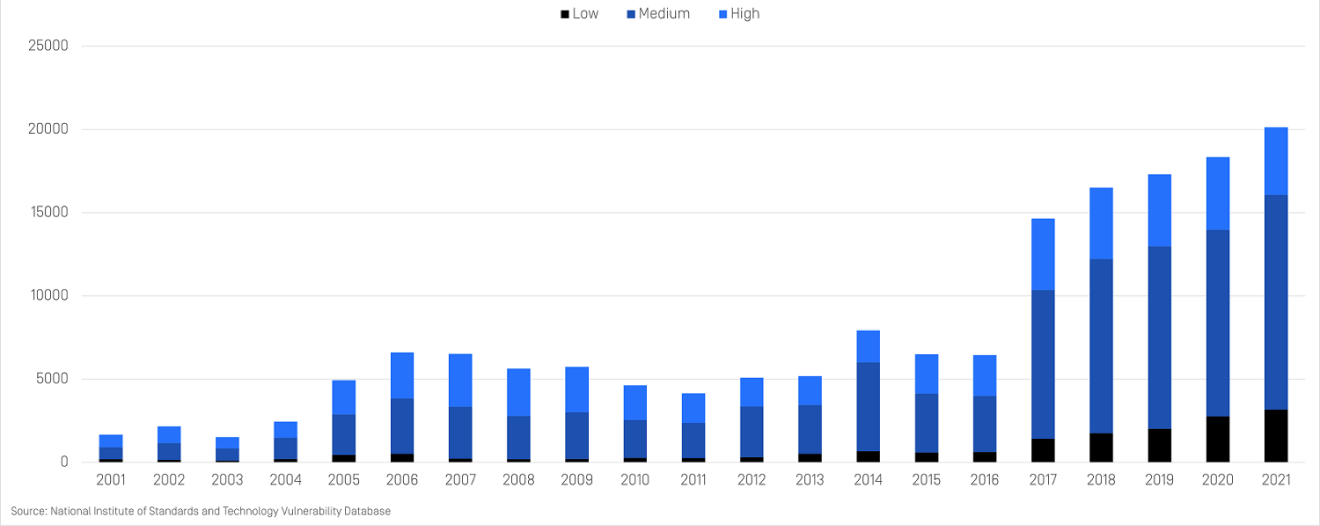
File Based Vulnerability Assessment Technology Opswat Ain (school of computing and informatics, malaysia) description: vulnerability assessment and risk management are critical components of cybersecurity, focusing on identifying, evaluating, and mitigating. Provides several features for probing computer networks, including host discovery and service and operating system detection; extensible feature set with many scripts that provide more advanced services detection, vulnerability detection and other features. Physical security audits, environmental control checks (hvac, fire suppression), organizational threat assessments, and cyber vulnerability scanners are all key components of a thorough organizational vulnerability assessment. Vulnerability assessment and management (vam) solutions that assess the network, then prioritize the repairs needed and in some cases provide the tools to do the repairs.
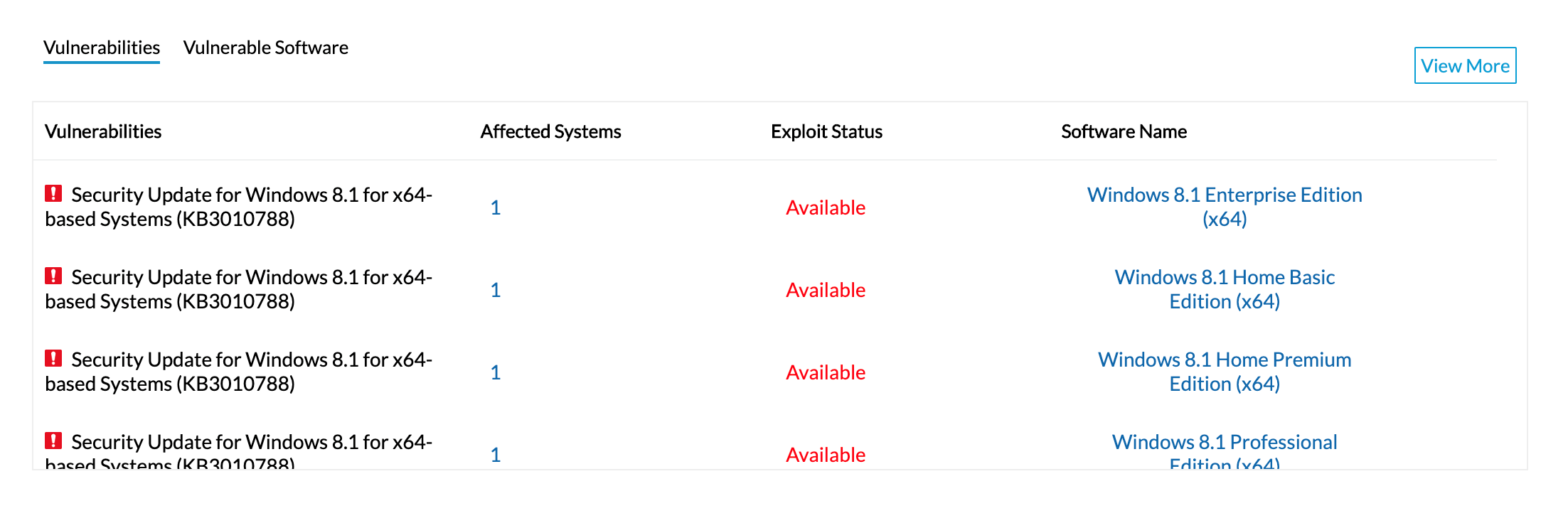
Vulnerability Assessment Tool Vulnerability Analysis Checklist Physical security audits, environmental control checks (hvac, fire suppression), organizational threat assessments, and cyber vulnerability scanners are all key components of a thorough organizational vulnerability assessment. Vulnerability assessment and management (vam) solutions that assess the network, then prioritize the repairs needed and in some cases provide the tools to do the repairs.
Comments are closed.