Vulnerability Assessment Guide Pdf

Vulnerability Assessment Pdf Secure Communication Computer Security Pdf | a guide on how to do a vulnerability analysis. every step is shown explained and exemplified with a cambodian case study. | find, read and cite all the research you need on researchgate. This template has been developed by the national cybersecurity authority (nca) as an illustrative example that can be used by organizations as a reference and guide.
What Is A Vulnerability Assessment A Complete Guide For 2023 They have created a climate risk and vulnerability assessment toolkit that outlines a variety of resources to guide a vulnerability assessment. this document provides guidance on the interpretation and utilization of exposure and sensitivity data. Vulnerability assessment: typically is general in scope and includes a large assessment. predictable. unreliable at times and high rate of false positives. vulnerability assessment invites debate among system admins. produces a report with mitigation guidelines and action items. A proxy for vulnerability levels in economic s strengthening projects, poverty measurements are backwards looking and static, while vulnerability measurements assess risk, and are therefore forward looking and dynamic. While you, as an individual or an organization, may not know all answers to the questions outlined in the owasp vulnerability management guide (ovmg or the guide), it should not prohibit your business from becoming more resilient through vulnerability management program adoption.
Understanding Vulnerability Assessment Pdf A proxy for vulnerability levels in economic s strengthening projects, poverty measurements are backwards looking and static, while vulnerability measurements assess risk, and are therefore forward looking and dynamic. While you, as an individual or an organization, may not know all answers to the questions outlined in the owasp vulnerability management guide (ovmg or the guide), it should not prohibit your business from becoming more resilient through vulnerability management program adoption. Vulnerability assessment guide free download as pdf file (.pdf), text file (.txt) or read online for free. tenable vulnerability assessment guide. Physical security audits, environmental control checks (hvac, fire suppression), organizational threat assessments, and cyber vulnerability scanners are all key components of a thorough organizational vulnerability assessment. Abstract and figures the study was carried out based on several discussions and interactions with the ctae team on the idea of “participatory vulnerability risk assessment” manual. This resource guide was developed to help locate resources to help you gain a working knowledge of the vulnerability management process as well as identify best practices for incorporating them into your own program.
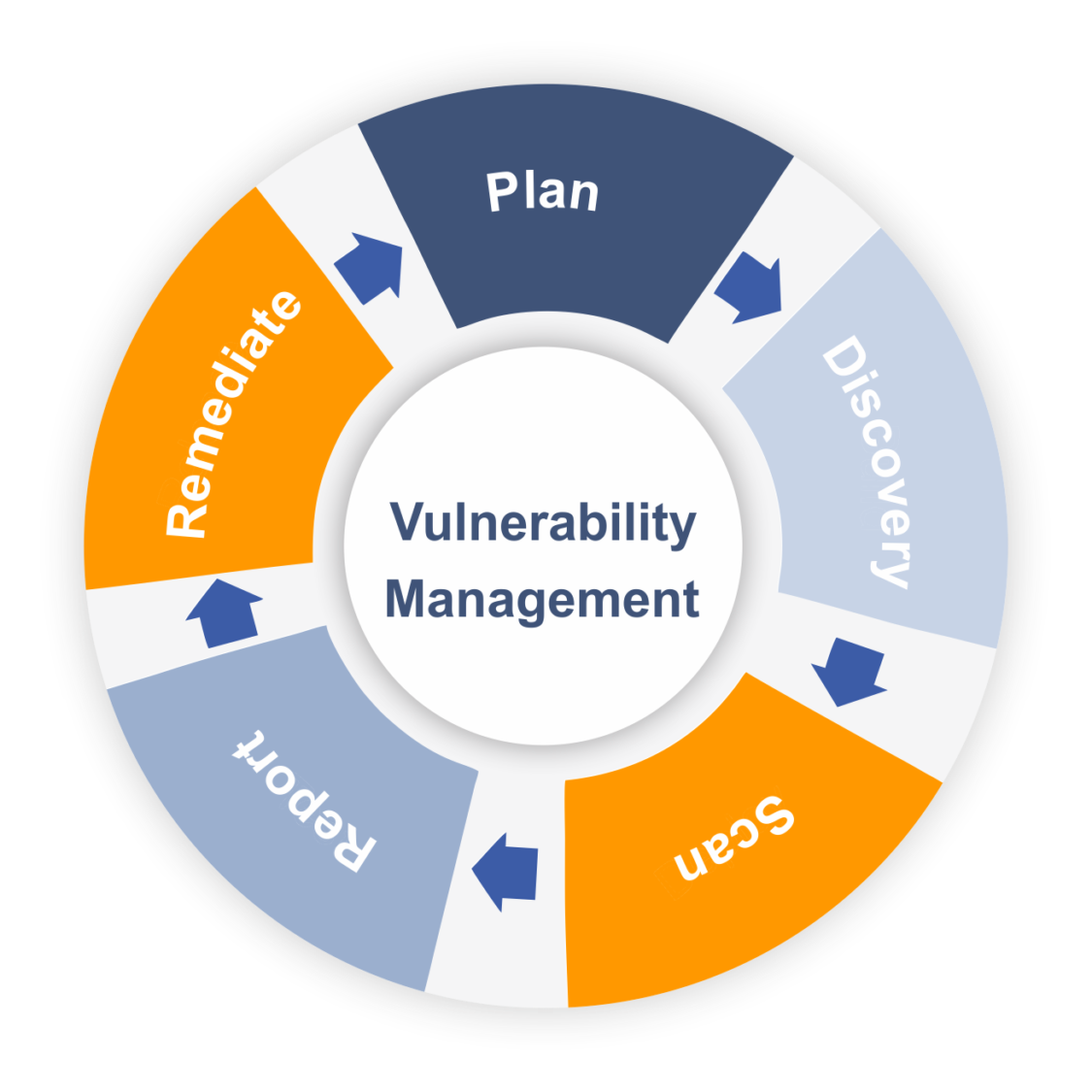
Vulnerability Assessment Scanning Tools List 2018 Esecforte Vulnerability assessment guide free download as pdf file (.pdf), text file (.txt) or read online for free. tenable vulnerability assessment guide. Physical security audits, environmental control checks (hvac, fire suppression), organizational threat assessments, and cyber vulnerability scanners are all key components of a thorough organizational vulnerability assessment. Abstract and figures the study was carried out based on several discussions and interactions with the ctae team on the idea of “participatory vulnerability risk assessment” manual. This resource guide was developed to help locate resources to help you gain a working knowledge of the vulnerability management process as well as identify best practices for incorporating them into your own program.
Comments are closed.