Vulnerability Assessment Gb Tech
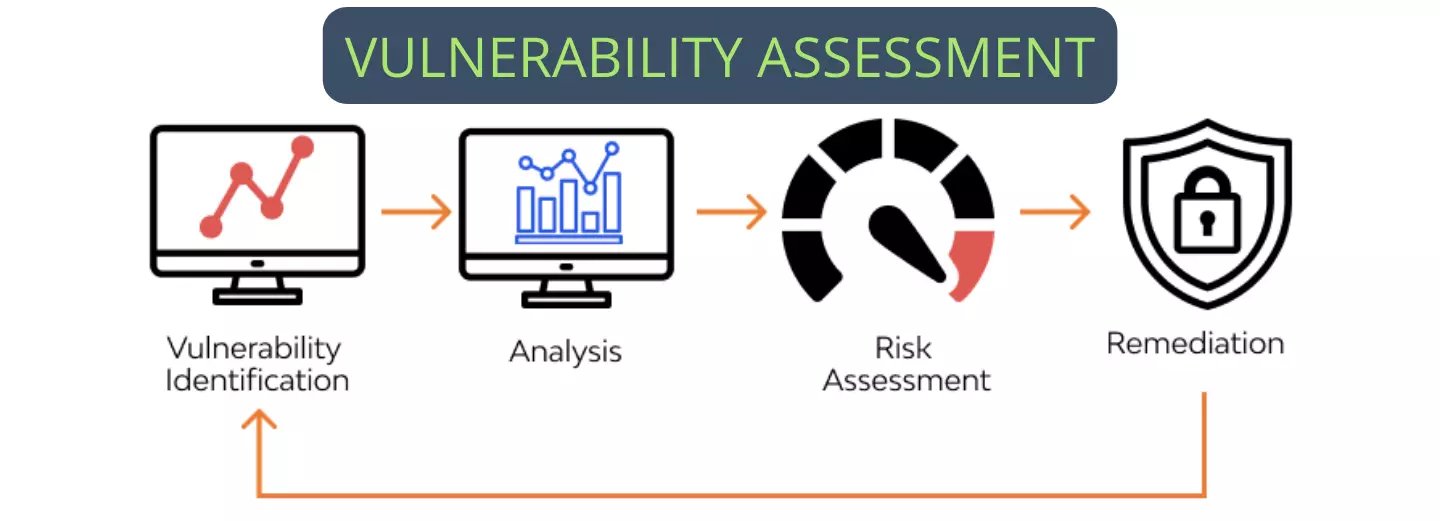
Vulnerability Assessment Arc Tech Cyber Security Data Privacy Vulnerability assessments provide your it team with critical insight into the it infrastructure and network. it allows your it team to properly manage and patch vulnerabilities that pose a risk to your network and protect your organization from threat actors and possible breaches. Understand the importance of regular vulnerability assessments and penetration tests and why both approaches are essential for risk management.
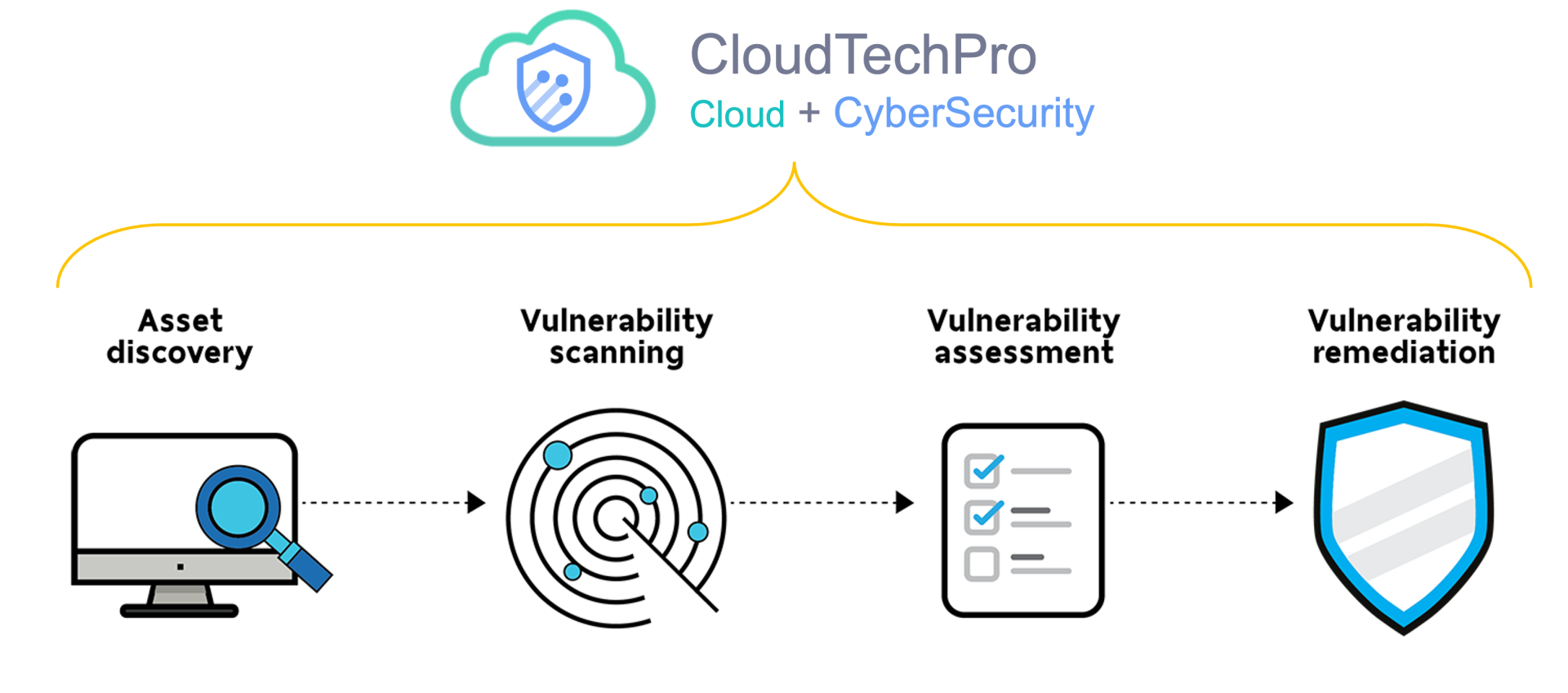
Vulnerability Assessment Cloudtechpro All types of it risk assessments will identify, prioritize and measure your cybersecurity risk, but specific industry, business strategy and regulatory requirements will determine which type of risk assessment methodology you require. Discover how vulnerability scans can safeguard your organization by identifying and mitigating cyber threats before they impact your operations. You must use penetration tests and vulnerability assessments on your service to make sure it’s secure. vulnerability assessments help you find potential weaknesses in your service. Vulnerability assessments are an important part of the vulnerability management and it risk management life cycles since they safeguard systems and data against unauthorized access and data breaches.

Vulnerability Assessment Briska Tech Cyber Security Quality Assurance You must use penetration tests and vulnerability assessments on your service to make sure it’s secure. vulnerability assessments help you find potential weaknesses in your service. Vulnerability assessments are an important part of the vulnerability management and it risk management life cycles since they safeguard systems and data against unauthorized access and data breaches. Gb defense solutions conducts comprehensive threat and security assessments to help organizations, schools, and other industries develop, implement, and maintain effective security and safety programs that protect their most important assets – their people. Basic cyber risk assessment, analysis, and management method. this section is for readers who are new to cyber security risk management, or want guidance on a basic step by step approach to risk. Learn about the top 10 vulnerability assessment best practices, essential strategies, and proven methods. discover how to minimize risks, improve compliance, and protect your data from new risks now!. Our comprehensive risk assessment reveals your company’s true vulnerabilities and compliance, which is the first step towards implementing a remediation plan and compliance strategy.
Vulnerability Assessment Gb Tech Gb defense solutions conducts comprehensive threat and security assessments to help organizations, schools, and other industries develop, implement, and maintain effective security and safety programs that protect their most important assets – their people. Basic cyber risk assessment, analysis, and management method. this section is for readers who are new to cyber security risk management, or want guidance on a basic step by step approach to risk. Learn about the top 10 vulnerability assessment best practices, essential strategies, and proven methods. discover how to minimize risks, improve compliance, and protect your data from new risks now!. Our comprehensive risk assessment reveals your company’s true vulnerabilities and compliance, which is the first step towards implementing a remediation plan and compliance strategy.
Comments are closed.