Vulnerabilities Management Pdf Vulnerability Computing Computer

Computer Vulnerabilities Pdf Vulnerability Computing Computer The ultimate destination for modern light photos. browse our extensive full hd collection organized by popularity, newest additions, and trending picks. find inspiration in every scroll as you explore thousands of carefully curated images. download instantly and enjoy beautiful visuals on all your devices. Exceptional gradient pictures crafted for maximum impact. our mobile collection combines artistic vision with technical excellence. every pixel is optimized to deliver a amazing viewing experience. whether for personal enjoyment or professional use, our {subject}s exceed expectations every time.

Vulnerability Management Pdf Vulnerability Computing Security Elevate your digital space with gradient photos that inspire. our high resolution library is constantly growing with fresh, creative content. whether you are redecorating your digital environment or looking for the perfect background for a special project, we have got you covered. each download is virus free and safe for all devices. Captivating gorgeous space pictures that tell a visual story. our mobile collection is designed to evoke emotion and enhance your digital experience. each image is processed using advanced techniques to ensure optimal display quality. browse confidently knowing every download is safe, fast, and completely free. Elevate your digital space with gradient arts that inspire. our full hd library is constantly growing with fresh, ultra hd content. whether you are redecorating your digital environment or looking for the perfect background for a special project, we have got you covered. each download is virus free and safe for all devices. Premium collection of beautiful minimal designs. optimized for all devices in stunning full hd. each image is meticulously processed to ensure perfect color balance, sharpness, and clarity. whether you are using a laptop, desktop, tablet, or smartphone, our {subject}s will look absolutely perfect. no registration required for free downloads.

Vulnerability Management System Avoiding The Threat Of Cyberattacks Exceptional sunset pictures crafted for maximum impact. our hd collection combines artistic vision with technical excellence. every pixel is optimized to deliver a modern viewing experience. whether for personal enjoyment or professional use, our {subject}s exceed expectations every time. Breathtaking space wallpapers that redefine visual excellence. our full hd gallery showcases the work of talented creators who understand the power of high quality imagery. transform your screen into a work of art with just a few clicks. all images are optimized for modern displays and retina screens. Curated premium sunset wallpapers perfect for any project. professional 8k resolution meets artistic excellence. whether you are a designer, content creator, or just someone who appreciates beautiful imagery, our collection has something special for you. every image is royalty free and ready for immediate use. Your search for the perfect mountain background ends here. our hd gallery offers an unmatched selection of gorgeous designs suitable for every context. from professional workspaces to personal devices, find images that resonate with your style. easy downloads, no registration needed, completely free access.

What Is Vulnerability Management Vulnerability Assessment Tool Curated premium sunset wallpapers perfect for any project. professional 8k resolution meets artistic excellence. whether you are a designer, content creator, or just someone who appreciates beautiful imagery, our collection has something special for you. every image is royalty free and ready for immediate use. Your search for the perfect mountain background ends here. our hd gallery offers an unmatched selection of gorgeous designs suitable for every context. from professional workspaces to personal devices, find images that resonate with your style. easy downloads, no registration needed, completely free access.

Vulnerabilities Management Pdf Vulnerability Computing Computer

Vulnerability Management Procedure Pdf Vulnerability Computing

What Is Vulnerability Management Pdf Vulnerability Computing

Policies Around Vulnerability And Patch Management Pdf

Vulnerability Management Processes And Tools
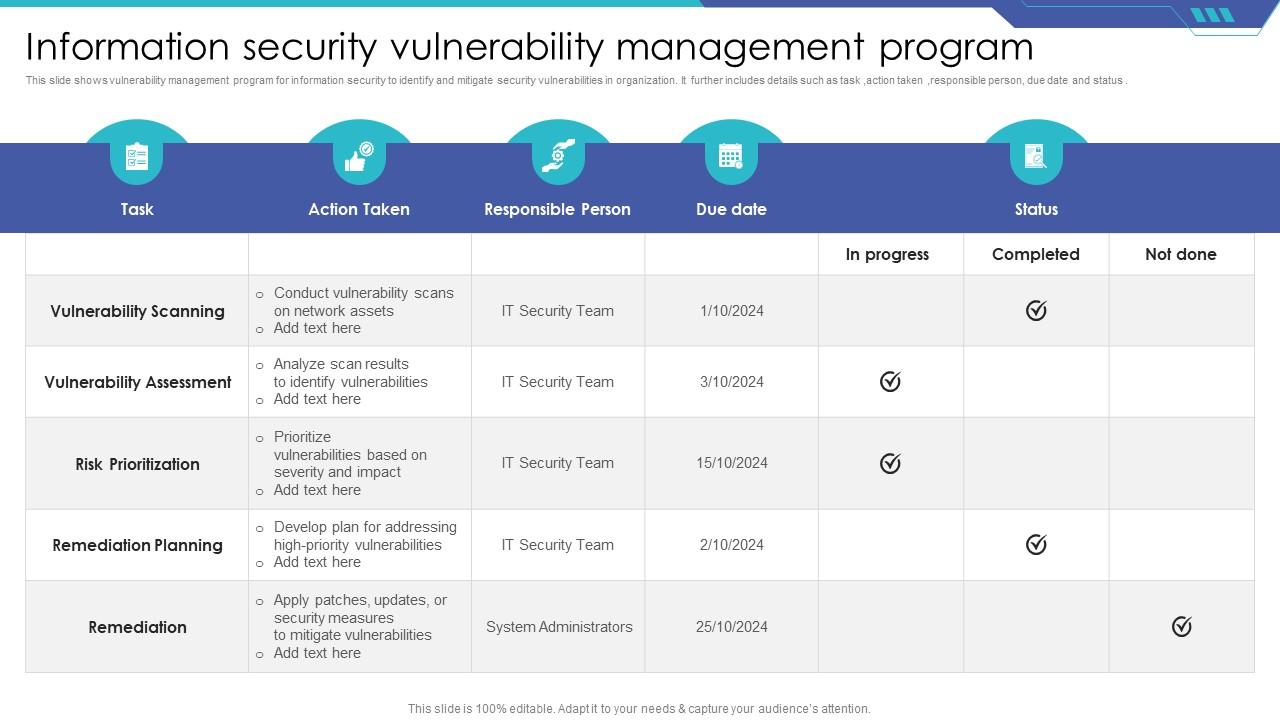
Information Security Vulnerability Management Program Ppt Sample

Vulnerability Management Policy Pdf Vulnerability Computing Malware

Vulnerability Management Training Pdf Vulnerability Computing

Class 2 Vulnerability Management Pdf Vulnerability Computing

Wartsila Ics Vulnerability Management Leaflet Pdf Vulnerability

What Is Vulnerability Management Cyber Security Element Four

Vulnerability Management Pdf Penetration Test Vulnerability

Vulnerability Management 2 Pdf Vulnerability Computing Security

Guide To Vulnerability Management 1668341881 Pdf Security

Vulnerability Scanning Pdf Port Computer Networking

Vulnerability Management Pdf Vulnerability Computing Security

Vulnerability Management Pdf Vulnerability Computing Computer

3vulnerability Management Dict Pdf Vulnerability Computing Security

Vulnerability Management Policy Template For Control 7 Pdf
Vulnerability Management Guide Ciso2ciso Com Cyber Security Group

Vulnerability Management Program Pdf Vulnerability Computing

Vulnerability Management Overview Pdf Vulnerability Computing

Vulnerability Management Cyber Security Pdf Vulnerability

What Is Vulnerability Management Pdf Vulnerability Computing

A Guide To Threat Centric Vulnerability Management 202x Cyberproof

Vulnerability Management Program Pdf Security Computer Security

Vulnerability Management Process Pdf Vulnerability Computing

Vulnerability Management Datasheet Pdf Vulnerability Computing

Vulnerabilities Pdf Exploit Computer Security Superuser
Vulnerability Management Pdf

Pdf Download Vulnerability Management Beginners Guide To
Comments are closed.