Vulnerabilities Dashboard Research About Vulnerabilities Dashboard

Security Vulnerabilities Dashboard By Mufidul On Dribbble In the vulnerabilities dashboard in the analytics module, users can access informative charts that provide insights into the security vulnerabilities detected within their data. In this short paper, we report on the early results of developing an interactive vulnerability dashboard that enables security analysts to prioritize vulnerabilities based on their age, persistence, and impact on the system.

Security Vulnerabilities Dashboard Dashboard Design Vulnerability In this paper, we report our work in progress of developing a vulnerability management dashboard that helps analysts to overcome these challenges. the approach uses interviews to identify a. The vulnerability overview dashboard (vulnerabilitiesvulnerability overview) lets you customize how information about vulnerabilities and vulnerability instances is presented so you can view their impact on your devices from different perspectives. In this paper, we report our work in progress of developing a vulnerability management dashboard that helps analysts overcome these challenges. the approach uses interviews to identify a typical security analyst workflow and proceeds with an iterative design that relies on real world data. This is a really simple way to draw out the potentially high impact and highly exploitable vulnerabilities in your network, especially when used in conjunction with the other filters available in the dashboard.
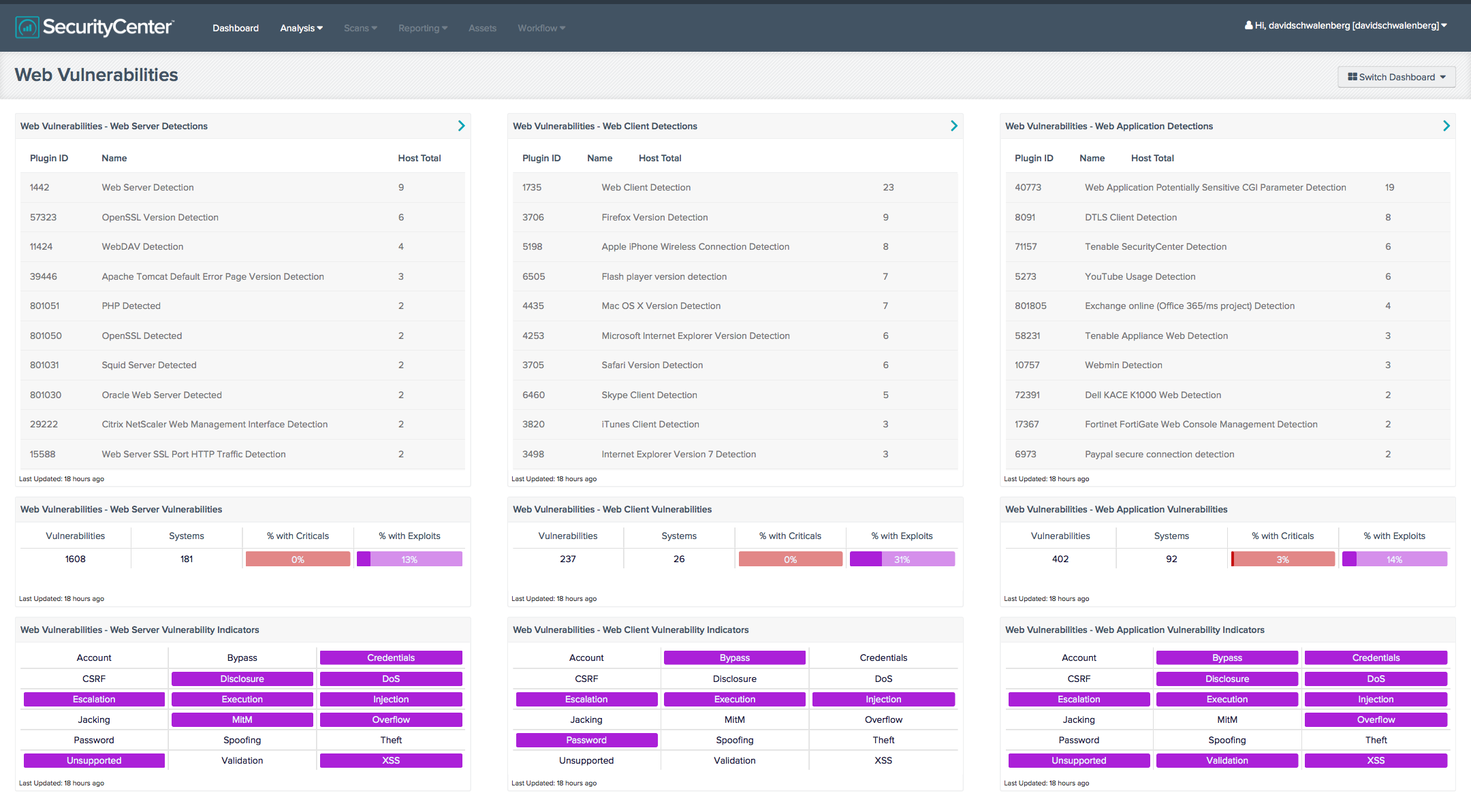
Web Vulnerabilities Dashboard Sc Dashboard Tenable In this paper, we report our work in progress of developing a vulnerability management dashboard that helps analysts overcome these challenges. the approach uses interviews to identify a typical security analyst workflow and proceeds with an iterative design that relies on real world data. This is a really simple way to draw out the potentially high impact and highly exploitable vulnerabilities in your network, especially when used in conjunction with the other filters available in the dashboard. These dashboards provide real time monitoring and alerting, enabling organizations to quickly detect vulnerabilities and expedite the vulnerability management remediation process. A vulnerability management dashboard helps teams organize their vulnerability data. read our suggestions for insightful and actionable dashboards. Cve threat dashboard common vulnerabilities and exposures database cve database dashboard – real time tracking of cybersecurity threats. monitor the latest common vulnerabilities and exposures (cves), analyze trends, and stay informed with real time security intelligence, updated every 30 minutes. Use this dashboard to gain insights into the effectiveness of your current vulnerability management efforts, learn about new vulnerabilities and emerging threats, help prioritize your remediation plans, and focus on specific areas in your environment.

Vulnerability Overview Dashboard These dashboards provide real time monitoring and alerting, enabling organizations to quickly detect vulnerabilities and expedite the vulnerability management remediation process. A vulnerability management dashboard helps teams organize their vulnerability data. read our suggestions for insightful and actionable dashboards. Cve threat dashboard common vulnerabilities and exposures database cve database dashboard – real time tracking of cybersecurity threats. monitor the latest common vulnerabilities and exposures (cves), analyze trends, and stay informed with real time security intelligence, updated every 30 minutes. Use this dashboard to gain insights into the effectiveness of your current vulnerability management efforts, learn about new vulnerabilities and emerging threats, help prioritize your remediation plans, and focus on specific areas in your environment.
Comments are closed.