Vmware Cybersecurity Precryption Encryption Vmwareexplore Gigamon
Gigamon Hybrid Cloud Visibility Cybersecurity Solutions Carahsoft The vsphere virtual machine encryption process encrypts data on the host before writing the data to storage. the effectiveness of back end storage features such as deduplication, compression, replication, and so on, might be affected when encrypting virtual machines in this manner. Learn best practices for vm encryption in vmware, covering key management, performance impacts, and secure backup strategies to protect sensitive data.

Vmware Cybersecurity Precryption Encryption Vmwareexplore Gigamon This objective is a key component of the 2v0 16.25 exam, testing your ability to implement encryption features like vm encryption and vsan encryption in real world scenarios. These guides provide prescriptive guidance for customers on how to deploy and operate vmware products in a secure manner. find them at vmware security hardening guides . When you create a new windows 11×64 vm, the new vm wizard (fig 2) asks you to set an encryption password or auto generated one. this enables the vm to support windows 11 requirements for tpm secure boot. Vmware vm encryption provides protection directly at the hypervisor level, which means encryption is handled independently of the guest operating system. whether the guest os is compromised or not, your data stays secure.

Gigamon On Linkedin Vmware Deepobservability Vmwareexplore When you create a new windows 11×64 vm, the new vm wizard (fig 2) asks you to set an encryption password or auto generated one. this enables the vm to support windows 11 requirements for tpm secure boot. Vmware vm encryption provides protection directly at the hypervisor level, which means encryption is handled independently of the guest operating system. whether the guest os is compromised or not, your data stays secure. Gigamon precryption® technology delivers plaintext visibility into lateral, east west encrypted cloud traffic to the full security stack. no decryption required. Below are several key strategies for protecting esxi hosts and virtual machines (vms) from ransomware attacks: 1. keep vmware esxi updated. regularly apply security patches and firmware updates. When creating an encrypted vm, vmware workstation gives you the option to remember the password. it does this by storing the password in the windows credential manager. vmware does not provide a way to retrieve this stored password, but it can be accessed via the win32 credreadw api function. This article explores in depth the strategies, best practices, and technical approaches to protect your vmware vms through encryption, with a focus on how access control can reinforce security.
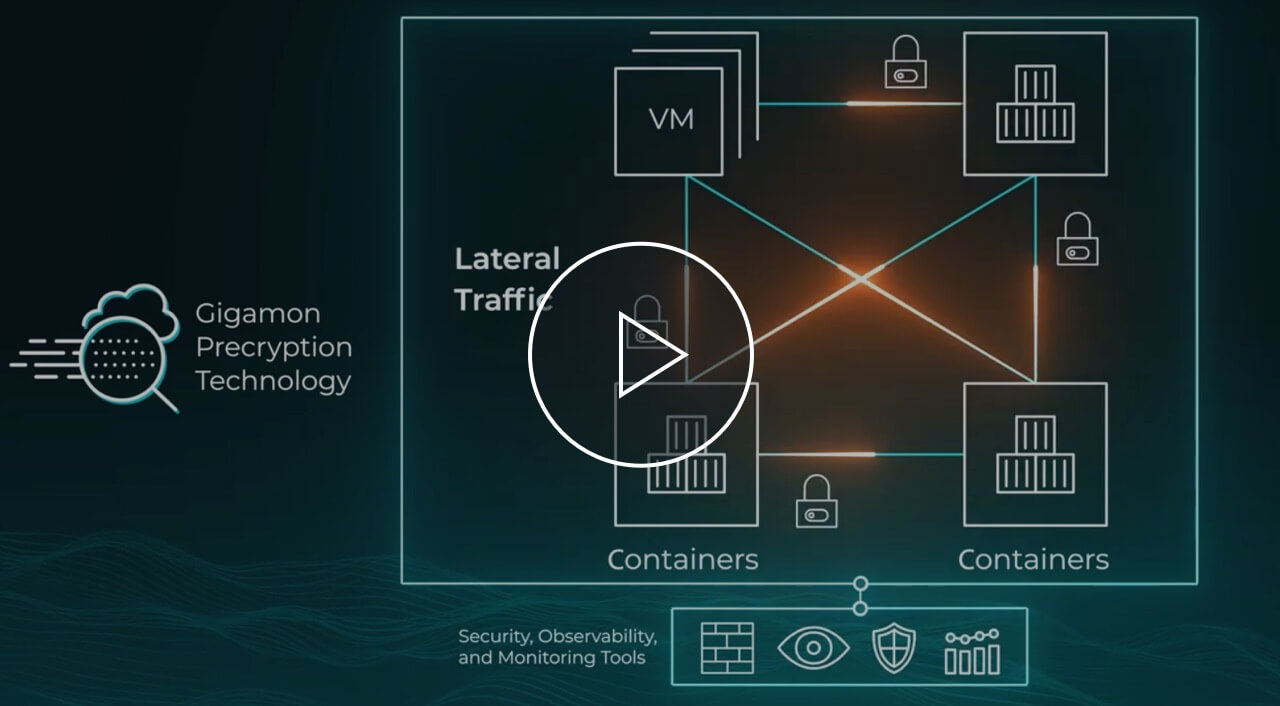
Precryption Technology Gigamon Gigamon precryption® technology delivers plaintext visibility into lateral, east west encrypted cloud traffic to the full security stack. no decryption required. Below are several key strategies for protecting esxi hosts and virtual machines (vms) from ransomware attacks: 1. keep vmware esxi updated. regularly apply security patches and firmware updates. When creating an encrypted vm, vmware workstation gives you the option to remember the password. it does this by storing the password in the windows credential manager. vmware does not provide a way to retrieve this stored password, but it can be accessed via the win32 credreadw api function. This article explores in depth the strategies, best practices, and technical approaches to protect your vmware vms through encryption, with a focus on how access control can reinforce security.

Vmware Memory Encryption Linux Level1techs Forums When creating an encrypted vm, vmware workstation gives you the option to remember the password. it does this by storing the password in the windows credential manager. vmware does not provide a way to retrieve this stored password, but it can be accessed via the win32 credreadw api function. This article explores in depth the strategies, best practices, and technical approaches to protect your vmware vms through encryption, with a focus on how access control can reinforce security.

Gigamon On Linkedin Precryption Cybersecurity Encryption
Comments are closed.