Virus Trick Even Fools Computer Experts Explained Safely

Virus Trick Even Fools Computer Experts Explained Safely It basically tricks the program into running malicious code, even if you never run the malicious file yourself. in this video talk about this "dll hijacking" or "dll sideloading" technique and. Hackers slip in malicious helper files that look harmless, letting the app run normally while silently installing malware in the background. even signed, virus free programs can secretly hack.

Funny Computer Trick Anonpiper But instead of unlocking anything, these videos trick people into running hidden malware on their devices. once that happens, attackers can steal passwords, cryptocurrency wallet details, or access to social media and bank accounts. Here’s everything you need to know about this new verification attack along with some tips and tricks to help you avoid malicious sites spreading malware and other viruses. Imagine the scammers are skilled enough to craft a really stubborn computer virus. if your device gets infected, your antivirus solution might not be able to get rid of it. Protect your computer from viruses with these cybersecurity rules! learn how to keep your data safe and secure with our tips and tricks.
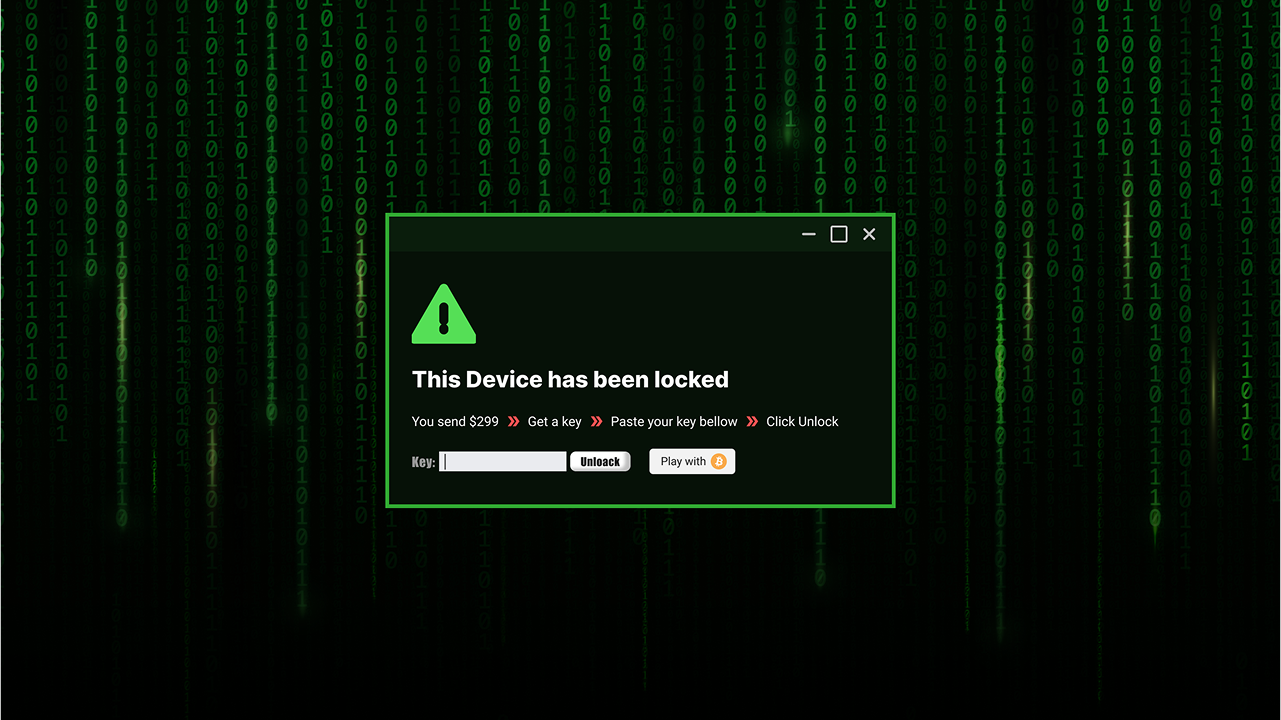
Computer Virus Prank Fake System Crash Virus Alert Imagine the scammers are skilled enough to craft a really stubborn computer virus. if your device gets infected, your antivirus solution might not be able to get rid of it. Protect your computer from viruses with these cybersecurity rules! learn how to keep your data safe and secure with our tips and tricks. Explore how trojan horse malware functions, how it tricks users, infects systems, and carries out hidden attacks. learn what every enthusiast should know about its deceptive power. Even signed, virus free programs can secretly hack your computer through a tactic called dll hijacking. This trick is increasingly used in malware campaigns, highlighting the importance of enabling file extensions and exercising caution with suspicious files. It demonstrates real examples of *dll* manipulation and its risks, emphasizing how *reverse engineering* can expose these **security vulnera more. audio tracks for some languages were.

How To Prevent The April Fools Day Virus Cousinyou14 Explore how trojan horse malware functions, how it tricks users, infects systems, and carries out hidden attacks. learn what every enthusiast should know about its deceptive power. Even signed, virus free programs can secretly hack your computer through a tactic called dll hijacking. This trick is increasingly used in malware campaigns, highlighting the importance of enabling file extensions and exercising caution with suspicious files. It demonstrates real examples of *dll* manipulation and its risks, emphasizing how *reverse engineering* can expose these **security vulnera more. audio tracks for some languages were.
Comments are closed.