Virtual Network Visibility Keysight
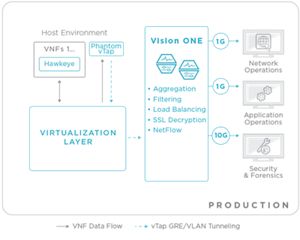
Virtual Network Visibility Keysight Virtual network visibility solutions optimize performance, enhance security, and simplify monitoring. unlock the full potential of your network—explore keysight today!. Delivering dynamic network intelligence relies on network visibility, and keysight provides a complete suite of products. keysight vision network packet brokers (npbs) are at the core.

Virtual Network Visibility Keysight The following keysight packet brokers support ml ai sensors directly inside with robust compute mem storage making it easy to deploy and manage one system instead of multiple appliances. Complete visibility into cyberthreats – the keysight network visibility architecture delivers to the vectra cognito platform all required traffic from anywhere in the network or cloud; 100% of traffic can be monitored, inspected and analyzed. Keysight’s visibility solutions deliver real time, end to end visibility, insight, and security across physical, virtual, sdn, and nfv networks. by ensuring seamless control, coverage, and performance, these solutions protect and optimise critical networking, data centre, and cloud assets. This book provides a collection of the top 68 network visibility use cases, along with a brief overview of how to implement each one. these summaries allow you to determine which use cases are critical for your business.
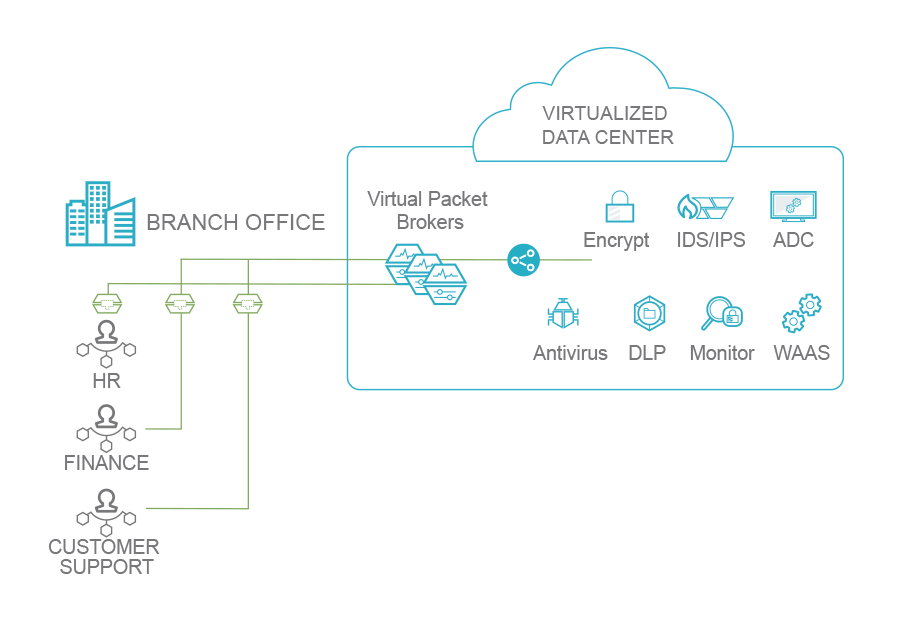
Virtual Network Visibility Keysight Keysight’s visibility solutions deliver real time, end to end visibility, insight, and security across physical, virtual, sdn, and nfv networks. by ensuring seamless control, coverage, and performance, these solutions protect and optimise critical networking, data centre, and cloud assets. This book provides a collection of the top 68 network visibility use cases, along with a brief overview of how to implement each one. these summaries allow you to determine which use cases are critical for your business. That’s why network visibility solutions like keysight’s are critical for seamless deployment across hybrid infrastructures, with complete physical, virtual and cloud visibility even into most encrypted traffic. Keysight provides intelligent visibility across hybrid networks to optimize threat hunting, incident response, forensics, trou bleshooting, and resilience. visibility proves vital to delivering a secure, high quality user experience. Keysight cloudlens, the public, private, and hybrid cloud visibility platform, enables packet capture, filtering, and analysis to provide dynamic network intelligence in any cloud environment. The ai powered network visibility solution enhances existing security infrastructures by filtering out noise and focusing on high priority threats, allowing enterprises to optimize their security posture without overwhelming their teams with excessive data.

Keysight Network Visibility Tempest Telecom Solutions That’s why network visibility solutions like keysight’s are critical for seamless deployment across hybrid infrastructures, with complete physical, virtual and cloud visibility even into most encrypted traffic. Keysight provides intelligent visibility across hybrid networks to optimize threat hunting, incident response, forensics, trou bleshooting, and resilience. visibility proves vital to delivering a secure, high quality user experience. Keysight cloudlens, the public, private, and hybrid cloud visibility platform, enables packet capture, filtering, and analysis to provide dynamic network intelligence in any cloud environment. The ai powered network visibility solution enhances existing security infrastructures by filtering out noise and focusing on high priority threats, allowing enterprises to optimize their security posture without overwhelming their teams with excessive data.

Keysight Network Visibility Tempest Telecom Solutions Keysight cloudlens, the public, private, and hybrid cloud visibility platform, enables packet capture, filtering, and analysis to provide dynamic network intelligence in any cloud environment. The ai powered network visibility solution enhances existing security infrastructures by filtering out noise and focusing on high priority threats, allowing enterprises to optimize their security posture without overwhelming their teams with excessive data.
Comments are closed.