Virtual Machine Forensics Pptx
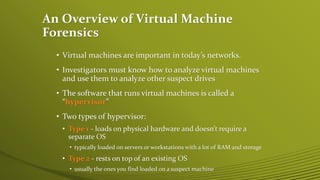
Virtual Machine Forensics Pptx Investigators must image both host systems and vms, checking for vm files, network adapters and usb attachments to uncover any virtual machines. live acquisitions of running vms are also important to capture snapshot data. download as a pptx, pdf or view online for free. Learn the standard procedures for analyzing, acquiring, and investigating virtual machines. understand network intrusions and unauthorized access scenarios, along with network forensics tools.
Virtual Machine Forensics Pptx Week11 mod9 free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. View gcfi6e ppt ch10.pptx from cybersecur 1 at cdi college of business, technology and health care. guide to computer forensics and investigations sixth edition chapter 10 virtual machine forensics,. Digital forensic examiners must analyze virtual machines (vms) to investigate cybercrimes, which are software running on a hypervisor, either a type 1 or type 2 hypervisor. Virtual machine forensics, live acquisitions, and network forensics.

Virtual Machine Forensics Pptx Digital forensic examiners must analyze virtual machines (vms) to investigate cybercrimes, which are software running on a hypervisor, either a type 1 or type 2 hypervisor. Virtual machine forensics, live acquisitions, and network forensics. Hardikadesara1 digital forensics of compromise virtual machine using autopsy public. Guide to computer forensics and investigations fourth edition chapter 11 virtual machines, network forensics, and live acquisitions virtual machines overview virtual. Investigators must know how to detect a virtual machine installed on a host, acquire an image of a virtual machine, and use virtual machines to examine malware. The purpose of my virtual digital forensics lab is to provide a realistic and isolated environment for practicing and learning various digital forensics skills and techniques, such as data.

Virtual Machine Forensics Pptx Hardikadesara1 digital forensics of compromise virtual machine using autopsy public. Guide to computer forensics and investigations fourth edition chapter 11 virtual machines, network forensics, and live acquisitions virtual machines overview virtual. Investigators must know how to detect a virtual machine installed on a host, acquire an image of a virtual machine, and use virtual machines to examine malware. The purpose of my virtual digital forensics lab is to provide a realistic and isolated environment for practicing and learning various digital forensics skills and techniques, such as data.

Virtual Machine Forensics Pptx Investigators must know how to detect a virtual machine installed on a host, acquire an image of a virtual machine, and use virtual machines to examine malware. The purpose of my virtual digital forensics lab is to provide a realistic and isolated environment for practicing and learning various digital forensics skills and techniques, such as data.
Comments are closed.