Virtual Machine Forensics Course Overview

Online Course Virtual Machine Forensics From Udemy Class Central In this course you will learn about virtual machines, hypervisors, different type 2 hypervisors, installing vm on your machine. files associated with popular hypervisors will be explained. Conducting forensics investigation on virtual machines.

Virtual Machine Forensics Course Online Codered Learn how to investigate virtual machines using ftk imager and osforensics. gain practical forensic skills with this step by step online course. Unlock the secrets hidden within virtual machines with our professional certificate in forensic analysis program. dive deep into the world of digital forensics and learn how to investigate and analyze virtual machine environments to uncover crucial evidence. • there are two types of hypervisors for running virtual machines: type 1 and type 2 • virtualization technology is intel’s cpu design for security and performance enhancements that enable the bios to support virtualization • forensic procedures for vms start by creating an image of the host machine, and then exporting files associated. This comprehensive course covers the setup and configuration of virtual environments for forensic analysis, enabling investigators to examine different operating systems such as windows and linux.
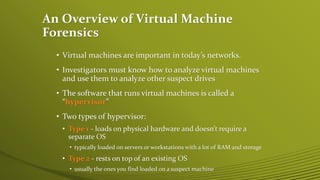
Virtual Machine Forensics Pptx • there are two types of hypervisors for running virtual machines: type 1 and type 2 • virtualization technology is intel’s cpu design for security and performance enhancements that enable the bios to support virtualization • forensic procedures for vms start by creating an image of the host machine, and then exporting files associated. This comprehensive course covers the setup and configuration of virtual environments for forensic analysis, enabling investigators to examine different operating systems such as windows and linux. Investigators can leverage vms to run forensic tools stored on usb drives, which is a portable solution for forensic analysis. steps to set up a vm on a usb drive are detailed on page 430, providing a practical approach to forensic investigations. Duration: 1 week summary: virtual machines are used extensively in computer systems and in teaching cyber security and digital forensics. understanding what they are and how they work is important for understanding the ramifications of these uses. In this article, we will explore the principles, methodologies, challenges, and best practices of virtual machine forensics, and explain how this emerging area is crucial for security and investigations professionals. This comprehensive course covers the setup and configuration of virtual environments for forensic analysis, enabling investigators to examine different operating systems such as windows, and linux.
Virtual Machine Forensics Pptx Investigators can leverage vms to run forensic tools stored on usb drives, which is a portable solution for forensic analysis. steps to set up a vm on a usb drive are detailed on page 430, providing a practical approach to forensic investigations. Duration: 1 week summary: virtual machines are used extensively in computer systems and in teaching cyber security and digital forensics. understanding what they are and how they work is important for understanding the ramifications of these uses. In this article, we will explore the principles, methodologies, challenges, and best practices of virtual machine forensics, and explain how this emerging area is crucial for security and investigations professionals. This comprehensive course covers the setup and configuration of virtual environments for forensic analysis, enabling investigators to examine different operating systems such as windows, and linux.
Comments are closed.