Virtual Machine Detection Using Malicious Javascript Malware Browser Exploit

Malicious Javascript Detection Tutorial In this short video i explain how browser based malware such as browser exploits can use javascript to reliably detect whether they are being executed run inside a security sand box ,. Over time the techniques have advanced as defenders learned new ways of avoiding vm detection. a while back a friend and i were working on a project related to exploit delivery via a web application for redteaming purposes.
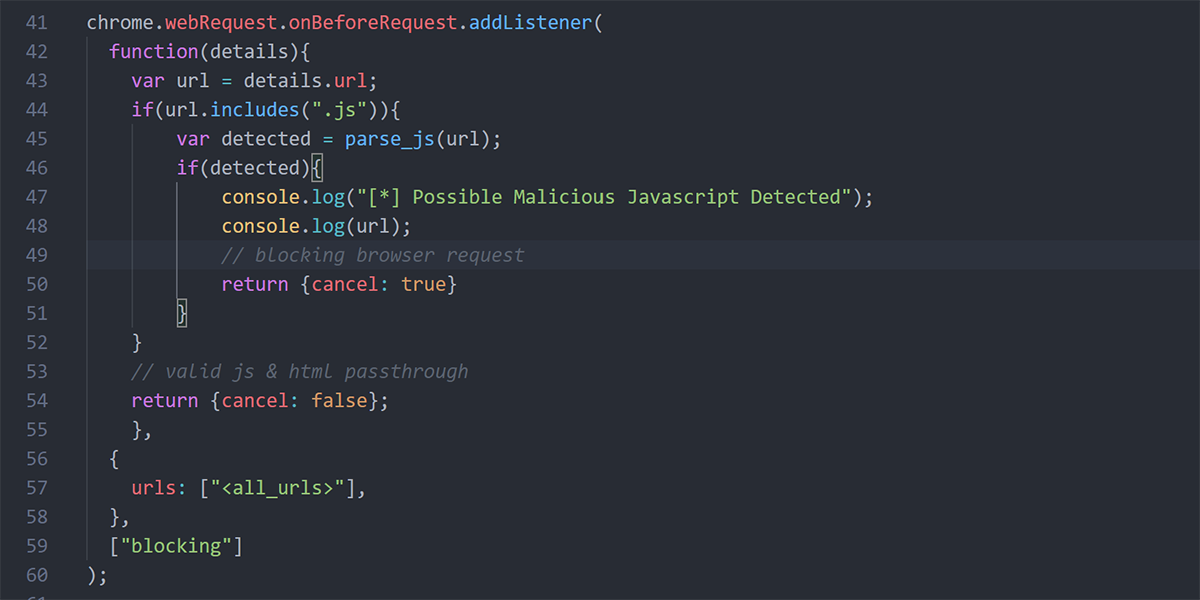
Building A Malicious Javascript Detection Pre Processor For A Chromium To summarize, while the default windows sandbox can be detected using javascript, by changing the configuration settings several can be eliminated from detection. This blog post covered four unique vm detection capabilities that can be performed from javascript. when i first discovered these techniques my initial thought was to apply the concepts toward vm detection. In this short video i explain how browser based malware such as browser exploits can use javascript to reliably detect whether they are being executed run inside a security sand box , virtual machine. This paper introduces javasith, a novel client side framework for analyzing potentially malicious extensions in web browsers, visual studio code (vscode), and node’s npm packages.
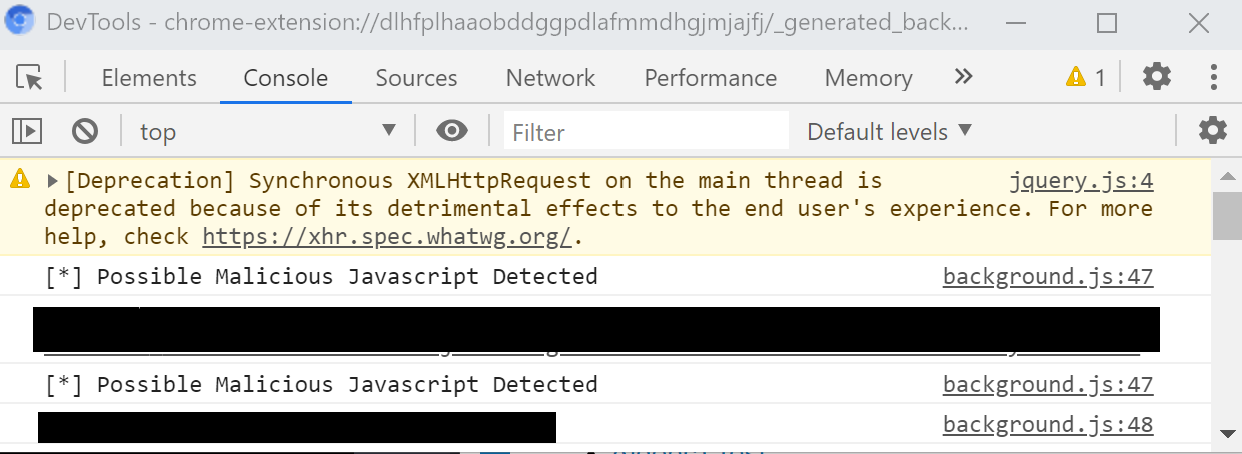
Building A Malicious Javascript Detection Pre Processor For A Chromium In this short video i explain how browser based malware such as browser exploits can use javascript to reliably detect whether they are being executed run inside a security sand box , virtual machine. This paper introduces javasith, a novel client side framework for analyzing potentially malicious extensions in web browsers, visual studio code (vscode), and node’s npm packages. We evaluate a malicious javascript injection campaign that has affected over 51,000 websites since 2022, and include campaign activity and variants. Today, we will delve into a step by step analysis of javascript malware, utilizing cutting edge techniques to deobfuscate and extract indicators of compromise (iocs) for enhanced cyber security. While it does use the browser as user interface, the whole analysis execution of the javascript code is done in the backend. as with any tool that handles malicious, unknown code, you should consider installing jsdetox into an isolated environment. While it does use the browser as user interface, the whole analysis execution of the javascript code is done in the backend. as with any tool that handles malicious, unknown code, you should consider installing jsdetox into an isolated environment.
Malicious Jquery Javascript Threat Detection Incident Response We evaluate a malicious javascript injection campaign that has affected over 51,000 websites since 2022, and include campaign activity and variants. Today, we will delve into a step by step analysis of javascript malware, utilizing cutting edge techniques to deobfuscate and extract indicators of compromise (iocs) for enhanced cyber security. While it does use the browser as user interface, the whole analysis execution of the javascript code is done in the backend. as with any tool that handles malicious, unknown code, you should consider installing jsdetox into an isolated environment. While it does use the browser as user interface, the whole analysis execution of the javascript code is done in the backend. as with any tool that handles malicious, unknown code, you should consider installing jsdetox into an isolated environment.

Pdf Obfuscated Malicious Javascript Detection Using Classification While it does use the browser as user interface, the whole analysis execution of the javascript code is done in the backend. as with any tool that handles malicious, unknown code, you should consider installing jsdetox into an isolated environment. While it does use the browser as user interface, the whole analysis execution of the javascript code is done in the backend. as with any tool that handles malicious, unknown code, you should consider installing jsdetox into an isolated environment.

Malware Analysis A Malicious Javascript Code R Hacking Tutorials
Comments are closed.