Vigenere Cipher Weaknesses Explained Pdf Cryptography Key

Vigenere Cipher Pdf Cipher Secrecy Vigenère cipher weaknesses explained the document provides an overview of cryptography, including its definitions, purposes, types, and various algorithms such as the caesar and vigenère ciphers. Through rigorous testing and analysis, we demonstrate that the modified vigenère cipher withstands various cryptanalytic techniques more effectively than its classical counterpart. this.

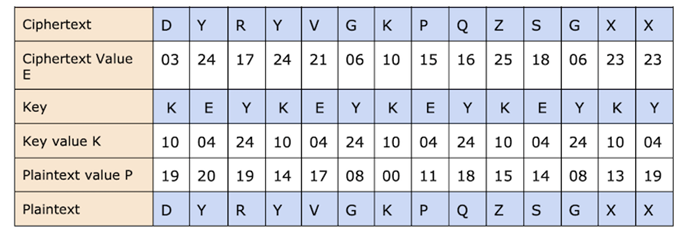
Vigenere Cipher Pdf Cipher Applied Mathematics Let qi denote the observed frequency of the i th english letter within a given ciphertext stream (qi is the number of times letter i appears in the ciphertext stream divided by the stream length) i of qi was obtained from letter i − j for key j therefore qi ≈ pi−j or equivalently qi j ≈ pi. Vigenere masks the frequency with which a character appears in a language: one letter in the ciphertext corresponds to multiple letters in the plaintext. makes the use of frequency analysis more difficult. This paper explores and compares the security aspects of three popular classical ciphers: the shift cipher, the vigenère cipher, and the affine cipher. each cipher’s mathematical formulation, key space size, and vulnerability to attacks such as brute force and frequency analysis are discussed. Hence, to decrypt a ciphertext encrypted with the vigen`ere cipher, one usually follows an iterative procedure as shown below. section 6 provides several complete examples.
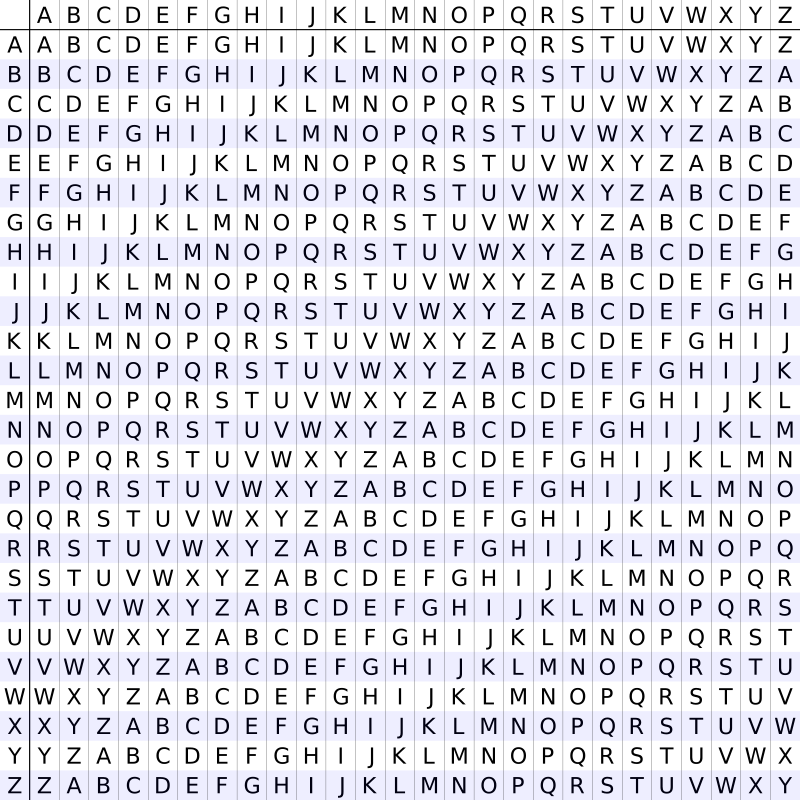
Vigenere Cipher Ctf Handbook This paper explores and compares the security aspects of three popular classical ciphers: the shift cipher, the vigenère cipher, and the affine cipher. each cipher’s mathematical formulation, key space size, and vulnerability to attacks such as brute force and frequency analysis are discussed. Hence, to decrypt a ciphertext encrypted with the vigen`ere cipher, one usually follows an iterative procedure as shown below. section 6 provides several complete examples. However, the vigenere cipher has vulnerabilities, particularly in brute force attacks when short keys are used. this research explores the technical specifications, strengths, and limitations of the vigenere cipher, comparing it with other classical and modern cryptographic algorithms. This report will investigate the vigenere cipher and attempt to find the key and decrypt the message, with only knowledge of the ciphertext. the analysis will be done using the kasiski test, as well as the index of coincidence method. Over the years, when vigenere cipher was no longer safe, researchers started suggesting various improvements to enhance the security of the vigenere cipher. kester (2012) proposed a cryptosystem based on vigenere cipher with varying key. Alice can garble the text in some way that bob can undo it atbash cipher! swap every letter with its opposite, a with z, b with y but eve can immediately figure it out alice tells bob a secret key to add complexity to the message this is a key idea in modern cryptography.

An Introduction To Classical Cryptographic Algorithms The Vigenere However, the vigenere cipher has vulnerabilities, particularly in brute force attacks when short keys are used. this research explores the technical specifications, strengths, and limitations of the vigenere cipher, comparing it with other classical and modern cryptographic algorithms. This report will investigate the vigenere cipher and attempt to find the key and decrypt the message, with only knowledge of the ciphertext. the analysis will be done using the kasiski test, as well as the index of coincidence method. Over the years, when vigenere cipher was no longer safe, researchers started suggesting various improvements to enhance the security of the vigenere cipher. kester (2012) proposed a cryptosystem based on vigenere cipher with varying key. Alice can garble the text in some way that bob can undo it atbash cipher! swap every letter with its opposite, a with z, b with y but eve can immediately figure it out alice tells bob a secret key to add complexity to the message this is a key idea in modern cryptography.
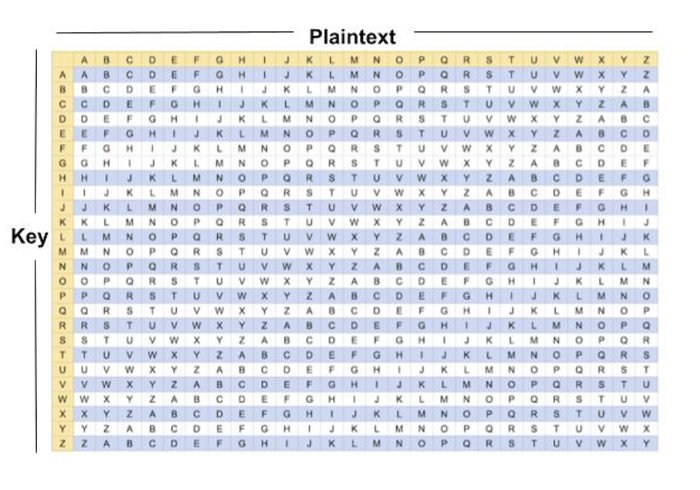
Cryptography Vigenere Cipher Over the years, when vigenere cipher was no longer safe, researchers started suggesting various improvements to enhance the security of the vigenere cipher. kester (2012) proposed a cryptosystem based on vigenere cipher with varying key. Alice can garble the text in some way that bob can undo it atbash cipher! swap every letter with its opposite, a with z, b with y but eve can immediately figure it out alice tells bob a secret key to add complexity to the message this is a key idea in modern cryptography.
Cryptography Vigenere Cipher
Comments are closed.