Vigenere Cipher In Cryptography

Vigenère Cipher In Cryptography Abdul Wahab Junaid Vigenere cipher is a method of encrypting alphabetic text. it uses a simple form of polyalphabetic substitution. a polyalphabetic cipher is any cipher based on substitution, using multiple substitution alphabets. the encryption of the original text is done using the vigenère square or vigenère table. The vigenère cipher is therefore a special case of a polyalphabetic substitution. [2][3] first described by giovan battista bellaso in 1553, the cipher is easy to understand and implement, but it resisted all attempts to break it until 1863, three centuries later.

Cryptography Vigenère Cipher The vigenère cipher is a classical cipher designed to defeat simple frequency analysis. instead of using one fixed substitution alphabet (like caesar), it uses many—changing the caesar shift with each character based on a keyword. An algorithm called the vigenere cipher is used to both encrypt and decrypt text. the vigenere cipher is an algorithm that uses a number of linked caesar ciphers to encrypt an alphabetic text. What is the vigenere cipher and how does it work? the vigenere cipher is a polyalphabetic substitution cipher invented by blaise de vigenere in the 16th century. it uses a keyword where each letter determines a different shift value (a=0, b=1, c=2, etc.). The vigenere cipher applies different caesar ciphers to consecutive letters. if the key is 'pub', the first letter is enciphered with a caesar cipher with key 16 (p is the 16th letter of the alphabet), the second letter with another, and the third letter with another.
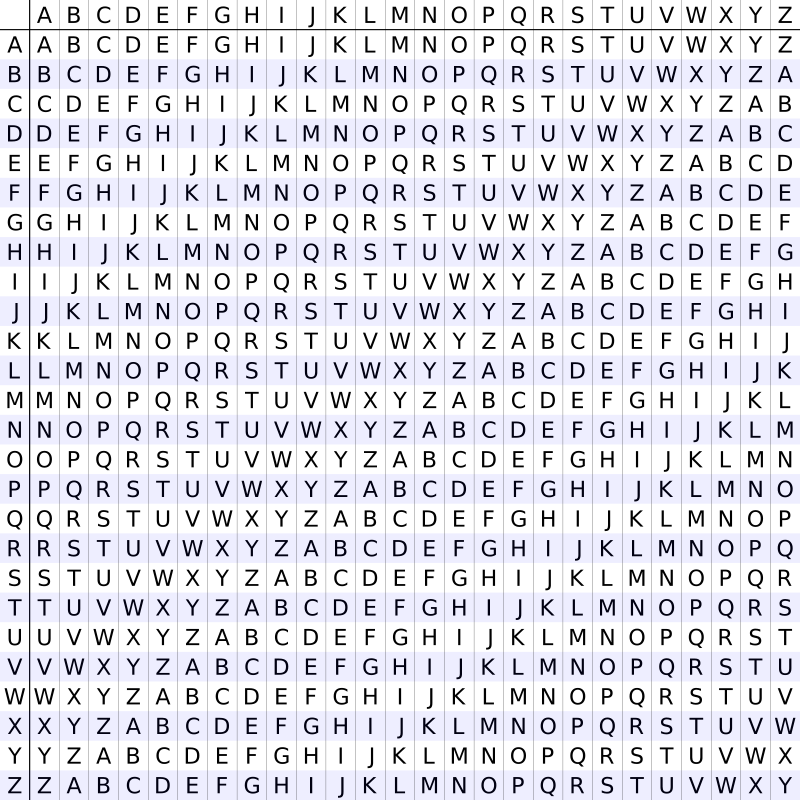
Vigenere Cipher Ctf Handbook What is the vigenere cipher and how does it work? the vigenere cipher is a polyalphabetic substitution cipher invented by blaise de vigenere in the 16th century. it uses a keyword where each letter determines a different shift value (a=0, b=1, c=2, etc.). The vigenere cipher applies different caesar ciphers to consecutive letters. if the key is 'pub', the first letter is enciphered with a caesar cipher with key 16 (p is the 16th letter of the alphabet), the second letter with another, and the third letter with another. Vigenere cipher, type of substitution cipher used for data encryption in which the original plaintext structure is somewhat concealed in the ciphertext by using several different monoalphabetic substitution ciphers rather than just one. Blaise de vigenère developed what is now called the vigenère cipher in 1585. he used a table known as the vigenère square, to encipher messages. this page discusses two different versions of the vigenère cipher, the autokey method and the keyword method. In 1863, a prussian major named kasiski proposed a method for breaking a vigenere cipher that consisted of finding the length of the keyword and then dividing the message into that many simple substitution cryptograms. Let qi denote the observed frequency of the i th english letter within a given ciphertext stream (qi is the number of times letter i appears in the ciphertext stream divided by the stream length) i of qi was obtained from letter i − j for key j therefore qi ≈ pi−j or equivalently qi j ≈ pi.
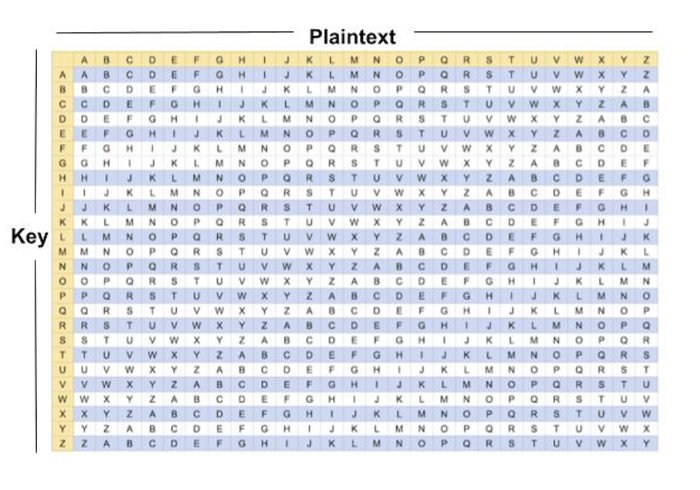
Cryptography Vigenere Cipher Vigenere cipher, type of substitution cipher used for data encryption in which the original plaintext structure is somewhat concealed in the ciphertext by using several different monoalphabetic substitution ciphers rather than just one. Blaise de vigenère developed what is now called the vigenère cipher in 1585. he used a table known as the vigenère square, to encipher messages. this page discusses two different versions of the vigenère cipher, the autokey method and the keyword method. In 1863, a prussian major named kasiski proposed a method for breaking a vigenere cipher that consisted of finding the length of the keyword and then dividing the message into that many simple substitution cryptograms. Let qi denote the observed frequency of the i th english letter within a given ciphertext stream (qi is the number of times letter i appears in the ciphertext stream divided by the stream length) i of qi was obtained from letter i − j for key j therefore qi ≈ pi−j or equivalently qi j ≈ pi.
Comments are closed.