Verifying Git Commits Using Gpg R Devto

Verifying Git Commits Using Gpg R Devto R stablediffusion is back open after the protest of reddit killing open api access, which will bankrupt app developers, hamper moderation, and exclude blind users from the site. By signing your commits with a gpg (gnu privacy guard) key, you cryptographically verify that the code came from you and hasn't been altered. github (and gitlab) rewards this with a shiny green "verified" badge.
Verifying Git Commits Using Gpg Dev Community рџ вђќрџ рџ ёвђќрџ Git solves a lot of development problems, but there are just as many loopholes for spoofing. git commits are based on trust, and most commit developers use simple credentials to identify the commit author, such as user.name and user.email. Git 2.19 (q3 2018) is even more helpful, since " git verify tag " and " git verify commit " have been taught to use the exit status of underlying " gpg verify " to signal bad or untrusted signature they found. Using gpg, ssh, or s mime, you can sign tags and commits locally. these tags or commits are marked as verified on github so other people can be confident that the changes come from a trusted source. Git is cryptographically secure, but it’s not foolproof. if you’re taking work from others on the internet and want to verify that commits are actually from a trusted source, git has a few ways to sign and verify work using gpg.
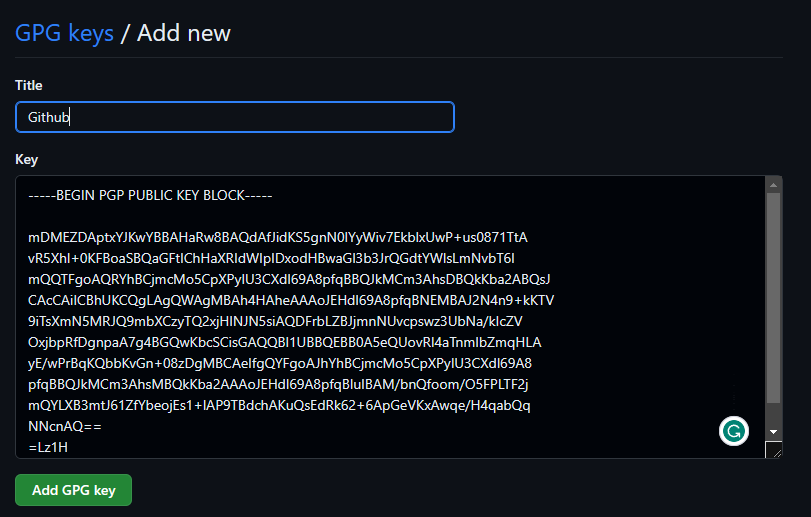
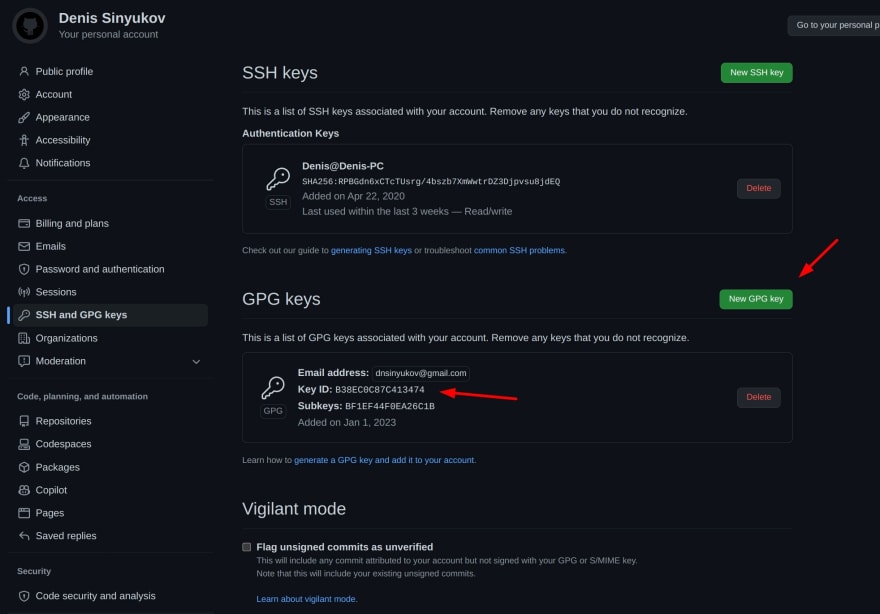
Configure Gpg To Sign Git Commits In Windows Using gpg, ssh, or s mime, you can sign tags and commits locally. these tags or commits are marked as verified on github so other people can be confident that the changes come from a trusted source. Git is cryptographically secure, but it’s not foolproof. if you’re taking work from others on the internet and want to verify that commits are actually from a trusted source, git has a few ways to sign and verify work using gpg. Using gpg (gnu privacy guard) to sign git commits is a powerful way to secure your code and verify authenticity. in this post, i’ll walk you through everything — from getting started with. Learn how to sign an existing git commit with gpg keys to add authenticity and security to your version control workflow. this quick and casual guide walks you through setting up a gpg key, amending commits to include a signature, and verifying the results—all with accurate commands. This guide shows you how to get the “verified” badge on your github commits by generating a gpg key pair, configuring gpg agent and pinentry, and registering your public key with github. For gitlab to consider a commit verified: the committer must have a gpg public private key pair. the committer’s public key must be uploaded to their gitlab account. one of the email addresses in the gpg public key must match a verified email address used by the committer in gitlab.
Comments are closed.