Validated Patterns Loading Secrets
Retail Validated Patterns Validated patterns supports the tokenization approach for secret management. tokenization involves keeping actual secret values out of version control (for example git) by using tokens or references that can pull secrets from secure storage during runtime. In order to load the secrets out of band into the vault you can copy the values secret.yaml.template inside the pattern's git repo to ~ values secret
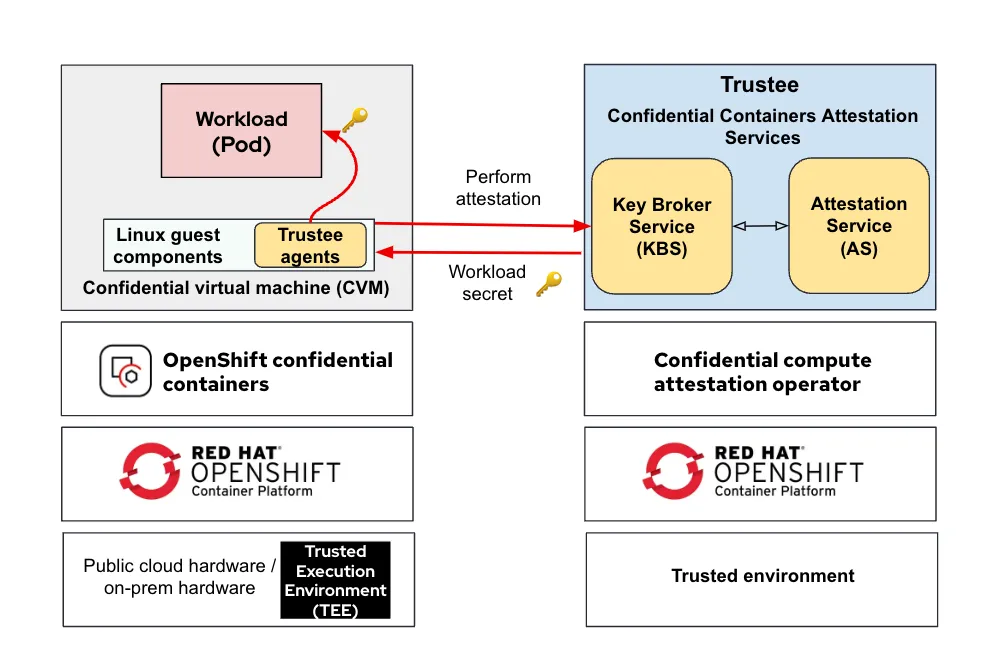
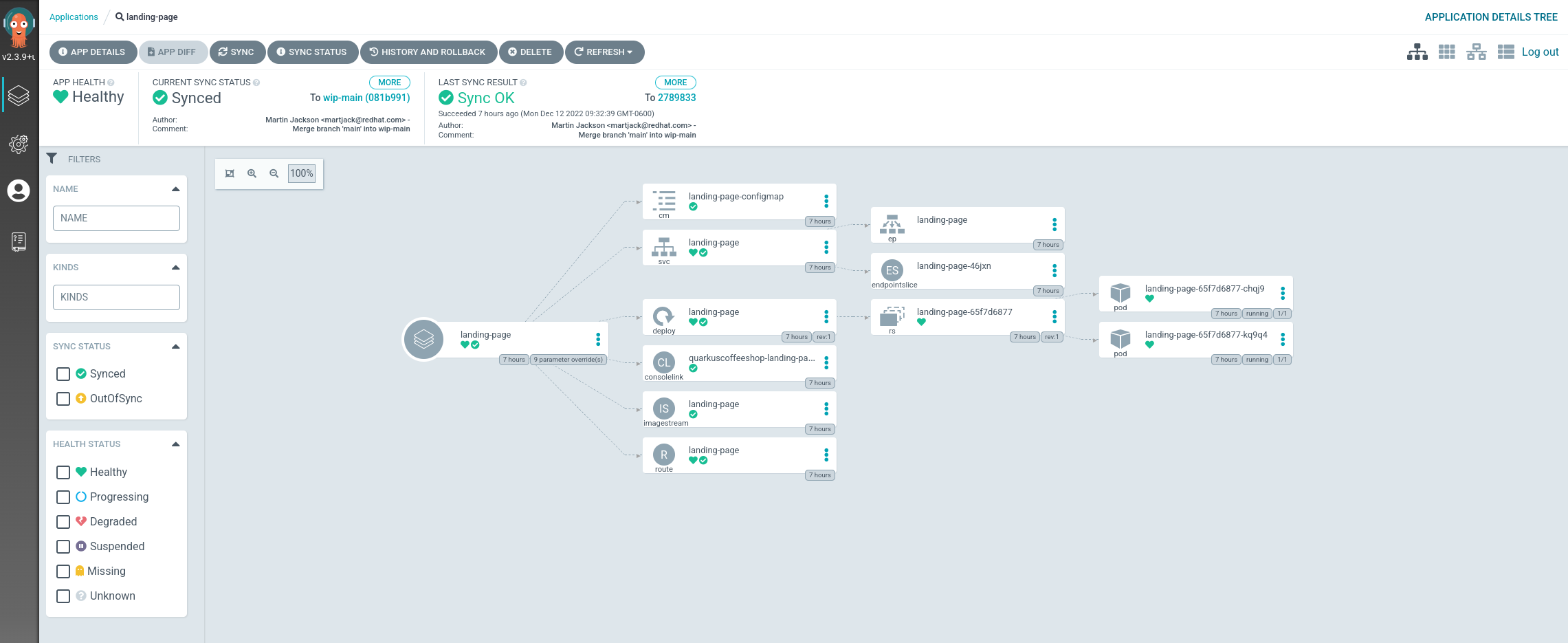
Confidential Containers Pattern Validated Patterns Now that you’ve prepared your environment, we’ll walk through how to deploy a validated pattern on your cluster. this learning path deploys the multicloud gitops validated pattern, because it demonstrates the gitops approach to managing multiple cloud deployments in both public and private clouds. This document provides troubleshooting guidance for common issues encountered when configuring and deploying secrets management in validated patterns. it covers diagnostic procedures, root cause analysis, and resolution steps for external secrets operator (eso), sealed secrets, and backend integration problems. Secret volume sources are validated to ensure that the specified object reference actually points to an object of type secret. therefore, a secret needs to be created before any pods that depend on it. This validated architecture describes a github action pipeline requesting access to vault to retrieve secrets. the github action uses the hashicorp vault action@v2 action and jwt to authenticate and retrieve secrets from vault.
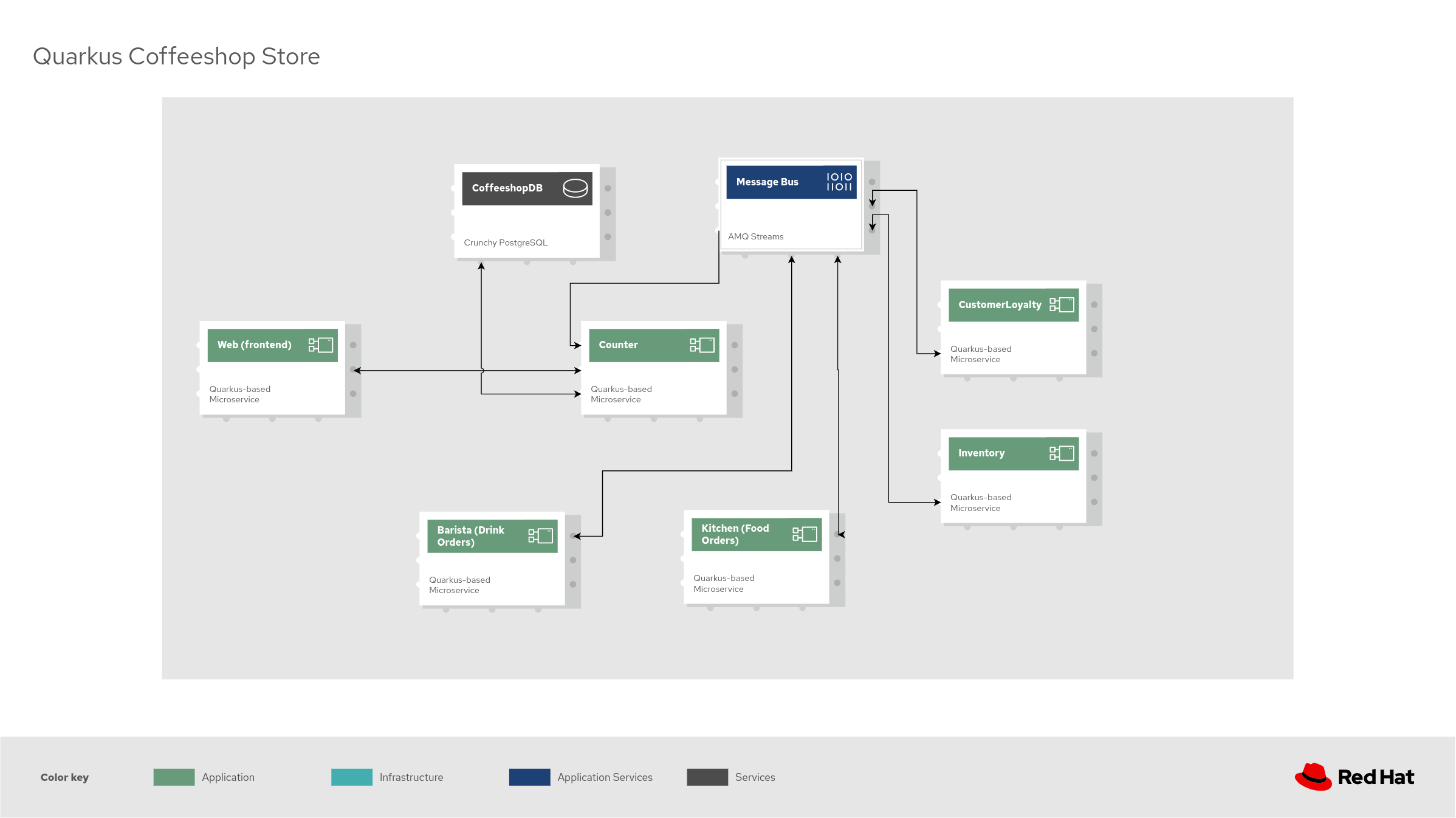
Details Of The Components Validated Patterns Secret volume sources are validated to ensure that the specified object reference actually points to an object of type secret. therefore, a secret needs to be created before any pods that depend on it. This validated architecture describes a github action pipeline requesting access to vault to retrieve secrets. the github action uses the hashicorp vault action@v2 action and jwt to authenticate and retrieve secrets from vault. A nice feature of validated patterns sit that the secrets bootstrapping when calling . pattern.sh make install and . pattern.sh make load secrets explicitly does not look in the cloned source repo. We have learned that the validated pattern for hybrid multicloud management provides a framework to deploy applications and application secrets consistently on different clouds and infrastructures using openshift and the gitops paradigm. Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on . Every node.js app has secrets — database passwords, api keys, jwt signing keys, webhook tokens. most applications handle them wrong. they get committed to git, printed in logs, exposed in error messages, or baked into docker images. in production, a single leaked secret can mean a full breach.
Comments are closed.