Using The Event Mapping Framework To Enforce Two Factor Authentication
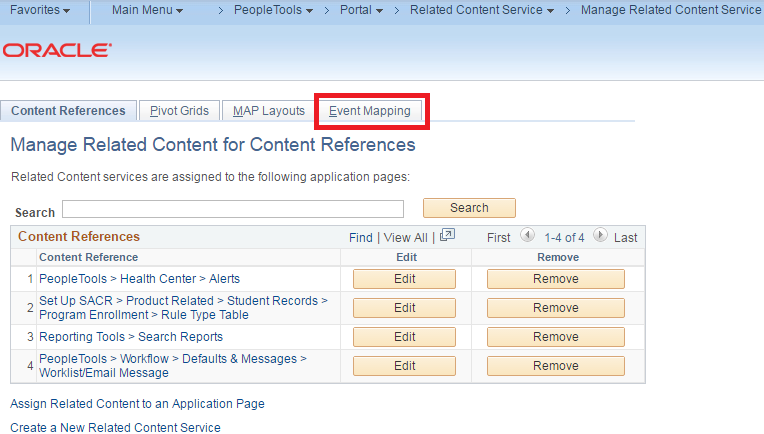
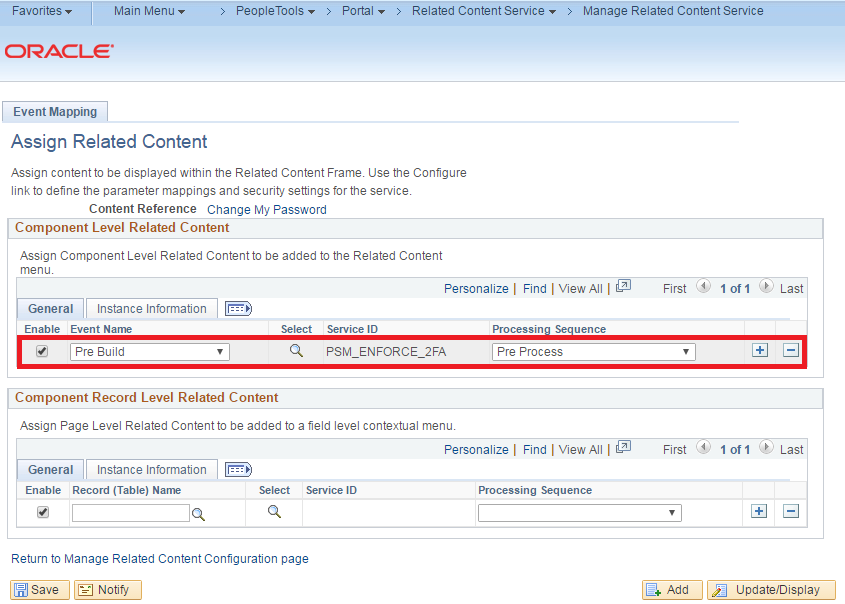
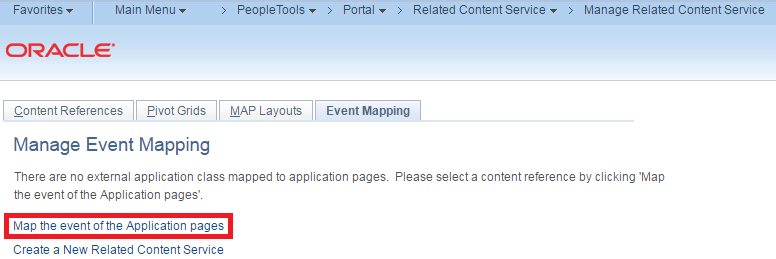
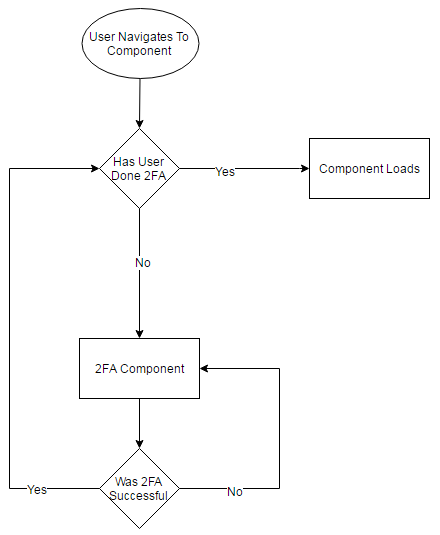
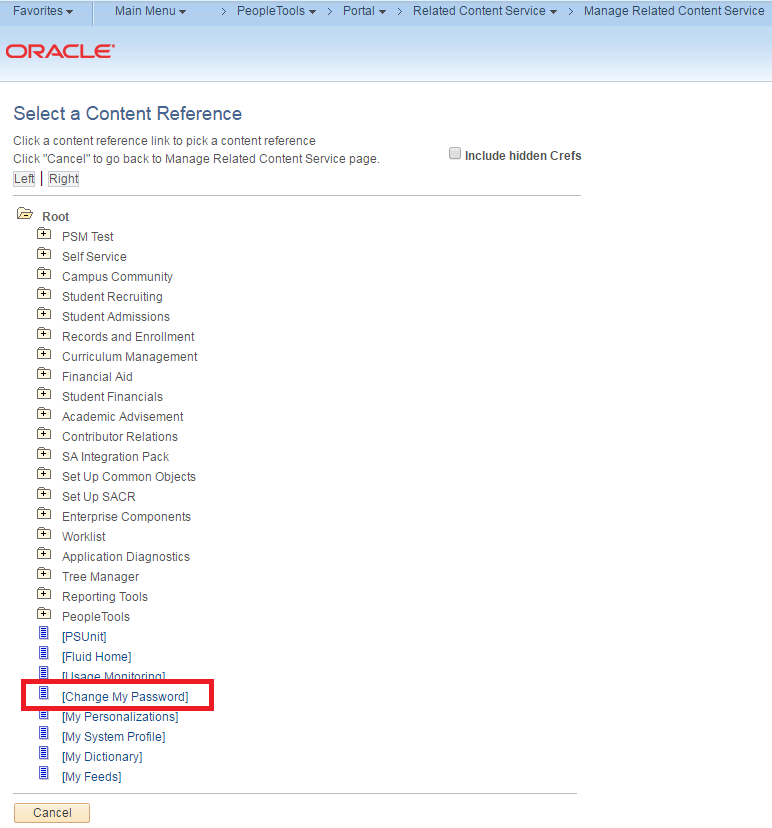
Using The Event Mapping Framework To Enforce Two Factor Authentication I am going to demonstrate how the event mapping framework can be used to enforce two factor authentication (2fa) by mapping application class peoplecode to component events. i have provided a proof of concept project that demonstrates this functionality. I am going to provide a tutorial on how to setup two factor authentication (2fa) in peoplesoft. this is going to serve as a technical demonstration (and documentation) of how i satisfied the project requirements that were outlined in this post.
Using The Event Mapping Framework To Enforce Two Factor Authentication Provide users the option to enable mfa using totp. always enforce mfa for administrators or high‑privilege accounts. implement a secure mfa reset process (recovery codes, support workflow). consider third‑party mfa providers if you lack the resources to build and maintain your own implementation. Learn how to implement and test two factor authentication to protect your users and data. Two factor authentication or 2fa is an advanced method of user authentication and a subset of multi factor authentication mechanisms. 2fa enhances the security of its user accounts by adding another layer of authenticity challenge after traditional passwords used in single factor authentication. While uaf focuses on passwordless authentication, u2f allows the addition of a second factor to existing password based authentication. both protocols are based on a public key cryptography challenge response model.
Using The Event Mapping Framework To Enforce Two Factor Authentication Two factor authentication or 2fa is an advanced method of user authentication and a subset of multi factor authentication mechanisms. 2fa enhances the security of its user accounts by adding another layer of authenticity challenge after traditional passwords used in single factor authentication. While uaf focuses on passwordless authentication, u2f allows the addition of a second factor to existing password based authentication. both protocols are based on a public key cryptography challenge response model. There are many different terms to describe multi factor authentication. sometimes it’s called two step verification, two factor authentication (2fa), one time password (otp), or strong authentication. In this post i'll describe how to to implement authenticator based verification outside of the context of asp identity, so you can add this to just about any solution. Learn how to effectively implement multi factor authentication (mfa) to enhance cybersecurity and protect against unauthorized access. this guide covers planning, deployment, and best practices. This dual layered technique usually combines a password with a one time code from an authentication app or sms.
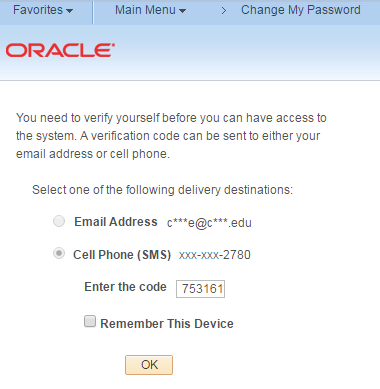
Using The Event Mapping Framework To Enforce Two Factor Authentication There are many different terms to describe multi factor authentication. sometimes it’s called two step verification, two factor authentication (2fa), one time password (otp), or strong authentication. In this post i'll describe how to to implement authenticator based verification outside of the context of asp identity, so you can add this to just about any solution. Learn how to effectively implement multi factor authentication (mfa) to enhance cybersecurity and protect against unauthorized access. this guide covers planning, deployment, and best practices. This dual layered technique usually combines a password with a one time code from an authentication app or sms.
Using The Event Mapping Framework To Enforce Two Factor Authentication Learn how to effectively implement multi factor authentication (mfa) to enhance cybersecurity and protect against unauthorized access. this guide covers planning, deployment, and best practices. This dual layered technique usually combines a password with a one time code from an authentication app or sms.
Using The Event Mapping Framework To Enforce Two Factor Authentication
Comments are closed.