Using Linux To Intercept Iot Device Traffic
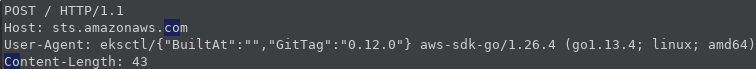
Intercept Linux Cli Tool Traffic In this video, david bombal interviews cybersecurity researcher and iot penetration tester, matt brown, to reveal how to intercept and decrypt supposedly secure ssl tls traffic from iot devices. matt demonstrates his open source tool, “man in the middle router,” a specialized linux based bash script designed to simplify iot hardware hacking labs. This channel is a place where i share my knowledge and experience finding vulnerabilities in iot systems. soli deo gloria 💻 social: website: brownfinesecurity x: x nmatt0 linkedin: linkedin in mattbrwn github: github nmatt0.

Iot In Traffic Monitoring Use Cases Advantages Features More This channel is a place where i share my knowledge and experience finding vulnerabilities in iot systems. Interceptsuite is a cross platform network traffic interception tool for tcp, udp, dtls, and tls protocols. operating at the transport layer, it provides comprehensive visibility into encrypted traffic from iot devices, thick clients, databases, gaming applications, and custom protocols. Interceptsuite is a cross platform network traffic interception tool for tcp, udp, dtls, and tls protocols. operating at the transport layer, it provides comprehensive visibility into encrypted traffic from iot devices, thick clients, databases, gaming applications, and custom protocols. In this paper, we systemat ically present the first manual reverse engineering framework for discovering communication protocols of embedded linux based iot systems. we have successfully applied our framework to reverse engineer a number of iot systems.
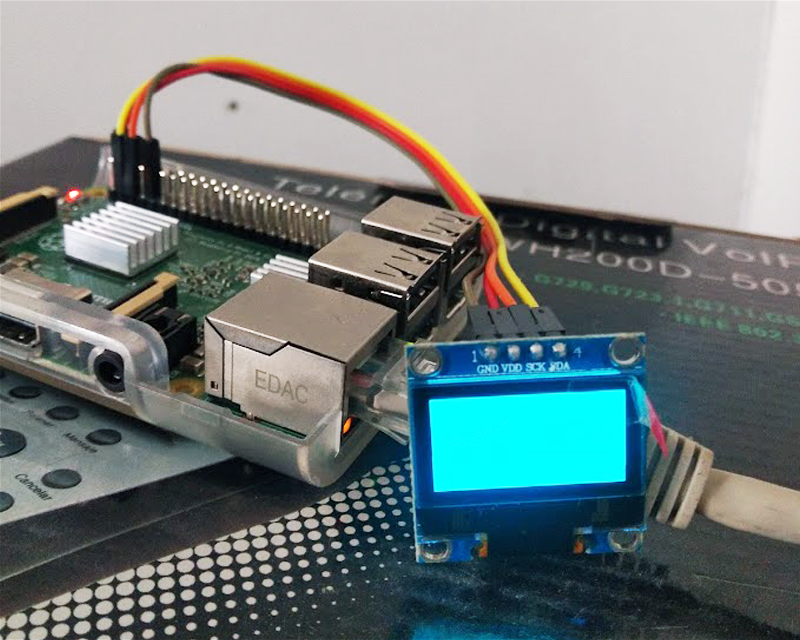
How To Connect An Iot Device To An Industrial Platform Using Embedded Interceptsuite is a cross platform network traffic interception tool for tcp, udp, dtls, and tls protocols. operating at the transport layer, it provides comprehensive visibility into encrypted traffic from iot devices, thick clients, databases, gaming applications, and custom protocols. In this paper, we systemat ically present the first manual reverse engineering framework for discovering communication protocols of embedded linux based iot systems. we have successfully applied our framework to reverse engineer a number of iot systems. This vulnerability highlights the importance of securing mqtt communication channels and properly protecting sensitive information to prevent unauthorized control of iot devices. Students will use a provided kali linux vm to set up the infrastructure to intercept network traffic from a simulated openwrt device and use the mitmproxy tool suite to decrypt tls encrypted. When man in the middle ing a device, we intercept and inspect the online traffic that goes in and out of it. this allows us to understand, and potentially modify, how it works. Kali linux can be used to perform a variety of penetration tests on your pc. here are some penetration testing strategies for iot devices with kali linux.

How To Connect An Iot Device To An Industrial Platform Using Embedded This vulnerability highlights the importance of securing mqtt communication channels and properly protecting sensitive information to prevent unauthorized control of iot devices. Students will use a provided kali linux vm to set up the infrastructure to intercept network traffic from a simulated openwrt device and use the mitmproxy tool suite to decrypt tls encrypted. When man in the middle ing a device, we intercept and inspect the online traffic that goes in and out of it. this allows us to understand, and potentially modify, how it works. Kali linux can be used to perform a variety of penetration tests on your pc. here are some penetration testing strategies for iot devices with kali linux.

Linux Security For Iot Devices What You Need To Know When man in the middle ing a device, we intercept and inspect the online traffic that goes in and out of it. this allows us to understand, and potentially modify, how it works. Kali linux can be used to perform a variety of penetration tests on your pc. here are some penetration testing strategies for iot devices with kali linux.
Comments are closed.