Using Intermediate Wireshark 3 Features

Wireshark Tutorial For Intermediate Beginners Pdf In this course, using intermediate wireshark features , you’ll learn to move beyond the basics with wireshark. first, you’ll explore the networking fundamentals that underpin wireshark. next, you’ll discover how to analyze http and https traffic with wireshark. By the end of this course, you'll possess the advanced wireshark skills and knowledge necessary to perform sophisticated network troubleshooting, performance monitoring, and security investigations – taking your network analysis to a whole new level.
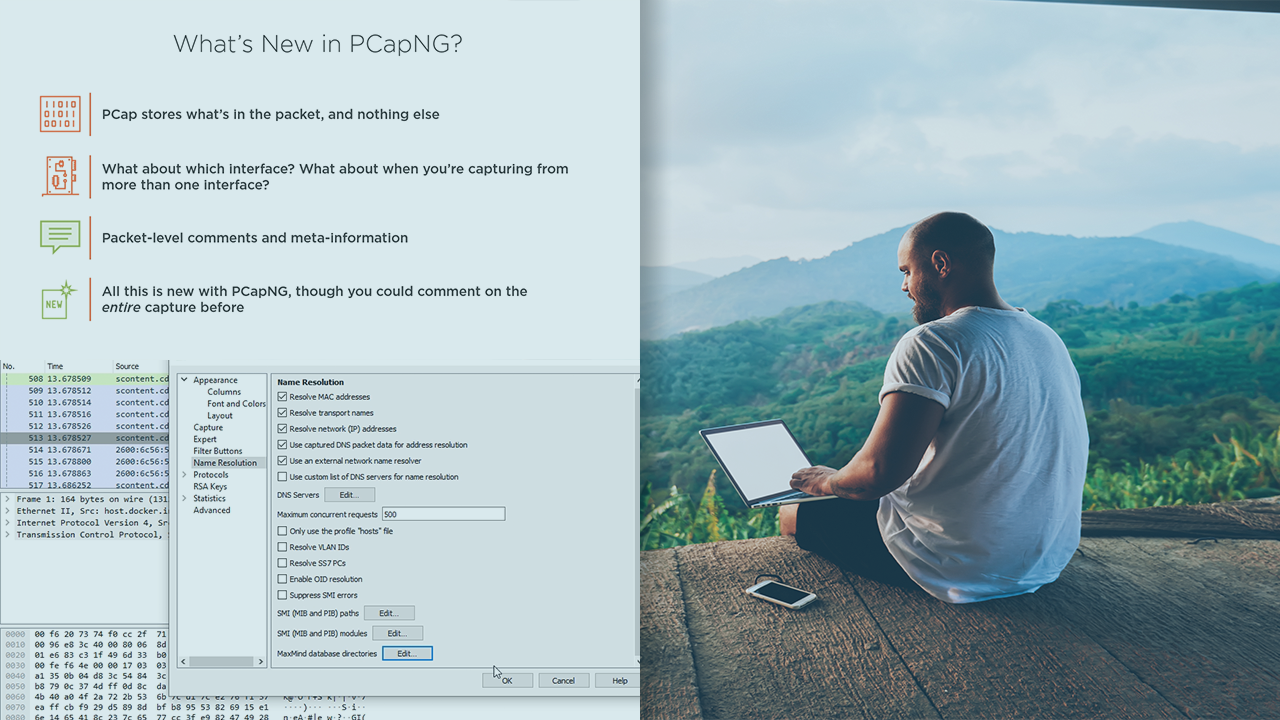
Using Intermediate Wireshark 3 Features Learn to use advanced features such as http traffic analysis, forensic analysis, and basic customization to take your network analysis to the next level. the content presented here is sourced directly from pluralsight platform. This course will teach you how to use intermediate wireshark features. wireshark allows you to go beyond the basics. first, you'll explore? wireshark's networking foundations. ? next, you'll discover? wireshark enables you to analyse https and https traffic. finally, you will learn how to: you can customize and automate wireshark. When you need to take a closer look at network traffic, wireshark is the go to tool for most network engineers. in this course, using intermediate wireshark features , you’ll learn to move beyond the basics with wireshark. Intermediate level display filters enable complex packet matching across multiple protocol layers. combine conditions with logical operators (&&, ||, !) to isolate specific traffic patterns. essential for packet dissection and anomaly detection in large pcap files.

Wireshark Tutorial For Intermediate Beginners Pdfcoffee Com When you need to take a closer look at network traffic, wireshark is the go to tool for most network engineers. in this course, using intermediate wireshark features , you’ll learn to move beyond the basics with wireshark. Intermediate level display filters enable complex packet matching across multiple protocol layers. combine conditions with logical operators (&&, ||, !) to isolate specific traffic patterns. essential for packet dissection and anomaly detection in large pcap files. In this course, using intermediate wireshark features , you’ll learn to move beyond the basics with wireshark. first, you’ll explore the networking fundamentals that underpin wireshark. In this course, using intermediate wireshark features , you’ll learn to move beyond the basics with wireshark. first, you’ll explore the networking fundamentals that underpin wireshark. 1.1. what is wireshark? 1.1.1. some intended purposes 1.1.2. features 1.1.3. live capture from many different network media 1.1.4. import files from many other capture programs 1.1.5. export files for many other capture programs 1.1.6. many protocol dissectors. This course provides an in depth look at wireshark configuration for cyber security analysis, including the best settings and filters to identify malware behavior, enumeration and scans, and other suspicious traffic.
Packt Advance Your Knowledge In Tech In this course, using intermediate wireshark features , you’ll learn to move beyond the basics with wireshark. first, you’ll explore the networking fundamentals that underpin wireshark. In this course, using intermediate wireshark features , you’ll learn to move beyond the basics with wireshark. first, you’ll explore the networking fundamentals that underpin wireshark. 1.1. what is wireshark? 1.1.1. some intended purposes 1.1.2. features 1.1.3. live capture from many different network media 1.1.4. import files from many other capture programs 1.1.5. export files for many other capture programs 1.1.6. many protocol dissectors. This course provides an in depth look at wireshark configuration for cyber security analysis, including the best settings and filters to identify malware behavior, enumeration and scans, and other suspicious traffic.
Comments are closed.