Using Gpg
Encrypting And Decrypting Files With Gpg It’s easy to get started with gpg, and you can be on your way with using it in a matter of minutes. in this tutorial, i’ll show you how to encrypt and decrypt files with gpg. Learn how gpg encryption protects your data through authenticity, integrity and nonrepudiation. this guide covers installation and symmetric and asymmetric cryptography basics.
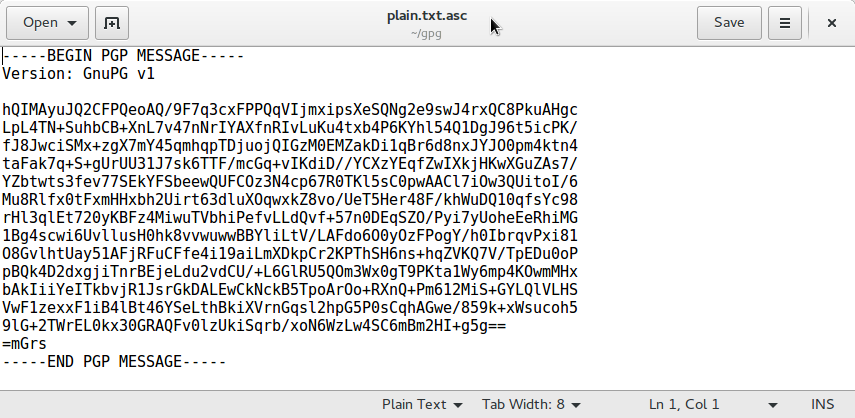
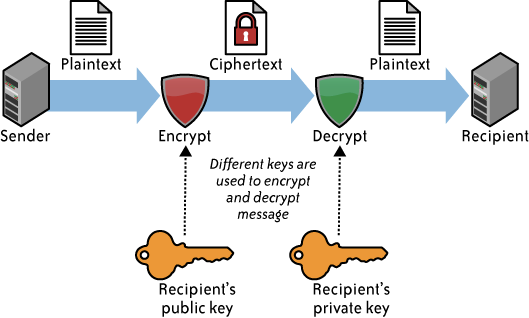
Gpg Using Your Key Fedora Magazine In this article, we show you how to encrypt files with gpg in linux, generate key pairs, share encrypted files securely, and decrypt them. This exploration highlights the versatility of gpg in handling various tasks — from key generation to data encryption and decryption, all essential for secure digital communication and file management. Gpg, or gnu privacy guard, is a public key cryptography implementation. this allows for the secure transmission of information between parties and can be used to verify that the origin of a message is genuine. in this guide, we will discuss how gpg works and how to implement it. This guide provides a comprehensive overview for setting up gpg on windows (using the gpg4win ui tool), macos, and linux with modern ecc encryption, managing keys, and securely encrypting decrypting files while following best practices for encryption security.
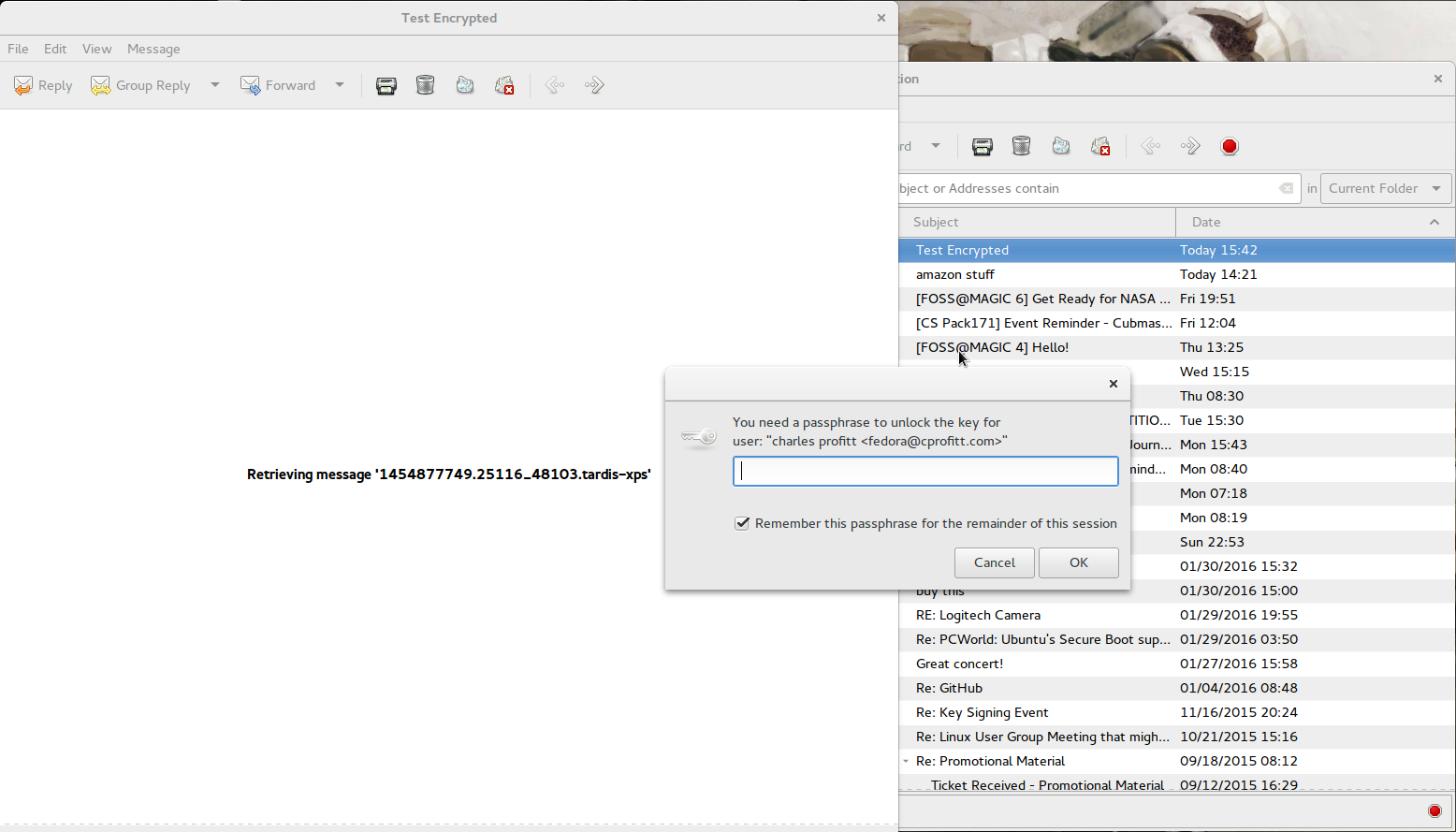
Gpg Using Your Key Fedora Magazine Gpg, or gnu privacy guard, is a public key cryptography implementation. this allows for the secure transmission of information between parties and can be used to verify that the origin of a message is genuine. in this guide, we will discuss how gpg works and how to implement it. This guide provides a comprehensive overview for setting up gpg on windows (using the gpg4win ui tool), macos, and linux with modern ecc encryption, managing keys, and securely encrypting decrypting files while following best practices for encryption security. In approximately 1 minute or less, you‘ll have gpg command accessible in your terminal. next we‘ll cover generating your key pairs to control encryption and decryption access. Discover how to protect sensitive data using `gpg`, a robust encryption tool, as cybersecurity threats increase. this guide covers everything from `gpg` installation across various operating systems to generating key pairs and encrypting decrypting files. Gpg is an invaluable tool for anyone seeking to secure their files and communications in a linux environment. this guide has walks you through the essentials, from installation to encrypting and decrypting files. A few years ago i wrote a guide about using gpg from the command line. it explains how openpgp works, how keys work, and what is actually happening when you encrypt or sign data: easy gpg that part ha.
1 What Is Gpg In approximately 1 minute or less, you‘ll have gpg command accessible in your terminal. next we‘ll cover generating your key pairs to control encryption and decryption access. Discover how to protect sensitive data using `gpg`, a robust encryption tool, as cybersecurity threats increase. this guide covers everything from `gpg` installation across various operating systems to generating key pairs and encrypting decrypting files. Gpg is an invaluable tool for anyone seeking to secure their files and communications in a linux environment. this guide has walks you through the essentials, from installation to encrypting and decrypting files. A few years ago i wrote a guide about using gpg from the command line. it explains how openpgp works, how keys work, and what is actually happening when you encrypt or sign data: easy gpg that part ha.
Gpg Guide Gpg is an invaluable tool for anyone seeking to secure their files and communications in a linux environment. this guide has walks you through the essentials, from installation to encrypting and decrypting files. A few years ago i wrote a guide about using gpg from the command line. it explains how openpgp works, how keys work, and what is actually happening when you encrypt or sign data: easy gpg that part ha.
Comments are closed.