Using Github To Look At Source For A Cve Hackthebox Forgot
Github S Dark Side Unveiling Malware Disguised As Cracks Hacks And The leading cyber readiness platform for the agentic era, battle testing and upskilling both humans and ai agents. helm chart for deploying typesense on kubernetes with ha clustering, prometheus metrics, and gateway api support. not affiliated with the typesense project. a prometheus exporter for php fpm. This blog post is an in depth walkthrough on how we perform security research leveraging github features, including code scanning, codeql, and codespaces.
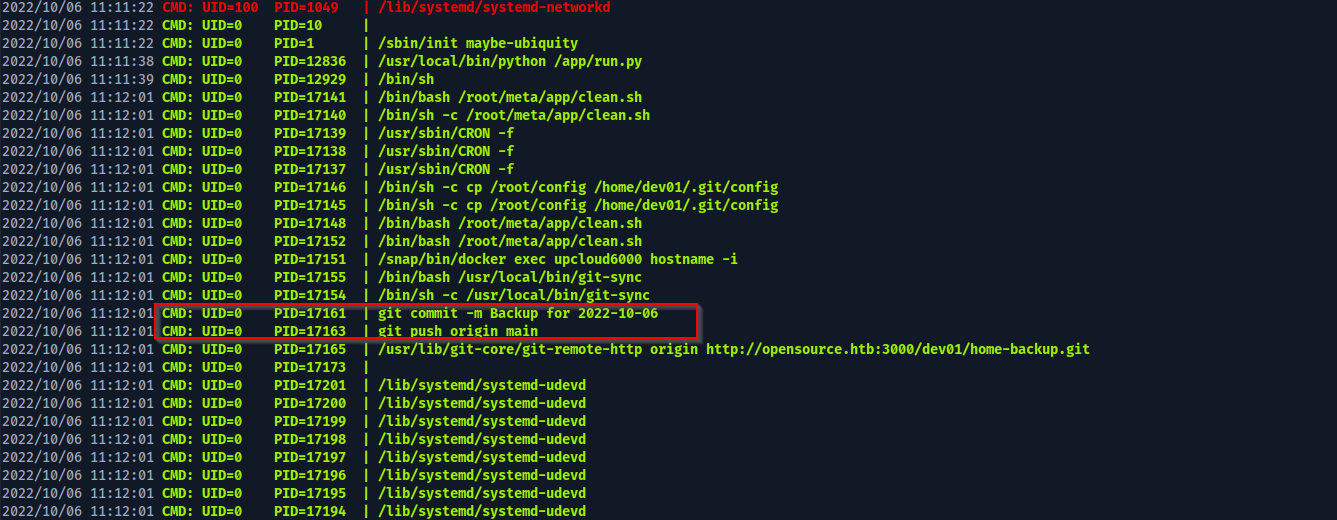
Hackthebox Opensource Saad Akhtar By exploiting this vulnerability, attackers can run arbitrary commands under the same user as the web server process. i came across an exploit for the cve 2022 46169 vulnerability in this github repo, which i then downloaded onto my attacking machine. Explore forrester's objective evaluation of cybersecurity training platforms, with a spotlight on the capabilities security teams need for ai enabled operations. why hack the box? join our mission to create a safer cyber world by making cybersecurity training fun and accessible to everyone. Let’s now “zoom out” a little, and get a broader view at what’s happening as part of this attack we know that the attacker used a poc for the relevant cve to gain access to the server, and it looks like they also used more than one host as part of the attack. As a beginner, looking at github for a large opensource project can be intimidating. i'll show how to find th more. in forgot from hackthebox, i'll need to exploit an insecure use of.
Github Artikrh Hackthebox Collection Of Scripts And Documentations Let’s now “zoom out” a little, and get a broader view at what’s happening as part of this attack we know that the attacker used a poc for the relevant cve to gain access to the server, and it looks like they also used more than one host as part of the attack. As a beginner, looking at github for a large opensource project can be intimidating. i'll show how to find th more. in forgot from hackthebox, i'll need to exploit an insecure use of. So this is my write up on one of the hackthebox machines called opensource. let’s go! as usual first of we start with an nmap scan. okay, so there are three ports provided, ports 22, 80, and. Conquer code on hackthebox like a pro with our beginner's guide. dominate this challenge and level up your cybersecurity skills. This linux based ctf (capture the flag) involves exploiting documented cves to gain root access. in this guide, we’ll break down the attack chain, from initial foothold to privilege escalation, using verified commands and techniques. The initial foothold involves discovering an exposed .git directory that can be dumped to retrieve credentials. these credentials allow access to the ghost content management system vulnerable to cve 2023 40028.
Github Occhima Hackthebox Setup So this is my write up on one of the hackthebox machines called opensource. let’s go! as usual first of we start with an nmap scan. okay, so there are three ports provided, ports 22, 80, and. Conquer code on hackthebox like a pro with our beginner's guide. dominate this challenge and level up your cybersecurity skills. This linux based ctf (capture the flag) involves exploiting documented cves to gain root access. in this guide, we’ll break down the attack chain, from initial foothold to privilege escalation, using verified commands and techniques. The initial foothold involves discovering an exposed .git directory that can be dumped to retrieve credentials. these credentials allow access to the ghost content management system vulnerable to cve 2023 40028.
Comments are closed.