Using Github Actions Watch Out For This Command Injunction Vulnerability
Actions Github Latest Version Includes Many Vulnerabilities Detected When creating workflows, custom actions, and composite actions, you should always consider whether your code might execute untrusted input from attackers. this can occur when an attacker adds malicious commands and scripts to a context. In this article, we’ll break down how command and code injection can happen in github actions, explore common attack patterns, show how to detect it in code, and end with practical advice to avoid these issues in your own workflows.

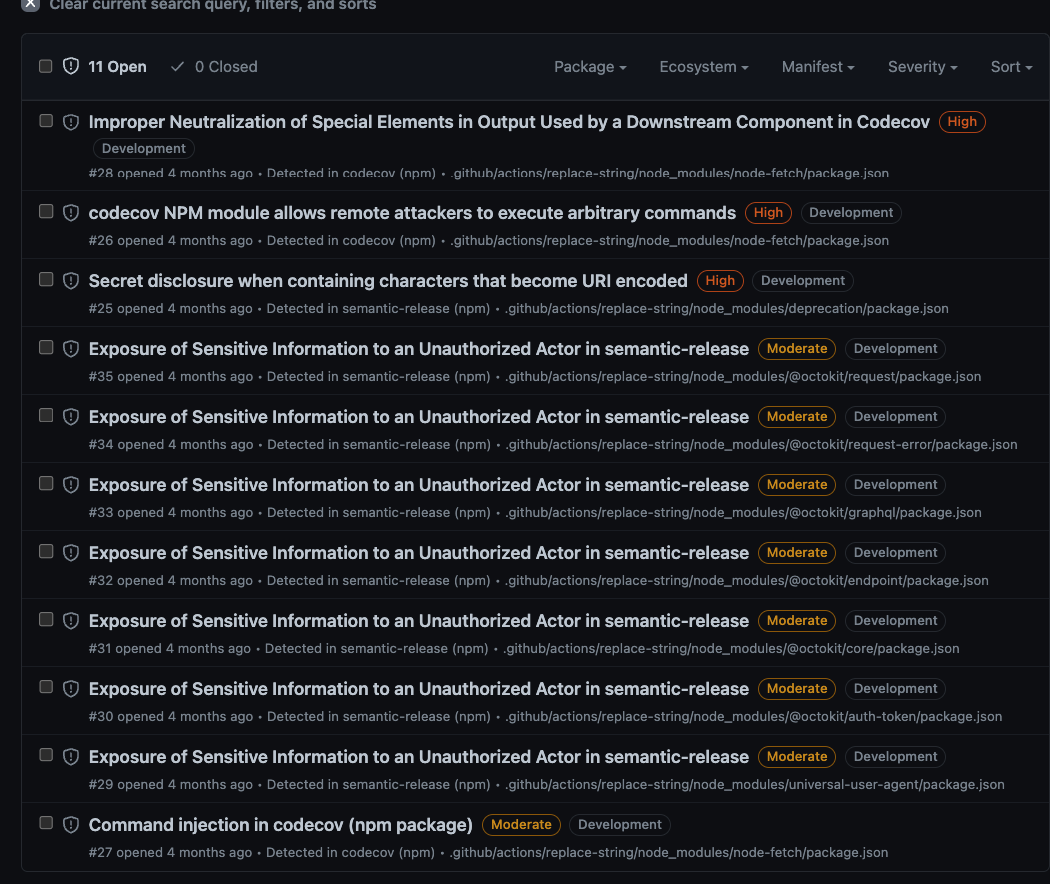
Workflow Commands For Github Actions Github Docs We recently made the ability to scan github actions workflow files generally available, and you can use this feature to look for several types of vulnerabilities, such as potential actions workflow injection risks. If you're not careful, attackers can inject malicious code into your workflow. let me show you the vulnerable pattern i discovered, then how to fix it. In this two part series we cover some of the many security considerations when using github actions, with a focus on securing your ci cd pipeline against adversaries with contributor access to your github repository. In this blog post, we will provide an overview of github actions, examine various vulnerable scenarios with real world examples, offer clear guidance on securely using error prone features, and introduce an open source tool designed to scan configuration files and flag potential issues.
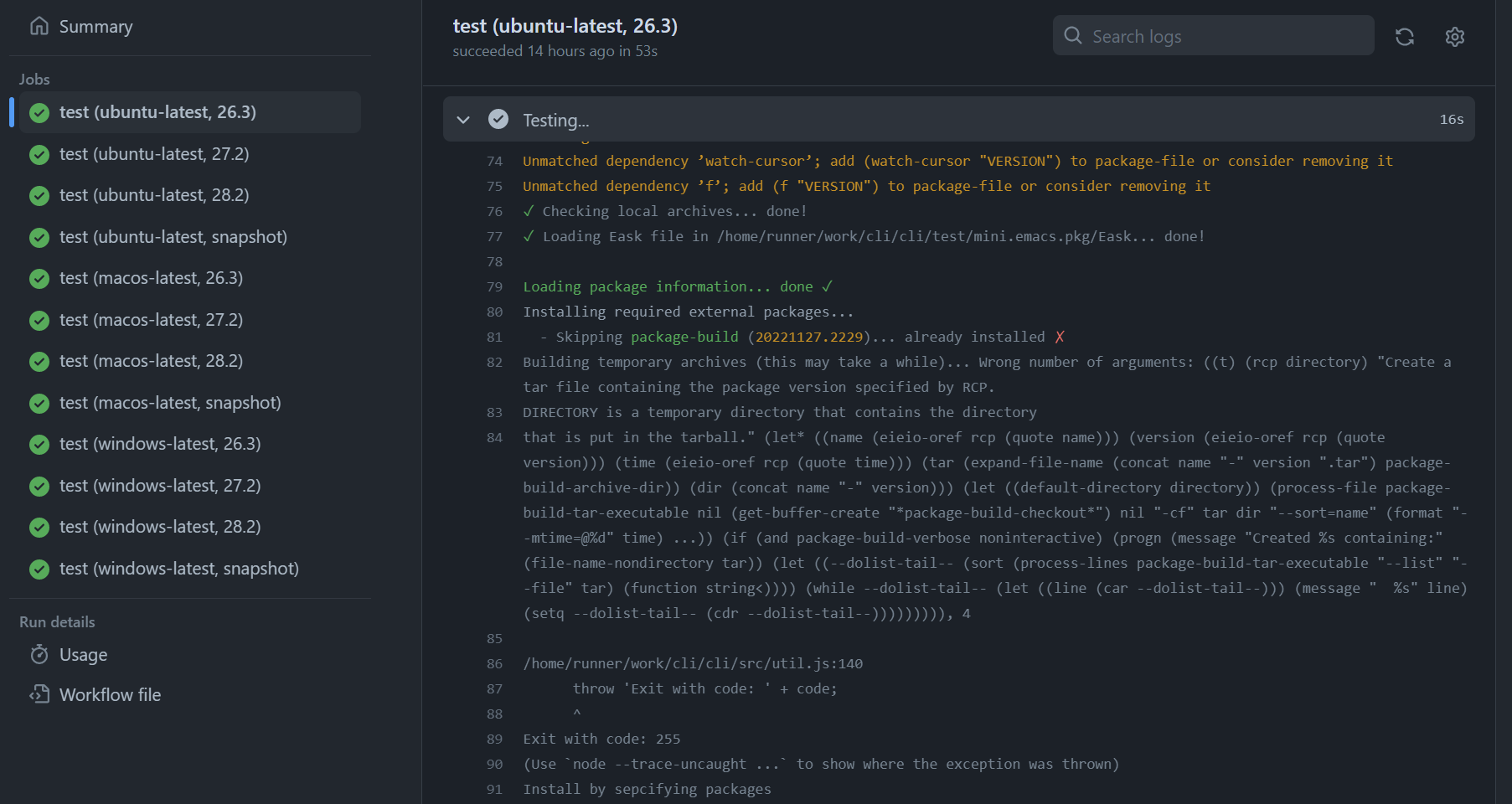
Github Actions Doesn T Stop Even There Is An Error Issue 2308 In this two part series we cover some of the many security considerations when using github actions, with a focus on securing your ci cd pipeline against adversaries with contributor access to your github repository. In this blog post, we will provide an overview of github actions, examine various vulnerable scenarios with real world examples, offer clear guidance on securely using error prone features, and introduce an open source tool designed to scan configuration files and flag potential issues. This guide shows how to mitigate script injection attacks in github actions workflows by using environment variables for untrusted input. script injection occurs when untrusted input is interpolated directly into shell commands, allowing attackers to execute arbitrary code. Using third party github actions introduces risks, especially considering incidents like the tj actions compromise. when referencing third party actions in your workflows, you can either hash pin or use tag based versioning. This blog introduces sonarqube's enhanced analysis capabilities for github actions, designed to proactively identify and remediate security vulnerabilities like command injection and code execution that pose a significant supply chain risk. Cycode discovered critical vulnerabilities in several popular open source projects, each of which can cause a supply chain attack through the ci process. we found the vulnerabilities in misconfigured github actions workflows.
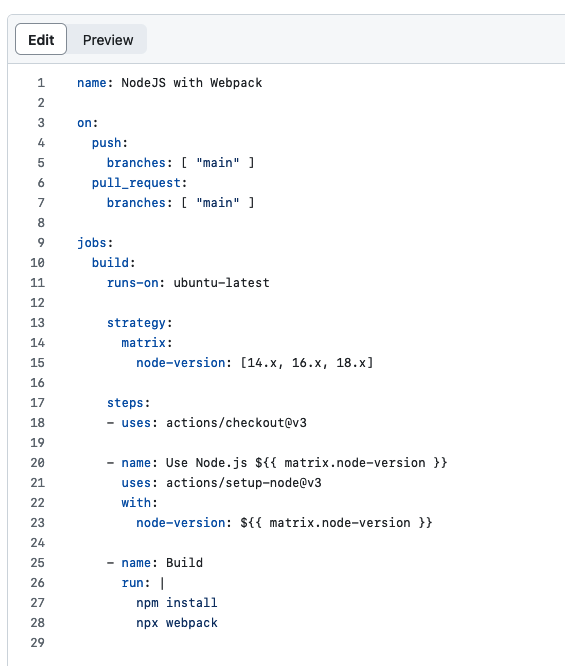
Github Actions For Continuous Deployment This guide shows how to mitigate script injection attacks in github actions workflows by using environment variables for untrusted input. script injection occurs when untrusted input is interpolated directly into shell commands, allowing attackers to execute arbitrary code. Using third party github actions introduces risks, especially considering incidents like the tj actions compromise. when referencing third party actions in your workflows, you can either hash pin or use tag based versioning. This blog introduces sonarqube's enhanced analysis capabilities for github actions, designed to proactively identify and remediate security vulnerabilities like command injection and code execution that pose a significant supply chain risk. Cycode discovered critical vulnerabilities in several popular open source projects, each of which can cause a supply chain attack through the ci process. we found the vulnerabilities in misconfigured github actions workflows.
Github Joshjohanning Github Actions Log Warning Checker Bash Script This blog introduces sonarqube's enhanced analysis capabilities for github actions, designed to proactively identify and remediate security vulnerabilities like command injection and code execution that pose a significant supply chain risk. Cycode discovered critical vulnerabilities in several popular open source projects, each of which can cause a supply chain attack through the ci process. we found the vulnerabilities in misconfigured github actions workflows.
Comments are closed.